- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to disable RSA/SHA1 on Palo alto device for SSH access
- LIVEcommunity
- Discussions
- General Topics
- Re: How to disable RSA/SHA1 on Palo alto device for SSH access
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How to disable RSA/SHA1 on Palo alto device for SSH access
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-20-2021 03:55 PM
We are using OpenSSH v8.2 cannot connect to SSH hosts with SSH Proxy enabled (SSH Decryption).
Testing showing that this is due to the Palo Alto attempting to use RSA with SHA1 which has been removed by OpenSSH in v8.2.
Is there a way we can configure the Palo Alto to disable RSA/SHA1 for SSH?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2021 07:53 AM - edited 07-21-2021 07:57 AM
Hello,
If these hosts are internal, why not bypass decryption for them from trusted hosts/users?
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2021 02:58 AM
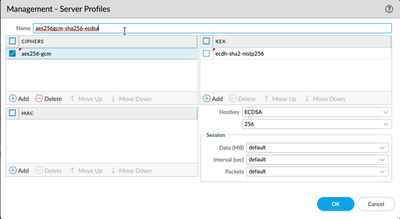
to set the cipher suites only on the management interface, you can use a profile for SSH the set of commands is
> configure # delete deviceconfig system ssh # set deviceconfig system ssh ciphers mgmt aes256-ctr # set deviceconfig system ssh ciphers mgmt aes256-gcm # set deviceconfig system ssh default-hostkey mgmt key-type ECDSA 256 # set deviceconfig system ssh regenerate-hostkeys mgmt key-type ECDSA key-length 256 # set deviceconfig system ssh session-rekey mgmt interval 3600 # set deviceconfig system ssh mac mgmt hmac-sha2-256 # set deviceconfig system ssh mac mgmt hmac-sha2-512 # commit # exit > set ssh service-restart mgmt
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-16-2023 10:54 AM
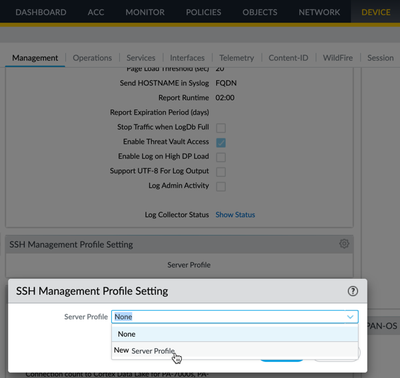
You can also configure the SSH profile directly from the firewall; caveat - you will still need to run the restart command listed above by @Blocker95848
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-16-2023 06:23 PM
Hi @Jatin.Singh ,
That is a great question. It would be nice to disabled protocols on the SSH Proxy tab of the decryption profile, but you can't. The only purpose for SSH Proxy is to be able to detect the ssh-tunnel App-ID. The NGFW does not actually perform content inspection on the decrypted traffic. I would disable it as @OtakarKlier mentioned.
Thanks,
Tom
- 7189 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma Browser for Mobile in Prisma Access Discussions
- Re: How to Post a LIVEcommunity Discussion in General Topics
- analytics bioc tune in Cortex XDR Discussions
- auth override cookie in Globalprotect in GlobalProtect Discussions
- There is now a command: !setIncident tags="<tags to be added>", which by default adds the tags you specify. One can also add the option appendTags=Fal in Cortex XSOAR Discussions