- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect clients experiencing latency delays
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect clients experiencing latency delays
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-29-2017 02:43 AM
Hello,
Clients who are connected via GlobalProtect VPN are experiencing slowness with all their traffic traversing the VPN (ie.. Internet and Server access traffic).
The latency is between 200-400ms for all the traffic regardless of whether its Internet based (to google) or server based (to our corporate servers).
Can you suggest any troubleshooting steps for this? Any relevant article to check?
Thanks in advance.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 07:36 AM
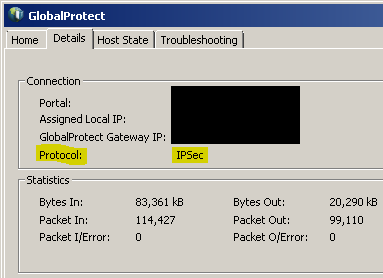
In GlobalProtect client, Details tab.
Check if protocol is SSL or IPSec.
If it is SSL then check if you permit udp 4501 towards GlobalProtect gateway.
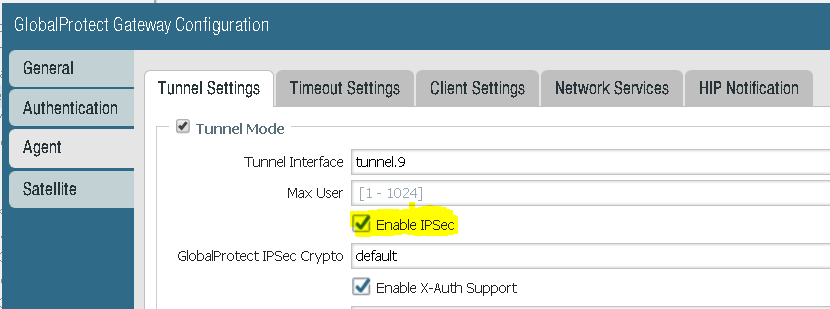
Also check that you have "Enable IPSec" checked in GlobalProtect gateway config (Tunnel Settings tab).
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 07:36 AM
In GlobalProtect client, Details tab.
Check if protocol is SSL or IPSec.
If it is SSL then check if you permit udp 4501 towards GlobalProtect gateway.
Also check that you have "Enable IPSec" checked in GlobalProtect gateway config (Tunnel Settings tab).
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 07:54 AM
So you mean to permit udp 4501 in to the firewall using a security policy permiting it? I have a rule coming in to the firewall for the global protect client that has service any and I still get complaints from users that it still too slow.
I looked in network/interfaces/tunnel and I don't see a place in enable ipsec but I do see it enabled when I go to the globalprotect gateway configuration
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 07:59 AM - edited 09-01-2017 08:00 AM
If you run GlobalProtect on your untrust interface and you don't have block any-any rule added then last interzone-default will permit from untrust to untrust 4501.
If you run GlobalProtect gateway on loopback and then you need to NAT udp 4501 to this loopback.
GlobalProtect agent will try IPSec 3 times and then falls back to SSL.
In case SSL it is TCP inside TCP (tcp meltdown and other issues can occure).
Enable IPSec is in firewall.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 08:05 AM
If agent view shows IPSec then issue is somewhere else.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 08:13 AM
Yes I have IPSEC enabled in the location in your screenshot. I am using the SSL protocol to connect. I must add I did not do the original configuration of the VPN's I have got them to work and now I am working at getting them to work as efficiently as I can.
I didn't find any NATTING concerning the loopbacks used for the VPN's
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 08:15 AM
If GP agent shows SSL as protocol it can't connect with IPSec.
Go to Monitor > Traffic and use filter below.
( port.dst eq 4501 )
Do you see it being blocked?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 08:22 AM
Port 4501 is not being blocked for legitimate traffic to the loopback for the VPN
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 09:17 AM
Earlier you mentioned you saw no natting but now you mention that GP runs on loopback.
If it runs on loopback there must be DNAT in place.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 03:32 PM
I also run different portals/gateways on loopbackinterfaces ... but I do not NAT at all in this case. All the loopbacks simply have public IPs so there is no need for DNAT
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2017 05:06 PM
True it can use external IP but if agent connects overr SSL then most likely it is either Security Policy or NAT that is not configured correctly.
In some rare cases source network but quite rare nowadays.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-18-2021 07:17 PM
Hi there! I know this thread is older...but how do you create a DNAT for 4501 AND 443?
For example, I have gateway configured with x.x.x.x:7000
I have a DNAT that forwards 7000 to 443. How do I get it working with 4501? reason I ask is because I want my tunnel to use IPSEC rather than SSL.
Thank you!!
- 1 accepted solution
- 16059 Views
- 12 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect Internal Detection in GlobalProtect Discussions
- Network connection unreachable on MAC OS newer version 15.3.2 o higher in General Topics
- stream timeout in General Topics
- High Data Plane Utilization During Business Hours in Next-Generation Firewall Discussions
- Wireless not connecting prior to login - Windows 11 in GlobalProtect Discussions