- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
I am trying to get my firewall on the network for the first time.
- LIVEcommunity
- Discussions
- General Topics
- Re: I am trying to get my firewall on the network for the first time.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
I am trying to get my firewall on the network for the first time.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2021 11:51 PM
So far I cant ping the firewall from the network and I can't ping the gateway or any pcs from the firewall. I have checked the arp table and I don't see any mac addresses there, so now I am starting to get concerned about the viability of this firewall. However my experience with paloalto firewalls started with this device. However my networking experience did not. I am running on 6.01. So obviously I would like to update the firewall so I can work with a more current version of PANOS. Finding documentation for 6.01 has not been very fruitful.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2021 07:31 AM
Hello
You may need to do a factory reset on the FW, if you think the FW is the cause.
You should be plugged into the mgmt port (which will NOT show its mac address in the ARP table. ARP is for the data plane ports).
Think of the mgmt port as nothing more than a linux computer. It should have a IP/mask/default gw that is local to your network.
I would plug my computer directly into the Mgmt port of the FW, and eliminate any network issues.
Can you console into the box, vs ssh or web page to it? From console you should try to ping out to your computer.
If the FW has a support contract on it, you may be able get it upgraded. Without support, how would you plan to upgrade?
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2021 08:03 AM
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2021 08:15 AM
Here is my deviceconfig
show deviceconfig
deviceconfig {
system {
ip-address 10.0.1.5;
netmask 255.255.255.0;
update-server updates.paloaltonetworks.com;
update-schedule {
threats {
recurring {
weekly {
day-of-week wednesday;
at 01:02;
action download-only;
}
}
}
}
timezone US/Pacific;
service {
disable-telnet yes;
disable-http yes;
}
hostname PA-3020;
default-gateway 10.0.1.1;
dns-setting {
servers {
primary 10.0.1.1;
}
}
}
setting {
config {
rematch yes;
}
management {
hostname-type-in-syslog FQDN;
}
}
}
[edit]
admin@PA-3020#
If there is another show command you would like to see let me know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2021 09:46 PM - edited 04-28-2021 09:47 PM
Also make sure Under Management interface Ping option is checked.
Also you can connect your PC to Management Interface of firewall and assign it IP in same subnet range and same gateway.
Then you can test whether you can ping the gateway from your PC or not?
Also is that gateway reachable from your network?
Regards
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2021 11:35 PM
I will check the ping option. I knew that there had to be a setting for the ping reply just hadn't found it yet. But since I did a factory reset I was thinking that it should be replying. The firewall is replying to a ping from itself. So I wasn't overly concerned about it. Just an fyi. I have held a CCNP I have worked with and installed Cisco routers for a number of years. I know how to make IP networks work. The firewall cannot ping the gateway router or pcs on the network, nor can they ping the firewall. The firewall is configured with 10.0.1.5/24 and the router is 10.0.1.1/24 The network is pretty simple but for some reason, its just not working. I have a pc that is using a terminal cable and I can windows terminal into that pc I work on it almost daily and i learn more and more every day but its just working yet. Do I need to turn on the Ethernet ports like I would on a Cisco router. I haven't found anything that looks like that in the configuration but it is something that makes sense.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-29-2021 01:31 AM - edited 04-29-2021 01:33 AM
Hi @Alleria ,
to be able to ping any Interface that belong to the firewall, each interface will need to have an "interface Mgmt with ping checked" assigned to that interface, you can find and create Interface mgmt under Network > Network profiles > interface Mgmt. and after that assigning it on the interfaces from Interface Advanced tab.
on the other hand you should be able to ping other hosts from firewall, but for your information if you did not specify the source of ping, the firewall will use the Physical managment interface, so i would try "ping source x.x.x.x host x.x.x.y" where xxxx the firewall interface that belong to same host-network.
hope that will work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-29-2021 01:42 PM
I just tried the ping source and host and it was not successful. Also this firewall atm is only on one network, so there really shouldn't be any issues there.
Part of my problem here has been the fact that I am on 6.01 so most of the documentation for 6.01 is not available online anymore, most of what I have been able to do I or figured out I have done on my own by exploring through the CLI. I have added IPs to the permitted IPs however upon checking the ARP table nothing seems to be getting into the firewall as it is.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-30-2021 07:48 AM
Good Day
You should install Wireshark onto your computer. Next, connect your computer to the mgmt interface and from the terminal window (as you can you can console in,) ping the IP of your computer (which should be on the same subnet). If the ping is not successful, you would have the wireshark trace to confirm that you either DID or DID NOT see ping attempts. If you see the pings, there is something external to the firewall. If you do not see the pings, then there is something wrong with this FW.
