- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Upgrading site-to-site IPSec tunnel tunnel tonight - no PRF option
- LIVEcommunity
- Discussions
- General Topics
- Upgrading site-to-site IPSec tunnel tunnel tonight - no PRF option
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-07-2022 12:07 PM - edited 02-07-2022 12:22 PM
We're upgrading a VPN tunnel to IKEv2 between a Cisco FTD 2140 and a PA-850 running 9.1. What I've noticed is that the PA doesn't have an option for PRF on phase 1. Does the PA automatically make this the same as the integrity algorithm? Is there some other way to configure this?
Thank you.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-08-2022 09:57 AM
FWIW, PRF was set to SHA256 on the Cisco FTD, and the tunnel negotiated with no problems. It was IKEv1 previously, so the transition went smoothly. Steve, thanks for your input.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-08-2022 07:51 AM
From a simplicity perspective, the PRF is done internally within the PANW.
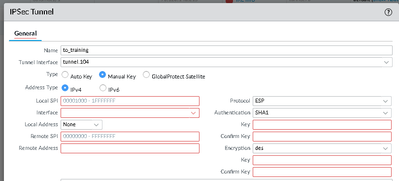
When creating the actual tunnel (IPSec tunnel menu item on the PANW), you can choose Manual Key, vs Auto Key
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-08-2022 09:57 AM
FWIW, PRF was set to SHA256 on the Cisco FTD, and the tunnel negotiated with no problems. It was IKEv1 previously, so the transition went smoothly. Steve, thanks for your input.
- 1 accepted solution
- 12701 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!