- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Default Action for SQL Injection Attacks
- LIVEcommunity
- Discussions
- Cloud Delivered Security Services
- Threat & Vulnerability
- Default Action for SQL Injection Attacks
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2018 05:09 AM
Following a sudden spike in SQLMap threats, I was looking at the default action for SQL injection threats and I noticed that it is is only an "alert" which seems odd for that kind of attack. Has anyone looked deeper into this and/or changed the action and is there a reason for this not being a reset/drop action?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-22-2018 10:04 AM
Hello,
I would recommend setting the medium to also reset or block. There are going to be some exceptions, at least there are in my environemtn so I had to create special exception cases for them.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-19-2018 01:45 PM
Hello,
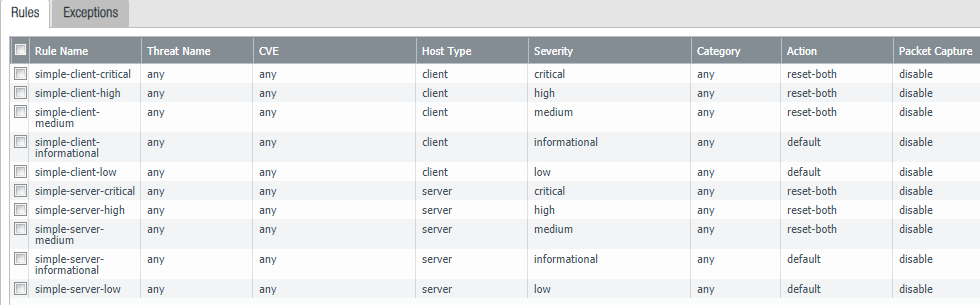
While it is by deafult sert to alert, I found its best to block threats by Severity. As you can see by the picture, this Vulnerability Protection Profile, when added to a Policy, will reset the traffic so it cannot cause any damage:
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-22-2018 04:16 AM
Hi,
We already reset Critical and high, but use the PAN default below that so the difference between your profile and ours is really just that you extend that down to medium.
I see you also use the default action for low and info which is probably for the same reason we do - some of the low and info threats are by default blocked which we found odd. The PAN severity classification seems a bit weird which is why I was asking if anyone knew a reason why SQL injection was only an alert by default - if the detection is robust I would expect this to be a block by default.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-22-2018 10:04 AM
Hello,
I would recommend setting the medium to also reset or block. There are going to be some exceptions, at least there are in my environemtn so I had to create special exception cases for them.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2018 02:47 AM
OK thanks, I will look a bit closer at what other medium level threats we are seeing, with a view to doing that.
Many thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2018 02:45 PM - edited 11-02-2018 02:47 PM
Leaving medium to default allows so much bad stuff through.
I have even low severety set to reset-both with only 3 manual exeptions in there for traffic sourcinf from wan and handful more for internal traffic.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-05-2018 01:28 AM
Thanks, I don't think I will go that far just yet, but have put medium to reset-both for spyware and vulnerabilities.
- 1 accepted solution
- 23020 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- CVE Mapping for Zero-day Exploits: Enhancement in Threat content release notes and Cloud reports in Advanced Threat Prevention Discussions
- How to enable signature of Unique threat id in Advanced Threat Prevention Discussions
- Container scanning(Basic question) in Advanced Threat Prevention Discussions
- Best practice stopping attacks from outside in Advanced Threat Prevention Discussions
- How to choose signature for sql-injection? in Advanced Threat Prevention Discussions



