- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
deafult decryption
- LIVEcommunity
- Community Legacy Content
- Automation / API
- Automation/API Discussions
- Re: deafult decryption
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
deafult decryption
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2014 02:15 AM
Hi,
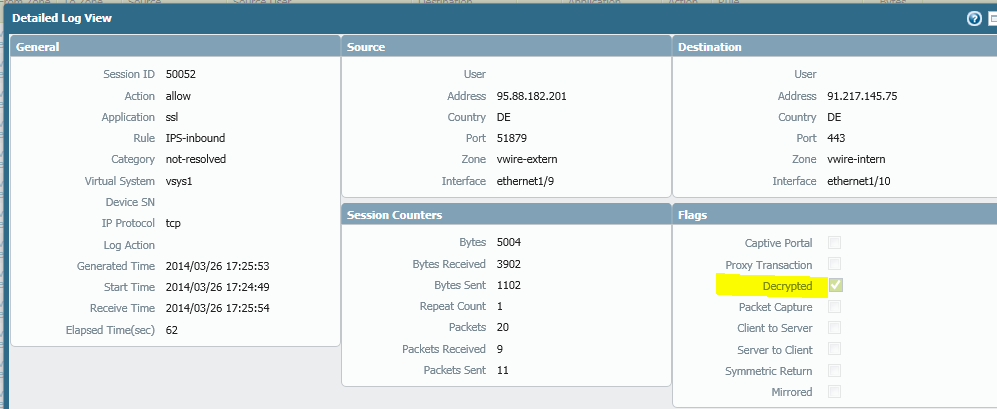
I run a HA-cluster of PA-5020 PAN OS 5.0.10
I've just noticed that since I've upgraded from 5.0.8 to 5.0.10 a specific traffic was identified as web-browsing instead of as before SSL.
It seems that traffic identified as web-browsing over port TCP 443 always is decrypted. Is this so? The only way I've managed to control this is by a Application Override rule to identify the taffic as a other app then web-browsing.
How can I control what is being decrypted and not other than by my decryption rules?
BR // Per
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-26-2014 09:17 AM
Dear per.markgren,
The PaloAlto will only decrypt traffic based on the decryption policies. web-browsing is not decrypted by default, this can only be because you have a decryption policy in place.
If you do not want to decrypt certain traffic just create a rule for it under the decryption policies
ex: source: xxx / destination: any / service: http / action = NO-DECRYPT
Put that rule at the top, and this traffic will no longer be decrypted.
- 2508 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Ansible PFX Cert Upload not adding key in Automation/API Discussions
- Ansible panos_decryption_rule - not working with ssl-inbound-inspection in Automation/API Discussions
- Automate importing of certificate in broken certificate chain in Automation/API Discussions
- Do not decrypt SSL traffic for Office 365 and ZOOM in Automation/API Discussions
- High MP CPU : PHP Process : API in Automation/API Discussions