- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Audit Global protect server
- LIVEcommunity
- Discussions
- General Topics
- Audit Global protect server
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Audit Global protect server
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-27-2020 08:32 AM
Hi,
We launched a sslab test for a GlobalProtect Portal website. Our note is B. We would like to improve these two things but we dont know what it can be done in PA config. These are:
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-01-2020 03:01 AM
Hi @BigPalo
Forward secrecy actually is supported by paloalto. If you look at the details of the browser handshake list, you should see most of them use ciphersuites with forward secrecy. Only a few - which count as reference browser for Qualys SSLLabs - do not use forward secrecy ciphersuites.
The point with the missing secure renegotiation is still true and unfortunately theres nothing you can do about that at the moment except wait until it is supportet (in PAN-OS 10 it is still not supported).
An explanation of secure renegotiation you can find here: https://devcentral.f5.com/s/articles/ssl-legacy-renegotiation-vs-secure-renegotiation-explained-usin...
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-09-2020 03:51 AM
Hi @BigPalo ,
You can easily get A minus on SSLlabs and take out most of the forward secrecy.
I assume you have your ssl-tls-service-profile set at minimum TLS 1.2
Just run the following via the CLI:
- configure
- set shared ssl-tls-service-profile yourprofile protocol-settings auth-algo-sha1 no
- set shared ssl-tls-service-profile yourprofile protocol-settings enc-algo-3des no
While you are at it also disable the following:
- set shared ssl-tls-service-profile yourprofile protocol-settings enc-algo-rc4 no
- set shared ssl-tls-service-profile yourprofile protocol-settings keyxchg-algo-rsa no
- commit
Unfortunately it does not fix anything for secure renegotiation.
Regards,
Raymond
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2023 09:10 AM
Can this be done as a push from Panorama? I do not like the concept of doing a command line only change on an individual firewall which could easily be forgotten in the case of a disaster restore or upgrade situation.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2023 10:15 AM
You can run those commands in Panorama CLI.
Instead of command:
set shared ssl-tls-service-profile...
You need to use:
set template TemplateName config shared ssl-tls-service-profile...
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2023 10:53 AM
I must be missing something...
I used the following commands (with the template name changed)
set template HiddenTemplateName config shared ssl-tls-service-profile VPN-SSL protocol-settings auth-algo-sha1 no
set template HiddenTemplateName config shared ssl-tls-service-profile VPN-SSL protocol-settings enc-algo-3des no
set template HiddenTemplateName config shared ssl-tls-service-profile VPN-SSL protocol-settings enc-algo-rc4 no
set template HiddenTemplateName config shared ssl-tls-service-profile VPN-SSL protocol-settings keyxchg-algo-rsa no
The following commit failed with the result down below - what am I missing - all the profiles (there are three like this) have certificates already and in use?
Operation
Commit
Status
Completed
Result
Failed
Details
sd_wan plugin validation: Config valid
Validation Error:
devices -> localhost.localdomain -> template-stack -> HiddenStackName -> config -> shared -> ssl-tls-service-profile -> VPN-SSL is missing 'certificate'
devices -> localhost.localdomain -> template-stack -> HiddenStackName -> config -> shared -> ssl-tls-service-profile is invalid
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2023 11:12 AM - edited 01-16-2023 11:13 AM
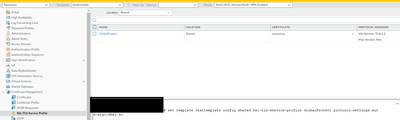
Go to "Device > Certificate management > SSL/TLS Service Profile"
Did you use correct name for profile or did it create new one named "VPN-SSL" as a result of the command?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2023 11:42 AM
I had already restored from backup the previous config so I just ran the commands and attempted commit again.
A new profile was not created according to the GUI. I looked in all the associated templates and template stacks.
I am now restoring back to original.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2023 11:44 AM
Try to tab complete the command and use questionmark to get correct options.
There must be typo in command somewhere.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2023 12:03 PM
Just adding "" around the various template names did not change anything. The commands have always been accepted with and without the "".
Using the ? as I worked through the first command I saw that certificate was an option. Adding that sub-command and then a ? again I was shown some certificates; however the one that is in use (from an external CA) was not in the list.
It looks like I will need to open a support ticket to get this sorted out.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2023 12:12 PM
No "" needed if template or profile names don't contain spaces.
Command works well and commit worked after entering command.
Palo Alto Networks certified from 2011
- 8612 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect MFA login using smtp in General Topics
- Need a similar setting of Global Protect in Prisma Access Agent in Prisma Access Agent Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Global Protect count current users not match statistics in GlobalProtect Discussions
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions