- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Palo Dual Action on Same Malicious Domain
- LIVEcommunity
- Discussions
- General Topics
- Palo Dual Action on Same Malicious Domain
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Palo Dual Action on Same Malicious Domain
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2021 11:08 AM
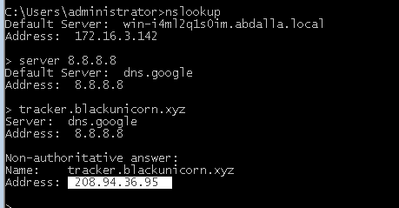
We have found in the logs, Malicious DNS queries are being blocked but few of them are in Alert State. however the Domain is marked as a malicious in DNS signature at Threat Vault.
Can you please elaborate why paloalto having dual action on same malicious domain.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2021 10:33 PM
@reaper we are not using Vsys moreover it's hit on same policy. Furthermore when we check the other domains we are still see that some time paloalto it's show alert and 90% is sinkhole please suggest.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-22-2021 12:09 PM
In our case, if the get the IP address of the malicious domain and it generates the “alert” on the firewall.
One the second time it will identify its malicious domain then the query will send to the sinkhole.
DNS sinkhole can be used to identify infected hosts on a network where there is an internal DNS Server in-route to the firewall that causes the reference of the original source IP address of the host that first originated the query to be lost (the query is received by the Internal DNS Server, and the internal DNS Server sources a new query if the name-to-IP resolution is not locally cached).
The things we have understood by your assistance but we could not found any document having the same use case or actual flow of DNS or its cache how they works.
Can you please suggest any document or use case.
- 2625 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- How to request review of residual High-Risk rating when category dispute has been resolved? in General Topics
- VirusTotal Bad reputation - krakensys.xyz in VirusTotal
- False positive High-Risk classification for legitimate healthcare SaaS (gmedic.co) in Next-Generation Firewall Discussions
- PAN-275077 is this bug still affected in 11.1.10-h1? in Next-Generation Firewall Discussions
- Up-to-date detections for TeamPCP malware used in Trivy and Checkmarx compromises available? in Cortex XDR Discussions