- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Network blocking and detecting capabilities in case of similar abnormal symptoms traffic
- LIVEcommunity
- Discussions
- General Topics
- RE: Network blocking and detecting capabilities in case of similar abnormal symptoms traffic
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Network blocking and detecting capabilities in case of similar abnormal symptoms traffic
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-08-2023 07:48 PM
Hello all,
Hope you are doing well.
Our customer who is using PA3220 experienced external public IP blockage due to abnormal symptoms traffic.
Upon investigation, it was found that a test Linux server installed internally attempted SSH brute force attacks against an unspecified number of external public IPs.
We would like to know if the PaloAlto PA device has any network blocking and detecting capabilities in case of similar abnormal symptoms traffic.
Although it seems that PaloAlto can sufficiently detect abnormal traffic if one client attempts to SSH connect (attack) to an unspecified number of others, we cannot find any logs or alarms related to the symptoms.
Thanks,
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-09-2023 01:44 AM
Hi @JoHyeonJae ,
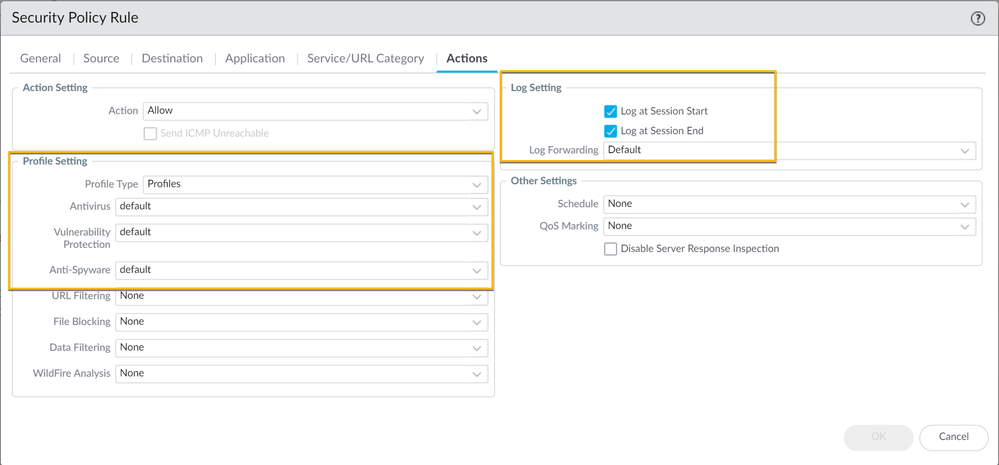
To enforce protection against brute force attacks make sure to attach the Vulnerability Protection profile to a Security policy rule.
See Set Up Antivirus, Anti-Spyware, and Vulnerability Protection
You can have all the security profiles in the world... if you don't apply them to your policy they won't protect you (also make sure that you log appropriately).
Kind regards,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-09-2023 05:45 PM
@kiwi
Thank you for your response. The customer is already using the Vulnerability Protection Profile. In this case, could you please advise what actions need to be taken for blocking?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-09-2023 07:14 PM
I have a few questions while setting up the Vulnerability Protection Rule.
What does the Duration value mean in the Vulnerability Protection Rule, and what criteria are used to detect and block/detect abnormal traffic?
If the Duration is set to 3600, does the PA device analyze all traffic generated by the Vulnerability Protection Profile during the one-hour period and block the Source IP suspected of brute-force attacks?
Can you explain what criteria the PA device uses to identify traffic suspected of brute-force attacks?
Thanks,
- 2911 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Network blocking and detecting capabilities in case of similar abnormal symptoms traffic in General Topics
- Cortex XDR PoC Lab ft. CVE-2021-3560 in Cortex XDR Discussions
- Is prisma have the capability to detect potential attack in Prisma Cloud Discussions
- APP-ID detection capabilities in IP64 tunnels in General Topics
- Detecting Botnets, Virus and Vulnerabilities after migration to 4.0.1 in General Topics