- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Nat type 2 , type 3 with playstation and xbox
- LIVEcommunity
- Discussions
- General Topics
- Re: Nat type 2 , type 3 with playstation and xbox
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Nat type 2 , type 3 with playstation and xbox
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-04-2014 11:29 AM
Hello Everyone,
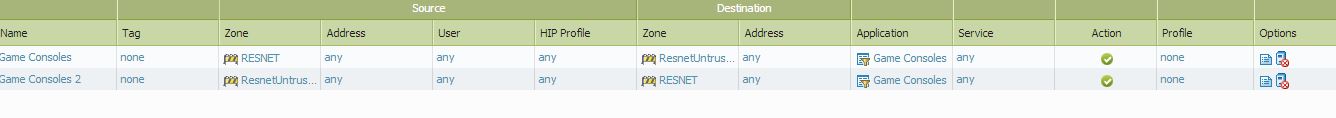
I have a problem with NAT that my end users are reporting that I have not been able to get to the bottom of. I am the administrator of a large University and have multiple buildings for on site housing. 2-3k students live on site. Everything production wise is working fine but I keep having repeat tickets from students asking me to fix the nat type so that they can use playstations and xbox from their dorm rooms. I have been playing with the nat rules but have been unable to get them to change from nat type 3 to 2. I am needing some advise on the issue. It is a very simple setup when dealing with our nat. We source nat our users to a pool of IPs and I have included a screenshot.
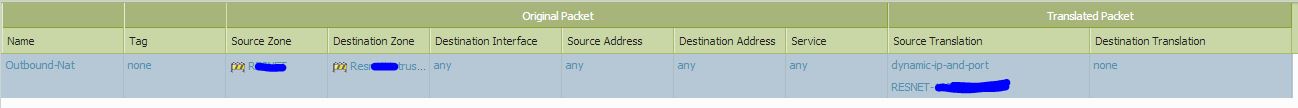
Here is my security policy for the game consoles
I moved a few of the the game users to our Cisco ASA and they go type 2 with no problems but I can not leave them on our asa. it was for testing mainly to see if the PA was the problem.
This is the issue my end users are telling me they would like us to fix.
PS3™ | Internet Connection Test
http://netnix.org/2011/09/06/understanding-ps3-nat/
Anybody else ran into this problem or know what could be the issue because I am not seeing anything that should be making the systems report type 3.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-19-2018 01:27 PM - edited 08-19-2018 01:43 PM
Working with PA support on NAT DIPP oversubscription , We might have stumbled across a solution.
I come from a cisco ASA background and always have used nat pool or many to many NAT. Recently we hit a NAT DIPP problem and as a result I personally had to get PA support to explain to me what was going on. After a detailed explanation and each model has a hardware limitation. PA support advised I shrink (use a /25 or smaller ) or stop using NAT pool and just NAT our customer behind a single IP. At first I was very against this idea but after PA support explained for them this is a best practice and because they are confident in how they block botnet and other malware, I broke down and did it. After a hour I notice a HUGE increase in traffic and as a result we went out and started testing our self. We found that things improved overall Latency / packet loss / etc. Also the warnings about NAT on commit went away about downgrading to 1x oversubscription.
I then had several XBOX and PS4 users redo network test and this resulted in OPEN or TYPE 2 NAT depending on the console.
I will confirm on Monday when I take my own PS4 and XBOX to work to test in the office, but I think avoiding NAT pool oversubscription might have fixed this issue. along with the firewall rules I posted early on to open the traffic to XBOX LIVE and Playstation Network.
Also we use secure works to watch our outgoing traffic and after 48hours and no notifications of botnet / malware from our RESNET. I was really worried going down to smaller subnet or single IP would have made us more vulnerable. I am guessing with us blocking incoming and the PA security features / protections this might be fine, but I am going to wait a full week before I make a final decision.
End result for the NAT was I mapped /22 to /21 for each building WiFi to a single ip. We have a large subnet to use thanks to our ISP. As a result I used a different IP for each building to avoid major oversubscription. for LAN users I am still using 1 to 1 NAT /24 to /24
I will report more as we move along but I think this might be a solution. Welcome to feedback sense this has been a very deep discussions with PA support.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 06:44 AM
@ASU-NetworkTeam I'll definitely be interested to hear the outcome of your tests. I did a ton of troubleshooting with them and I'm not sure we every tried a single IP. I'm actually currently running active/active firewalls and each firewall has access to the same /30 pool of IPs for NAT for each building. It's overkill at this point but I was re-doing our NAT space when we configured these and figured I'd plan in some growth.
I could probably reduce these so each firewall had 1 except if we have a failover scenario the other firewall wouldn't be able to accept the return traffic from the Internet that was originally destined for the downed firewall.
We're looking at a potential hardware upgrade in January and may move to an active/standby deployment. This solution, if it works, might be more feasible to try out at that point.
