- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
SSL Decryption - No bypass at cert error screen
- LIVEcommunity
- Discussions
- General Topics
- Re: SSL Decryption - No bypass at cert error screen
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2015 08:47 AM
Dears,
We tried to configure SSL Decryption in our 3020 box and for some users with no certificate applied, we have that common certificate error page.... But in our case, we have no "bypass button" ....
we created everything according PA tutorial and also we created a custom URL containing *.google.com and google.com
- Labels:
-
Configuration
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-12-2015 12:29 PM
We had a similar issue with a secure site and Firefox wouldn't offer the option to bypass on a PC while it did work on mine. We use the same version, and we're on the same subnet. Clearing the cache in Firefox on his PC is all it took for it offer the option to continue.
"for some users with no certificate applied, we have that common certificate error page..."
BTW, if you're decrypting traffic and don't have the certificate applied for some people and they get the alert, be aware that you're conditioning these users to blindly accept any untrusted connection in the future.
Also, some sites won't allow to continue if the MIM certificate is not installed, no matter what. Those sites will have to be added to an ssl bypass list.
Larry.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2015 10:15 AM
Chrome uses a mechanism called Certificate Pinning for google-based sites (google, youtube, gmail, etc.). If your users don't trust the root CA used in your SSL decryption, there is no way to bypass the message you're seeing. Once you trust the CA used for your decryption, and you clear the cache of the browser, you should be able to go back to gmail and it should work.
Chrome, IE, and Safari all use the Windows certificate store. Firefox uses its own, so you'll have to repeat the steps on Firefox if you hit it there too.
Cheers,
Greg
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2015 12:42 PM
Hello and Thank you for the help!!
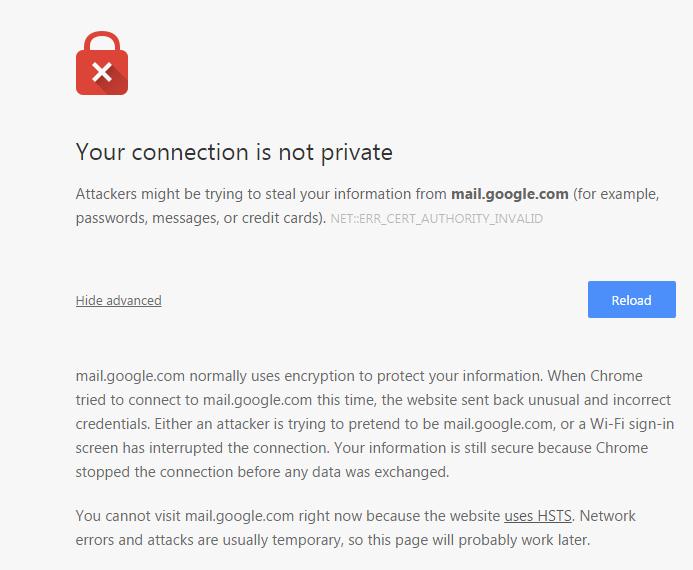
I tried everything... and just mail.google.com I have no bypass button....
cert error screen for google.com
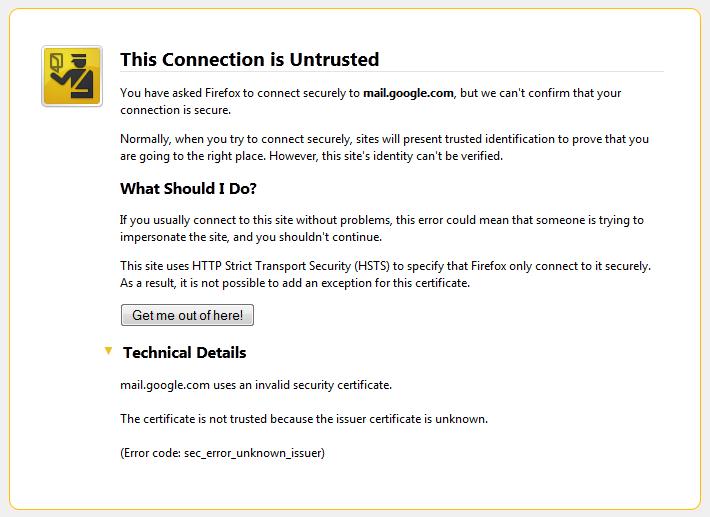
Is there any option to bypass this "HTTP Strict Transport Security (HSTS)" ?? As far as I understood... that site force us to trust the certificate or it will not allow the access.... right ?
thanks and best regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2015 01:17 PM
HSTS is a setting enforced by servers, not browsers, which forces the clients connecting to use TLS instead of plain HTTP.
You need to install the CA cert used in your firewall's decryption policy onto the clients and make it a trusted CA. That's the only way to correctly use decryption.
Here are the steps for Firefox: After Configuring SSL Decryption Mozilla Firefox Presents Certificate Error
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-12-2015 12:29 PM
We had a similar issue with a secure site and Firefox wouldn't offer the option to bypass on a PC while it did work on mine. We use the same version, and we're on the same subnet. Clearing the cache in Firefox on his PC is all it took for it offer the option to continue.
"for some users with no certificate applied, we have that common certificate error page..."
BTW, if you're decrypting traffic and don't have the certificate applied for some people and they get the alert, be aware that you're conditioning these users to blindly accept any untrusted connection in the future.
Also, some sites won't allow to continue if the MIM certificate is not installed, no matter what. Those sites will have to be added to an ssl bypass list.
Larry.
- 1 accepted solution
- 8767 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- URL category for anydesk in Next-Generation Firewall Discussions
- How to trigger a "Response page" on Palo Alto NGFWs using URL filtering & Decryption in Next-Generation Firewall Discussions
- Global Protect Split Tunneling with multiple network adapters in GlobalProtect Discussions
- Google street view in maps.google.com not working in General Topics
- block yahoo mail in Next-Generation Firewall Discussions