Just based on the version of code, I would not believe the FW has been in production or has had a maintenance contract on it. The FW may not even be licensed. If the FW is not licensed, then it may not allow to be pingable, but you should be able to bring up the GUI of the FW. Can you please provide some details about the FW, such as where you obtaned it from, was it in production, and when this FW was last known to be working. We all could simply be troubleshooting a bad firewall, whether you factory restored it or not.
What is the purpose of the FW? Are you planning to put it into a production or lab network? Are you wanting to teach yourself PANW firewalls? There are other solutions availablle to learn PANOS.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-11-2021 03:37 PM
Sorry for the delay in a response. I had a problem with wireshark not seeing my ethernet connection. Once I reinstalled it things worked much better. But I also had to work on my house funny how a leaking roof takes priorities. Anyway, I did some ping tests with wireshark running on the pc that I connect to the firewall with. While I was able to see pings to that pc and I am getting data all of the time I am not able to see pings to or from the firewall.
I got this firewall from ebay. If there is an issue with getting it to work I will have a hard time getting my money back. I have had it for a month now.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2021 11:11 AM
Hello. I am thinking that I would like you to ONLY have the PC connected to the management interface of the FW and nothing else. You shouldnt be able to see other traffic, because the cat5 cable will act as a "network", connecting your PC and the FW together. Then console into the FW (via console/usb) and try to ping outbound from the FW. If you do not see any pings from the FW, when only the PC and the FW are connected (again, not to switch/hub, etc), but directly connected, then you may have a bum mgmt interface on the FW.
I am making presumptions that the FW was factory defaulted, and you manually typed the config in, via the console cable, because you could not access the mgmt port directly.
There is also the other question/concern about licensing. It is great to have a FW to test/learn with.. but an unlicensed FW will NOT pass traffic (or very limited sessions, like 5 or less, if even that)...
Let me know how you progress.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2021 03:05 PM
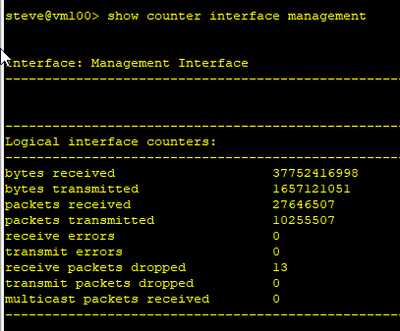
I connected just the pc into the firewall and i tried several different ports, and I had no luck pinging out of the firewall or pinging the firewall from the pc. The counters on the mgt interface also are not going up, and wireshark saw no icmp trafic or any other traffic that wasn't generated by the pc itself. I have never seen a bad logical interface, but my experience is limited to Cisco and Bay Networks. Is there a way around this problem.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2021 05:03 PM
Hello there. the ONLY interface that will even come close to passing traffic is the mgmt port. If you connected to the mgmt port and you see zero packets, no counters (which counters did you look at? Did you try "show counter interface management"
Again, if no traffic on the wireshark, counters are not moving, then I am not sure how you are convinced this is something we can get around. The FW appears to not transmit packets. You mentioned logical interface, why not physical interface (mgmt only).. you should plug into the mgmt port and at least see DNS attempts (if you configured DNS), or NTP (if you configured ntp) So, unless you doing something wrong, and are not properly communicating how things are connected up, then NO, i do not think there is anything more to do.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2021 06:19 PM
Just noticed this
9914 packets transmitted, 0 received, +7854 errors
Seen it when I ended the pinging that I had left on.
Pretty sure that those were the counters that I had looked at earlier
admin@PA-3020> show counter interface management
Interface: Management Interface
-------------------------------------------------------------------------------
-------------------------------------------------------------------------------
Logical interface counters:
-------------------------------------------------------------------------------
bytes received 0
bytes transmitted 0
packets received 0
packets transmitted 0
receive errors 0
transmit errors 0
receive packets dropped 0
transmit packets dropped 0
multicast packets received 0
I didn't setup one of the ethernet ports cause I am still learning this CLI. I tried to setup ethernet port 1/1. I got this when I tried to commit.
.
Validation Error:
zone -> untrust -> network -> virtual-wire 'ethernet1/1' is not a valid referenc
e
zone -> untrust -> network -> virtual-wire is invalid
This operation invalidates configuration for devices -> localhost.localdomain ->
vsys -> vsys1 -> zone -> untrust
network -> interface -> ethernet is invalid
[edit]
admin@PA-3020#
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-28-2021 11:31 PM
Ok I am now on the network. when I attempted to do a
admin@PA-3020> request system software check
I got this from the firewall
Server error : An active license is required for this feature
I'm guessing that this is a major road block.
- 14259 Views
- 16 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Is there an API to add IPs to Cortex XDR EDL programmatically? in Cortex XDR Discussions
- Palo Alto Networks Certified Security Professional in General Topics
- PAC File for Prisma Access China in Prisma Access Discussions
- how to download the network channel client(AI red teaming) in General Topics