- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect On-Demand using authentication profile and user certificate from PKI on gateway
- LIVEcommunity
- Discussions
- Network Security
- GlobalProtect Discussions
- GlobalProtect On-Demand using authentication profile and user certificate from PKI on gateway
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-22-2021 11:24 AM
I'm trying to setup a GlobalProtect On-Demand environment.
The portal uses an LDAP server profile for authentication and has been validated to be working fine.
I intend to configure the gateway to use a combination of RADIUS and certificate profile to authenticate. I've confirmed that authentication works without the certificate profile.
My understanding is that certificate based authentication for the "on-demand" mode works only if the certificates are user certificates (i.e. installed in the user store).
I've a PKI infrastructure in the environment that is pushing out certificates to the users. I do not intend to go down the SCEP configuration for this deployment.
So far I've not been successful to get certificate profile.
I'm greeted by the "Required client certificate not found" error.
I've tried to play with different options on the certificate profile like subject, subject alt-name, principal name, email, etc.
FYI... I have the PKI root CA and intermediate CAs already included in my certificate profile.
I wanted to know if anyone has this successfully working in this fashion using "On-demand" mode.
- What certificate fields or options did you use?
- What certificate profile options did you leverage?
- Any interesting scenarios you ran in your deployment?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2021 03:27 PM
Just so that I provide closure to this discussion. I managed to get this rolled out and fix the issues that I was having.
Here is what I learned during my deployment and troubleshooting:
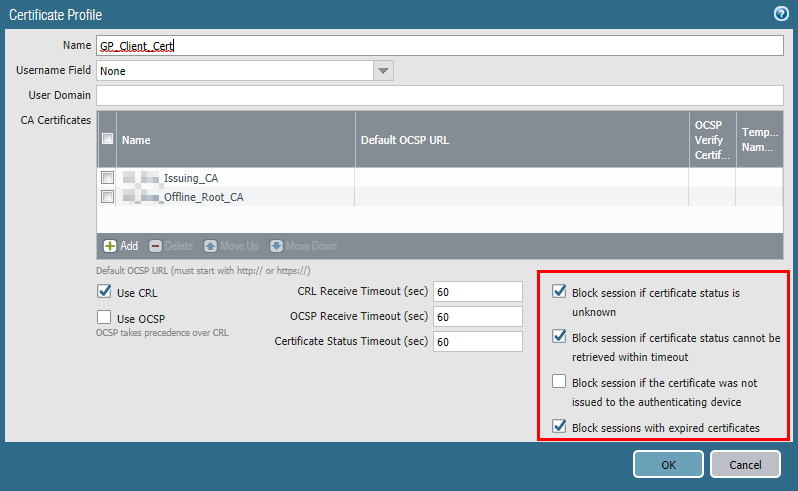
- When using user certificate along with an authentication profile; you can leave the username field to "none" on the certificate profile.
- "Required client certificate not found" was the error that got me stuck. I was using the certificate profile to verify the certificate-status:
- After long hours of detailed investigation I discovered that this was due to CRL verification failures. I hadn't validated the firewalls reachability to query the CRL that it was reading off the presented certificates. This lead to the discovery that the firewalls were configured with external DNS servers and that CRL verification attempts were being made against an internal FQDN. I updated the DNS servers on the firewall to lookup against internal DNS servers and everything is working like a charm!
Hope someone else finds this useful when they run into a similar fit!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-22-2021 01:37 PM
We are using the Prelogon and then on demand for GP.
We are using Machine cert for Client Authentication using prelogon and then on demand.
We do have our Internal PKI server.
We have imported the Intermediate cert from the PC to the PA.
PA already has Root CA.
!>Our cert profile has Root and Intermediate certs.
2>For Cert for VPN it has CN field.
3>You need to make sure cert which you have on PC make sure import its Root and Intermediate to the PA.
Regards
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-22-2021 01:47 PM
@MP18 Thanks for your response.
I've had success in the past deploying machine certificates for authentication. But, this time I'm specifically trying to get user certificate authentication to work with just the on-demand mode.
During my research, I came across the PAN KB article (Basic GlobalProtect Configuration with Pre-logon) that hints that this is possible.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-22-2021 02:31 PM
Yes as per that link it is possible.
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2021 03:27 PM
Just so that I provide closure to this discussion. I managed to get this rolled out and fix the issues that I was having.
Here is what I learned during my deployment and troubleshooting:
- When using user certificate along with an authentication profile; you can leave the username field to "none" on the certificate profile.
- "Required client certificate not found" was the error that got me stuck. I was using the certificate profile to verify the certificate-status:
- After long hours of detailed investigation I discovered that this was due to CRL verification failures. I hadn't validated the firewalls reachability to query the CRL that it was reading off the presented certificates. This lead to the discovery that the firewalls were configured with external DNS servers and that CRL verification attempts were being made against an internal FQDN. I updated the DNS servers on the firewall to lookup against internal DNS servers and everything is working like a charm!
Hope someone else finds this useful when they run into a similar fit!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-30-2021 10:35 PM
Thanks for updating the Community.
Regards
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2024 09:57 AM
thank you, very useful to know
- 1 accepted solution
- 7128 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- Global Protect is having issues with newer MACOS version. in Next-Generation Firewall Discussions
- Global Protect Internal Detection in GlobalProtect Discussions
- Palo Alto Global Protect clients failing to connect intermittently in GlobalProtect Discussions