- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Using Users instead of Groups in Policies - Help please
- LIVEcommunity
- Discussions
- General Topics
- Re: Using Users instead of Groups in Policies - Help please
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2016 10:08 AM
Hello all,
I'm new to PA but I'm really enjoying it...anyway, I've read everything I could find aboud group mappings, and one very good link is https://live.paloaltonetworks.com/t5/Featured-Articles/Getting-Started-User-ID/ta-p/69321 .. but it only show how to use a group in a policy.
Is it possible to use a "user" instead of a group in a policy? It seems I can only manage to retreive group info (user-id ip mappings are working through an Agent).
Thank you
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-25-2016 09:33 AM
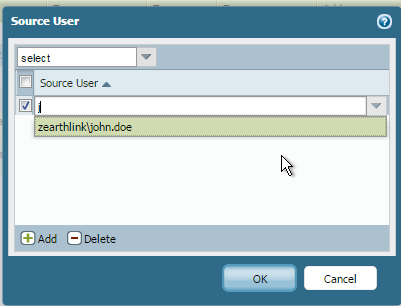
Ok, I feel ashamed now..... It was working all along, I just needed to start typing the username for it to recognize because by default the users don't appear on the list :|:|:|:|:| Not really intuitive 😕 .. days lost!!!
I really appreciated your help on this guys, sorry for the wasted time.
Best regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2016 11:44 AM
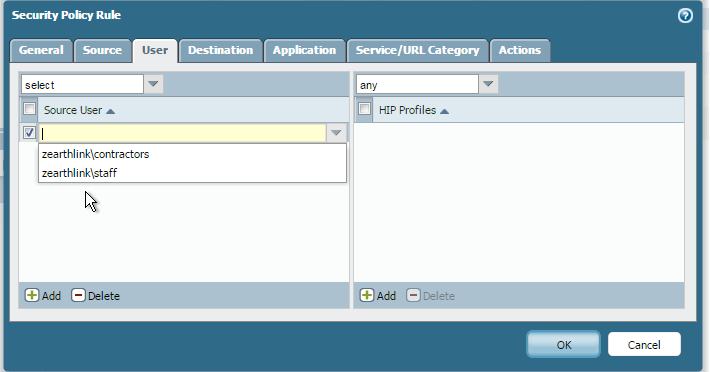
Yes, I'm able to build a security policy using a specific user ID and not just a security group.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2016 11:51 AM
Thank you for your reply Brandon, can you please elaborate a bit more on how you did it? Am I missing something ? On the Staff group I have users inside (Staff1, etc)
Thank you in advance
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2016 12:47 PM
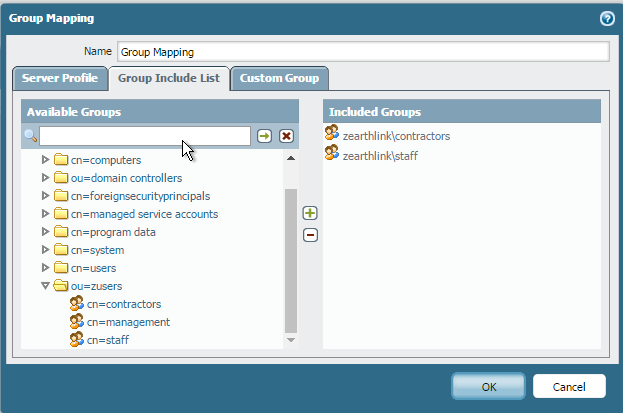
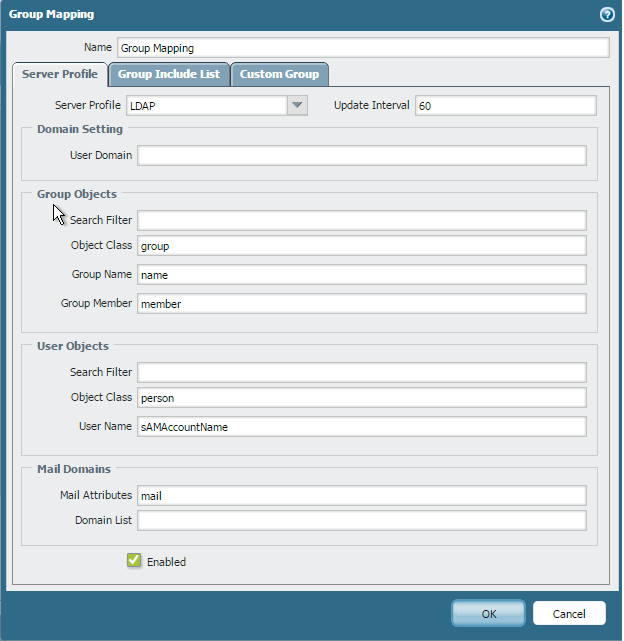
Generally speaking you would want to include the user domain in your Server Profile, it looks like you would have zearthlink. Try giving that a shot and see if it gives you options to your user list; it may also be a good idea to verify that you actually have the right permissions setup, PAs require more permissions then most server admins would feel is necessary so often times I see them not actually have every permission that they need.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2016 01:25 PM
Yeah like @BPry said, I didn't have to do it from the group mapping, it's all probably because of a lack of permissions on the account you're using in the Palo to query AD. When I create a new security rule I'm able to just enumerate the domain and find the correct user accounts that are necessary.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-24-2016 01:26 PM
Thank you Bpry for your comment. Unfortunately it didn't sort the issue out.
