- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
User ID Agent - Monitoring logs
- LIVEcommunity
- Discussions
- General Topics
- User ID Agent - Monitoring logs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-22-2022 02:18 PM - edited 12-22-2022 02:24 PM
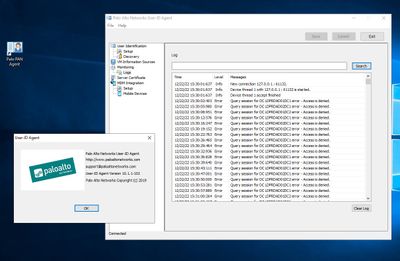
We've noticed errors in the Monitoring logs of our Windows servers running the PAN Agent ID software.
The User ID is working fine but the error is continually filling the logs. (error screenshot attached)
PAN o/s 10.1.6 h3 and the Agent ID version is 10.1.1-102.
useridd.log
==========
2022-12-21 08:38:10.822 +0000 Error: pan_ssl_conn_open(pan_ssl_utils.c:755): pan_tcp_sock_open() to 10.64.58.202 port 5009 failed; errno=115
2022-12-21 08:38:10.822 +0000 2022-12-21 08:38:10.822 +0000 Error: pan_ssl_conn_open(pan_ssl_utils.c:755): pan_tcp_sock_open() to 10.64.58.169 port 5009 failed; errno=115 Error: pan_ssl_conn_open(pan_ssl_utils.c:755): pan_tcp_sock_open() to 10.64.58.204 port 5009 failed; errno=115
2022-12-21 08:38:16.463 +0000 Warning: pan_hip_report_file_modify_cert(pan_hip_handler.c:3030): cannot find
2022-12-21 08:38:16.464 +0000 Warning: pan_hip_report_init_xml(pan_hip_report.c:311): can't get os_vendor from report 'L-PF3KYHJ5'
2022-12-21 08:38:16.464 +0000 pan_hip_obj_evaluate_list(pan_hip_obj.c:2472): b_collect_apps: 0
2022-12-21 08:38:19.210 +0000 Error: pan_ssl_conn_open(pan_ssl_utils.c:755): pan_tcp_sock_open() to 10.64.58.153 port 5009 failed; errno=115
2022-12-21 08:38:20.346 +0000 Error: pan_ssl_conn_open(pan_ssl_utils.c:755): pan_tcp_sock_open() to 10.64.58.201 port 5009 failed; errno=115
2022-12-21 08:38:20.346 +0000 Error: pan_ssl_conn_open(pan_ssl_utils.c:755): pan_tcp_sock_open() to 10.64.58.203 port 5009 failed; errno=115
2022-12-21 08:38:27.130 +0000 2022-12-21 08:38:27.130 +0000 Error: pan_ssl_conn_open(pan_ssl_utils.c:755): Error: pan_ssl_conn_open(pan_ssl_utils.c:755): pan_tcp_sock_open() to 10.64.58.202 port 5009 failed; errno=115 pan_tcp_sock_open() to 10.64.58.169 port 5009 failed; errno=115
next action plan:
Awaiting user windows server version.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-23-2022 07:42 AM
Hi @vij ,
Could be related to several issues.
Make sure the service user used with User-ID Agent is added to the "Server Operators" group (https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClVPCA0).
I've also seen this issue where update KB5014692 was causing the issue.
Make sure you have this patch installed on both the domain controller and the agent servers.
Hope this helps,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-23-2022 07:42 AM
Hi @vij ,
Could be related to several issues.
Make sure the service user used with User-ID Agent is added to the "Server Operators" group (https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClVPCA0).
I've also seen this issue where update KB5014692 was causing the issue.
Make sure you have this patch installed on both the domain controller and the agent servers.
Hope this helps,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- 1 accepted solution
- 3901 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cortex XDR Pro – Does it scan USB devices upon insertion? in Cortex XDR Discussions
- Cortex XSOAR - Forwarding Audit Log Execution Playbook to SIEM in Cortex XSOAR Discussions
- Screen reader Application hang in General Topics
- user-id - Firewall is not learning upn name format in Next-Generation Firewall Discussions
- Global Protect Connectivity Issue in GlobalProtect Discussions