That being said, I have to say that using our public IP addresses for the students seems to make a lot of it easier. We've even talked about investigating whether we might have enough just to hand out a public IP for everything in ResNet.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 07:01 AM - edited 08-20-2018 07:09 AM
Yes we stop doing the active / active due to budget. PA has some really outrageous pricing for active / active. It basically doubles the bill and not worth it in my opinion. You would be better off upgrading to a more powerful unit and doing active standby for budget reasons from what I have seen.
We have Active Standby and use LACP to a cisco 4500X routers. It works great and you also have the option to have the standby unit in no shut to keep routing protocol active if needed for faster fail over. Unless you have a need for the active / active because of usage, you are fine changing to active / passive. You know your network better than anyone so don’t just take my word, but it is worth researching it.
We have also found that the newer units are much more powerful than our older 5020 and the renewals are much LESS but the upfront purchase cost is ridiculous. I guess PA going to make $$$ somehow. You would think for the amount of money we pay we could at least get USA support 100%. I get so sick of calling and spending an hour or more getting passed the language barrier and then the technical explanation, or someone in India who really does not care and trying to just get the ticket closed.
So I test everything this morning XBOX and ps4. Xbox reports OPEN and ps4 is type 2 and working. The students are happy so far. Also issues with facetime quality and other things are gone. Using NAT pool apparently is a bad idea in palo alto world.
So yes down to two options. Route public WAN addresses to the clients or NAT each subnet to a different WAN address to avoid oversubscription.
I will post screenshots here in a few of what we did
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 07:17 AM
Wow your setup sounds a lot llike mine. We've got two 5060 unit currently with two Cisco 4500-X in VSS to serve as routers for some of the networks and as fiber aggregation since the 5060s are limited on 10g port count.
We've actually had a lot of issues with the 4500-X stack, mainly because our current (and admittedly old) network design involves using policy based routing to push all traffic through the firewall for security and access control. We're also using VRF... VRF + PBR + no ip redirects = PBR failing. Cisco says the config isn't supported on that platform when using VRFs...
Our active/active was mostly for having dual homed 10gb connectivity to AREON. The former Network Services manager wanted to make as much use of the firewalls as possible... I agree although we honestly don't push enough traffic to saturate even one of those 10g connections. If we go with the 5200 series we were looking at one that will do at least 20gb with app and threat turned on and that would pretty much eliminate the last reason not to go with active/standby. It's going to simply our network design too as I've had all sorts of issues trying to get ECMP working with PBR on our older Cisco hardware.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 07:33 AM
I updated our cisco 4500X to the latest gold star and gained route map ability and started using that. In the latest gold star release you do not need a enterprise license to do a lot of things.
Our setup used to look like yours but I got sick of it and change lots of it to route maps and ACL because troubleshooting turned into a pain in the rear and also TAC kept saying the same thing to us. SIMPLE is better. You should really look at Nessus and do netflows etc to it for security and scans. Take some of the load off that FW and save $$$. Also we use packetfence for 802.1X with a Suricata box we mirror all traffic to. They work together and trigger violations to keep problem users off the network. also it is free.... we are also going to intergrate nessus into our packetfence security once we get the licenses for nesses to do end user devices.
We are looking to change from 5020 to 3260 for budget reasons. the renewal is 60% less a year
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 07:39 AM - edited 08-20-2018 07:41 AM
We just went to Cisco Live and are also currently evaluating what an SDA deployment would look like and cost. That would move a lot of that off the firewall and back down in to the core where it belongs.
I'm also interested in their Stealthwatch product... from my understanding it seems to have the ability to do decrypted traffic anlaysis. It isn't a firewall so it won't block things it detects but I think it can hook in to a NAC solution to disable ports.
Part of the issue for us doing Netflow, and this would definitely be an issue with Stealthwatch and SDA, is that we have a lot of 2960-X switches on campus and they only do Netflow Lite.
It's the diet coke of Netflow... just one calorie, not Netflow enough.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 07:41 AM
I was at cisco Live as well. we might have been in the same room.
Those solutions are NOT cheap we got them quoted and was like WOW!
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-20-2018 07:44 AM
Yeah that's what I'm afraid of. Our SE is putting something together for us and we would almost definitely have to do a phased approach. They were saying at Cisco Live that it's a journey for sure.
What has sold us on it so far is the troubleshooting and monitoring. DNA Center has come a long way from Prime Infrastructure and it looks like it would help tremendously with support in our BYOD environments, including ResNet.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-21-2018 07:12 AM
Hello,
Can someone tell me how many PlayStation devices can run behind such a UPnP router? Does anyone have experiance with such environment?
We have a gaming office which has at least 20 PS4´s. Should this work with any UPnP router?
