- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to block malicious IP to connect GlobalProtec (Prisma Access)
- LIVEcommunity
- Discussions
- Secure Access Service Edge
- Prisma Access Discussions
- How to block malicious IP to connect GlobalProtec (Prisma Access)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2023 08:32 AM
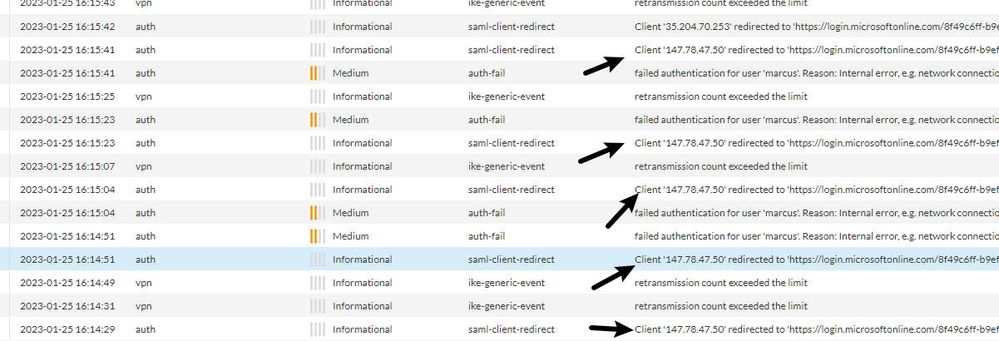
How do I block malicious IP of connecting to GlobalProtec (Prisma Access), in logs I see many attempts at login on VPN:
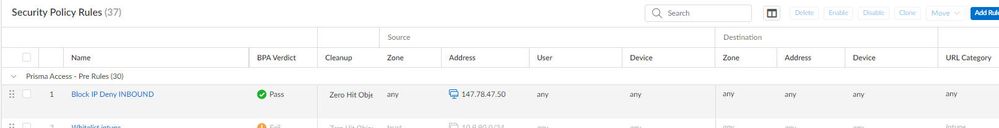
I created a Security Police but I was unsuccessful
I opened the ticket with Palo Alto but I believe you don't have much knowledge in Prisma Access to solve the problem.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2023 12:37 PM - edited 01-31-2023 01:03 PM
You can block the "panos-global-protect " application in the security policy but keep in mind that it depends on ssl. You can check the apps at https://applipedia.paloaltonetworks.com/ . Also from your logs I see that probably your Palo alto is intergrated with SAML with Azure AD and you can try to block the IP address also on the Azure AD using conditional Access.
Also do a policy test from the panorama to see if you are matching the correct rule https://docs.paloaltonetworks.com/panorama/10-1/panorama-admin/troubleshooting/test-policy-match-and...
It is interesting if you are using globalprotect agent or clientless vpn or Prisma Access in proxy mode where you see this issue.
Still just in case check for commit issues to the Prisma Access from the panorama https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PMb2CAG as maybe Pre rule is not commited the Virtual Firewalls that make up Prisma Access but still for some checks the support can actually connect to the firewalls in the cloud so push them.
Also there could be a proxy so Prisma Acess may not see the real ip and then you may enable "Trust XFF" if you are doing SSL decryption.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2023 12:37 PM - edited 01-31-2023 01:03 PM
You can block the "panos-global-protect " application in the security policy but keep in mind that it depends on ssl. You can check the apps at https://applipedia.paloaltonetworks.com/ . Also from your logs I see that probably your Palo alto is intergrated with SAML with Azure AD and you can try to block the IP address also on the Azure AD using conditional Access.
Also do a policy test from the panorama to see if you are matching the correct rule https://docs.paloaltonetworks.com/panorama/10-1/panorama-admin/troubleshooting/test-policy-match-and...
It is interesting if you are using globalprotect agent or clientless vpn or Prisma Access in proxy mode where you see this issue.
Still just in case check for commit issues to the Prisma Access from the panorama https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PMb2CAG as maybe Pre rule is not commited the Virtual Firewalls that make up Prisma Access but still for some checks the support can actually connect to the firewalls in the cloud so push them.
Also there could be a proxy so Prisma Acess may not see the real ip and then you may enable "Trust XFF" if you are doing SSL decryption.
- 1 accepted solution
- 4080 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!