- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Nominated Discussion: Integrated User-ID and Active Directory
- LIVEcommunity
- Articles
- General Articles
- Nominated Discussion: Integrated User-ID and Active Directory
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 08-23-2022 07:36 AM
This article is based on a discussion, Humps and bumps with the Palo Alto firewall integrated User-ID agent and Active Directory, posted by @Han.Valk.
Introduction
The User-ID agent links an IP-address to a user account. It enables identifying your users so that they show up in the logs and you can use them in rules. One can choose between the integrated agent or install the Windows edition. Problem with the Windows variant is that it is unsupported with Windows Server 2022 domain controllers at the moment of this writing. Therefore, in this article I will concentrate on the integrated edition.
Using the integrated User-ID agent, one can choose from several combinations of transport protocols and authentication mechanisms:
- WMI
- HTTP with Kerberos
- HTTPS with Kerberos
- HTTPS with basic authentication
Documentation is missing important details and sometimes a bit messy.
For all deployments using the integrated User-ID agent you must add the service account you created to the following three groups that you can find in the Builtin container in Active Directory:
- Distributed COM Users
- Event Log Readers
- Remote Management Users
I’ve done some experimenting with different combinations of these three groups and found you need all of them to not only see a Connected status in Server Monitoring, but also to get useful data. A Connected status doesn’t say everything.
If you have a multi-domain forest, you’d be better off creating a universal group in the root domain, assuming that’s where your service account lives. Make the service account a member of this group and add the universal group to the three groups mentioned above.
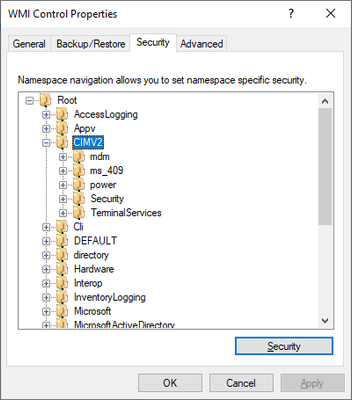
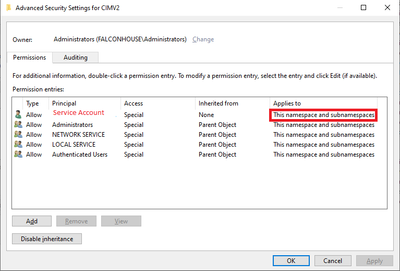
One thing the documentation isn’t telling you is that you not only need to give the service account ‘Enable Account’ and ‘Remote Enable’ WMI permissions on the CIMV2 branch but also on everything below it.
Please use Advanced → Add so that these permissions are applied to ‘This namespace and subnamespaces’.
Repeat this for every domain controller you want to monitor.
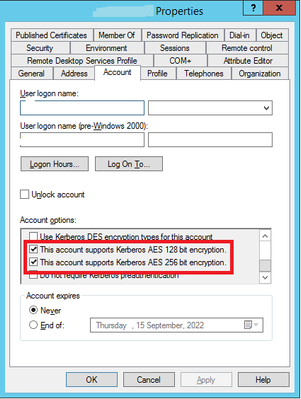
Another important point is that your service account must support Kerberos AES 128 or 256 bit encryption. Sometimes you must reset the password of the service account as well so that it is stored with AES encryption.
WMI
Because of DCOM hardening changes that Microsoft is rolling out, WMI does not work until you deploy the RequireIntegrityActivationAuthenticationLevel registry value and set it to zero. However, this setting currently has no effect in Windows Server 2022. With Windows Server 2022 your system log will fill with event id 10036 errors regardless what value you use for RequireIntegrityActivationAuthenticationLevel.
@palo Alto Networks: Can you please anticipate on the coming DCOM hardening so we can use WMI with DCOM hardening enabled?
@Microsoft: Can you please fix RequireIntegrityActivationAuthenticationLevel on Windows Server 2022?
HTTP with Kerberos
This works great in a flat active directory forest, but… What if you have a multi-domain Active Directory forest with child domains and lots of domain controllers? Will this work?
You can only add 4 domain controllers to a Kerberos Server Profile and you can only configure one Kerberos Server Profile to the User-ID Agent Setup.
One other thing, with Kerberos you must configure a domain and use FQDNs. Thus, the firewall must be able to resolve this domain and those domain controllers.
HTTPS with Kerberos
A few things to keep in mind in addition to that what is written above about HTTP with Kerberos:
- You have to create a Certificate Profile. Please do not only add the root certificate but also all intermediates.
- You must create a HTTPS listener for WinRM using this command: winrm create winrm/config/Listener?Address=*+Transport=HTTPS @{Hostname="<hostname>";CertificateThumbprint="Certificate Thumbprint"
Note: The hostname must be the same as the common name of the certificate otherwise WinRM won’t accept the command.
HTTPS with basic authentication
Everything that I wrote above about HTTPS with Kerberos is also true for HTTPS with basic authentication. When using HTTPS with basic authentication instead of an FQDN you can also use the IP-address of the domain controllers you add to Server Monitoring. So, the firewall doesn’t need the ability to resolve the domain controllers.
One important note: I would not recommend using the HTTPS with basic authentication option since it will enlarge the attack surface of your domain controllers. It will make them vulnerable to password spray attacks.
- 6225 Views
- 0 comments
- 0 Likes
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
ADNS
1 -
Advanced DNS Security
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
2 -
AI Security
1 -
AI Threat
1 -
AIOPS
1 -
Analytics
1 -
Ansible
2 -
antivirus
1 -
API
2 -
API & SDK
1 -
App-ID
1 -
applications
2 -
APS
1 -
Artificial Intelligence
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
6 -
AWS
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
7 -
Block List
1 -
Cardinality
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CI CD Integration
1 -
CICD integration
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud ngfw
1 -
Cloud security
2 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Configuration
8 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Container
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
Cortex XSIAM
1 -
Cortex XSOAR
2 -
CPSP
1 -
Custom Signatures
3 -
custom-featured-post
1 -
cyber elite
1 -
cyberelite
13 -
Cybersecurity
1 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
DLP
1 -
Docker
2 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
End to End Encryption
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
3 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
GKE
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
4 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
HyperLogLog
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector Design
2 -
Log Management
1 -
Logging
1 -
login
1 -
Logs
3 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
Network Security
35 -
Network Security Management
1 -
Network-Security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
31 -
NGFW Configuration
12 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Prisma Access
1 -
Panorama
12 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
7 -
Prisma AIRS
1 -
Prisma SASE
2 -
Prisma SD-WAN
1 -
proactive insights
2 -
Prompt Poaching
1 -
Public Cloud
1 -
Python
2 -
Radius
1 -
Ransomware
1 -
RBI
2 -
region
1 -
Registration
1 -
Remote Browser Isolation
3 -
Reporting
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Site-to-Site VPN
1 -
Software Firewalls
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
2 -
Strata Logging Service (SLS)
1 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Terraform
3 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
7 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
Upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
8 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WhatsApp
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next