
- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Palo Alto Networks continues to push boundaries in cloud-delivered security with the introduction of Prisma Access 4.2. This impressive release stands as the industry's sole ZTNA 2.0 security solution presented within a seamless, all-in-one package. In this fresh update, we're once again strengthening our cutting-edge ZTNA 2.0 security with an array of exciting new features and improvements:
We're rolling out credential phishing features to all Prisma Access deployments. There are three methods i.e Group mapping, IP mapping and domain credential filter with the domain credential filter only applicable for RN deployments.
To learn more about the new Credential Phishing feature in Prisma Access 4.2, please check out the links below:
To shield against the increasing threat of sensitive data leakage to AI applications and APIs we're thrilled to introduce a fresh arsenal of capabilities. These extend to ChatGPT and other AI apps and are part our Next-Generation CASB solution. Here's what you can expect:
We're bringing you comprehensive visibility into every nook and cranny of SaaS activity. This means you'll have your finger on the pulse of all usage, including when employees venture into the realm of new and cutting-edge generative AI apps such as ChatGPT that can put data at risk.
 SaaS Security Visibility
SaaS Security Visibility
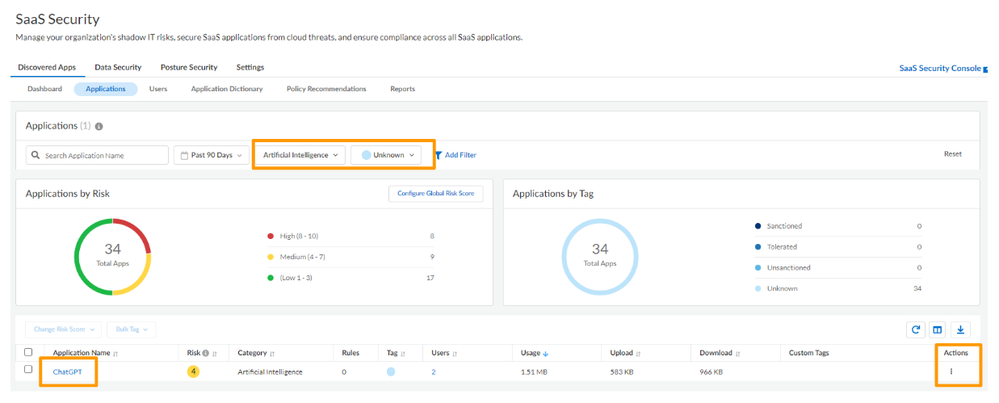 SaaS Security Granular Control
SaaS Security Granular Control
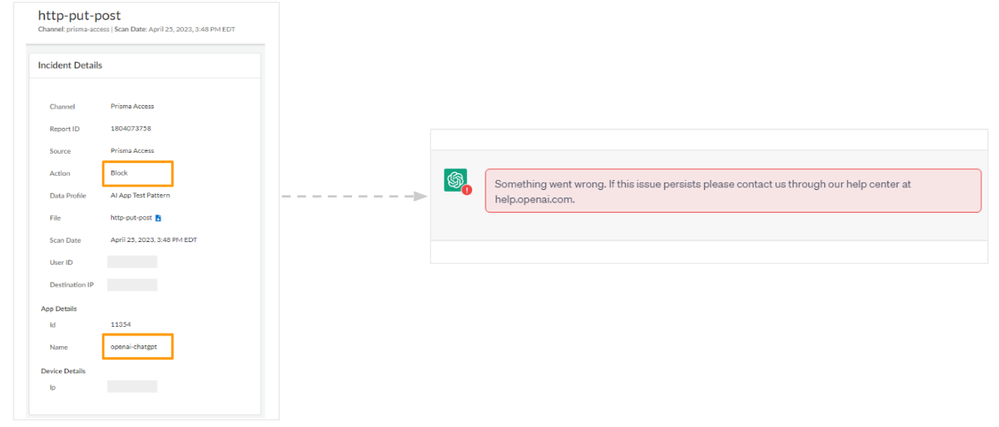 Data Loss Prevention (DLP)
Data Loss Prevention (DLP)
Aside from ChatGPT, we're on a continuous mission to expand AI app support! Brace yourself for a growing roster that now includes notable names like GitHub Copilot, Playground, and Bing Chat. It's all about making sure you have the tools and protection you need across a wide spectrum of AI-powered applications.
Want to know more ? Check out all there is to know about this amazing new release in the Prisma Access Administration Guide and the Prisma Access Release Notes.
We would like to hear how you've experienced Prisma Access release 4.2 so far. Please share your thoughts, comments and questions in the comments section below or on the Prisma Access LIVE Resource page.
Thanks for taking time to read this blog.
If you enjoyed this, please hit the Like (thumb up) button, don't forget to subscribe to the LIVEcommunity Blog area.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
| Subject | Likes |
|---|---|
| 3 Likes | |
| 3 Likes | |
| 2 Likes | |
| 2 Likes | |
| 1 Like |
| User | Likes Count |
|---|---|
| 6 | |
| 4 | |
| 3 | |
| 2 | |
| 2 |



