- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Web-gui access with no secure certificate.
- LIVEcommunity
- Discussions
- General Topics
- Re: Web-gui access with no secure certificate.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-03-2019 05:20 PM
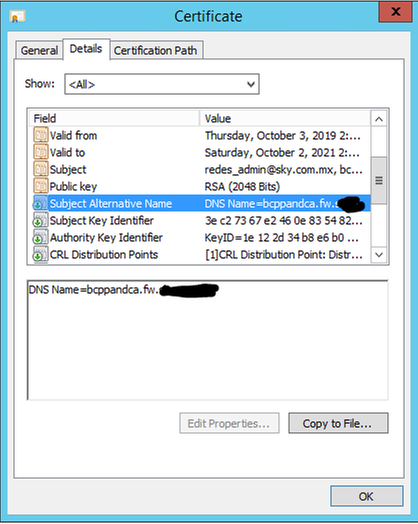
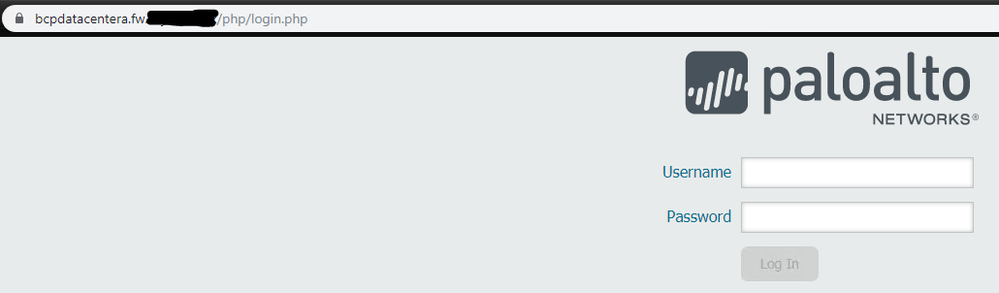
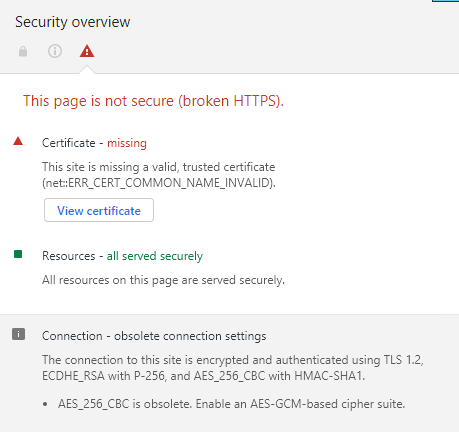
I access via GUI from Chrome and observe that the connection is not secure.
I created the certificate for the firewall, but Chrome keeps saying that my connection is not secure.
How can I solve this problem if the AC I have is internal to the company?
Is there any way to generate certificates with AES-GCM?
in chrome, the following legend appears to me.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-04-2019 01:10 AM
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-04-2019 01:10 AM
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-04-2019 08:30 AM
Just enter an alternative name, I'll try to place the same FQDN in the alternative name.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-04-2019 02:33 PM
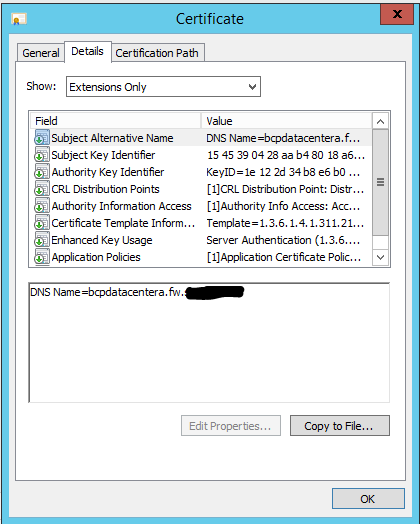
Change the alternative name and chrome already recognized the certificate as valid.
Thanks for the support.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-06-2019 07:02 AM
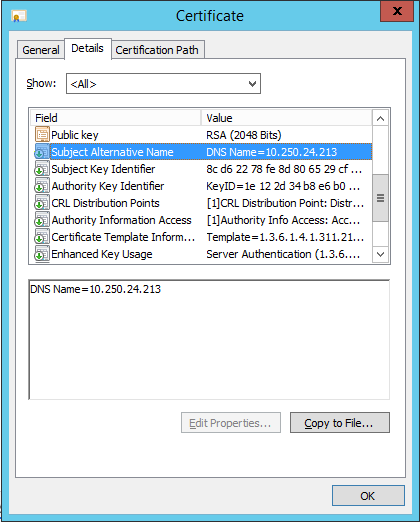
even if you put ip address in subject alternative name it works.
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-07-2019 10:28 AM
I'll Perform the test as indicated, the firewall management IP is a private IP even if I will try.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-21-2019 11:05 AM
Create the certificate by placing the device IP in the SAN and it does not work..
It only works by placing the same name on both the CN and the SAN.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-21-2019 12:46 PM
When creating SAN entries, you always put the common name as a SAN entry as well.
If you add the IP address as a SAN entry, make sure the type is IP Address (v4) instead of DNS name.
When I create certificates for devices like a PA, I do as shown below. The cert will be valid if you access with FQDN, short name or IP.
Common Name = devicename.domain.com
SAN:
DNS= devicename.domain.com
DNS= devicename
IP Address (v4) = IP Address
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2022 06:18 AM
Hi Team,
I was able to solve the issue by using below KB for adding SAN name in certificate
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000CluVCAS
Generated Self-Signed certificate in PA,then in certificate attributes add hostname and IP same as management address.
Here hostname denotes as SAN name (Subject Alternative Name)
Attach certificate to TLS Profile and that TLS profile to SSL/TLS management interface to login in GUI via TLS1.1/2
Attached reference screenshot
- 1 accepted solution
- 20255 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- What certificate to use for Palo Alto-provided EDL validation in General Topics
- Can AI Access Security actually inspect RESPONSES generated by AI?? in AI Access Security Discussions
- New cert GP cert prompt for people testing Yubikeys for windows logon in GlobalProtect Discussions
- New Certifications: Next Gen Firewall Engineer and Network Security Professional in General Topics
- How do I access init-cfg.txt in VM-Series in the Public Cloud