Regards,
Andrej
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2018 12:45 PM
@ASU-NetworkTeam I was looking at this on my PS4 at home and noticed on my PA220 lab unit that the NAT type still shows as Type 3 Strict. My configuraton at home doesn't use a NAT pool.. it should be only using the single IPv4 address my ISP provides me. I believe I have it configured for DIPP.
Anything else you guys are doing that might be leading to the better NAT types? Did you mentioned you disabled oversubscription?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-05-2019 10:51 AM - edited 09-05-2019 10:53 AM
@ASU-NetworkTeam
@ASU-NetworkTeam wrote:Yes we stop doing the active / active due to budget. PA has some really outrageous pricing for active / active. It basically doubles the bill and not worth it in my opinion. You would be better off upgrading to a more powerful unit and doing active standby for budget reasons from what I have seen.
We have Active Standby and use LACP to a cisco 4500X routers. It works great and you also have the option to have the standby unit in no shut to keep routing protocol active if needed for faster fail over. Unless you have a need for the active / active because of usage, you are fine changing to active / passive. You know your network better than anyone so don’t just take my word, but it is worth researching it.
We have also found that the newer units are much more powerful than our older 5020 and the renewals are much LESS but the upfront purchase cost is ridiculous. I guess PA going to make $$$ somehow. You would think for the amount of money we pay we could at least get USA support 100%. I get so sick of calling and spending an hour or more getting passed the language barrier and then the technical explanation, or someone in India who really does not care and trying to just get the ticket closed.
So I test everything this morning XBOX and ps4. Xbox reports OPEN and ps4 is type 2 and working. The students are happy so far. Also issues with facetime quality and other things are gone. Using NAT pool apparently is a bad idea in palo alto world.
So yes down to two options. Route public WAN addresses to the clients or NAT each subnet to a different WAN address to avoid oversubscription.
I will post screenshots here in a few of what we did
I'd be interested to find out if you're still running this solution the same way a year later. I've recently joined a team, and the current solution has been to set up a 1-to-1 private to public NAT per previous recommendations from Palo Alto on the topic. However, I don't see this as a long term solution as our userbase grows, and this is the first I've seen of a potential alternative solution. Additionally, similar issues present themselves with students who are PC gaming, and mapping them this way is not ideal at best. If NAT to a single IP for this special use case could resolve the issue, I'd see that as a usable approach.
Also, Are you still blocking all inbound with good results? Everywhere else I've seen says to open certain ranges of inbound ports but I've been dubious of how necessary it is.
Thanks for sharing this info! Really hope to find out some more about it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2019 07:35 AM
Just found this topic as work in a University, and have started getting the same enquiries from students wanting to use Nintendo Switch. Our dynamic IP & port setup is resulting in a NAT Type D on their consoles. I had made the network dual-stack, and had optimistically hoped the gaming networks would be using IPv6 and thus avoid this issue, but it seems not...
Will probably go with the static NAT IP per private subnet idea and see how that goes.
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2019 08:30 AM
@aceandy79I would be curious what your results are. I have a test unit at home and while I can't really set it up as true static NAT since I get a dynamic IP from my service provider, it is still only one IP it is using. I still see strict NAT on my home gaming devices.
Granted, it's entirely possible their port algorithms are set up differently for a true static IP configuration vs a Dynamic IP even though you're only ever getting the same IP.
I'd also encourage any Higher Ed or other entity supporting multiplayer gaming to contact your Palo Alto sales team and look into supporting Feature Request 7654. I put this in about 2 years ago asking for some DIPP NAT option to implement something like "sticky NAT" and/or to implement something closer to Cisco's ASA implementation for Port Address Translation (PAT). I was told by our sales team that these Feature Requests gain priority based on the number of customers that express the need for the specific feature.
There may be a better option than the one outlined in that specific FR but, one way or the other, I feel like we as a community can get together and express interest in something to get this fixed that doesn't involve using another vendor's product for gaming networks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2022 02:25 PM
Worked for me at home through a lab 220. Thanks for the info! The key is the static NAT rule, but I did not need to have bi-directional enabled for it to work. Luckily I have a static IP from my provider.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-03-2022 11:59 AM
Almost another year later (Nov 2022) and this still appears to be the only answer/solution to this problem, which seems a little crazy to me. Especially since like others here, the outside/untrust IP is dynamically assigned, but you can only enter a fixed IP for the translation which will require manual intervention to "correct" in the event of IP reassignment (and I imagine cause the ISP to see duplicate IP issues).
- 42869 Views
- 35 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- LGTV and Netflix bugs out when going through Palo Alto in General Topics
- University Students Receiving (HTTP Status Code : 416) (CE-40862-0) On Playstation devices in General Topics
- False positive URL filtering in VirusTotal
- Configure a static 1-to-1 destination NAT policy in General Topics
- Can't access management when PA200 is in line in General Topics