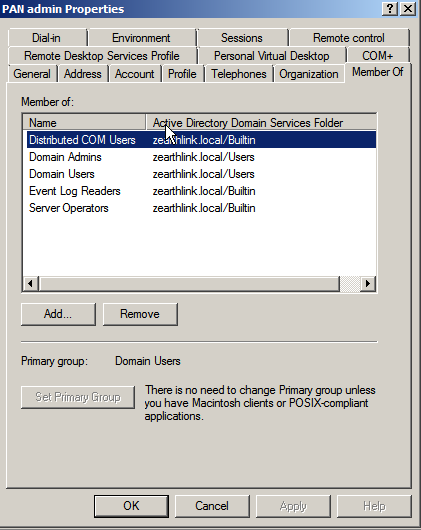
As for the account permissions, its the same I use for the user agent:
I even already tried with the "administrator" account (it's only a lab so not really a concern 🙂 ) without success.
If anyone have another idea please share it
Thank you in advance
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-25-2016 08:20 AM
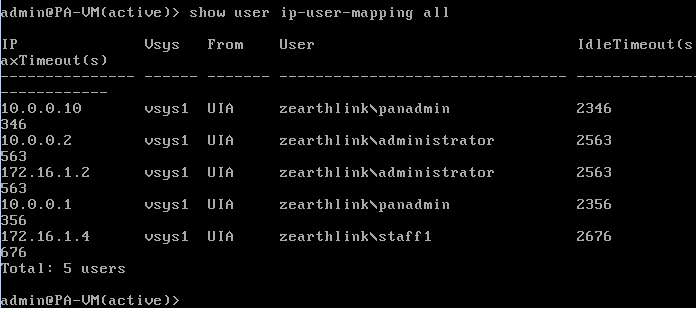
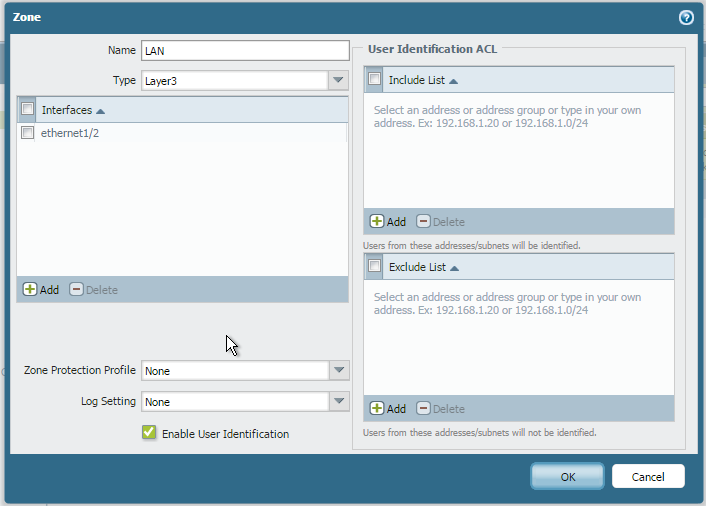
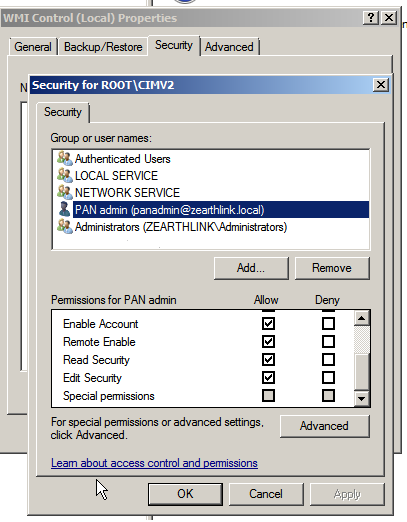
It really sounds like you just don't have something configured properly on the AD side of things. Have you modified the properties on CIMV2 in WIM, have you actually enabled User Identification on the actual zone (this would explain why your accounts listed can't be used)? If you run show user ip-user-mapping all do you actually get anything listed or does nothing show up? You could verify well have multiple issues here that are masquerading as one
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-25-2016 09:09 AM
Hello Bpry,
thank you for getting back to me again. I have user identification enabled on LAN, gave FULL permissions to the panadmin account and even tried the administrator account:
I can see the user logged (staff1) and it's ip address but still can't filter by users, just groups 😕
Thank you in advance
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-25-2016 09:33 AM
Ok, I feel ashamed now..... It was working all along, I just needed to start typing the username for it to recognize because by default the users don't appear on the list :|:|:|:|:| Not really intuitive 😕 .. days lost!!!
I really appreciated your help on this guys, sorry for the wasted time.
Best regards
- 1 accepted solution
- 5113 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Alto Site to Site VPN ipsec tunnel up but unable to ping Source to destination in Next-Generation Firewall Discussions
- Prisma Asset Type assignment to a created Prisma policy in Cortex Cloud Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Enforce GlobalProtect Access Based on Microsoft Intune Compliance Status in GlobalProtect Discussions
- EDL Capacity Reached but Lists Show Empty / Default Entry (0.0.0.0/32) – Panorama Multi-VSYS Setup Post: in General Topics