- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
PaloAlto does not pass through itself a request for AD
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- PaloAlto does not pass through itself a request for AD
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
PaloAlto does not pass through itself a request for AD
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-26-2022 07:52 AM
Hi !
I have problem with connection PC to AD between which stands PaloAlto
PC 192.168.10.10
AD 192.168.30.40 (loc.lab)
pings go from PC to AD 192.168.30.40 (loc.lab) and return successfully
pings go from PC to loc.lab (192.168.30.40) and return successfully
But when I try to connect a PC with a local account enter into the domain i get
when i transfer pc to network 30 i successfully connect to AD
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-27-2022 09:00 AM
Hello,
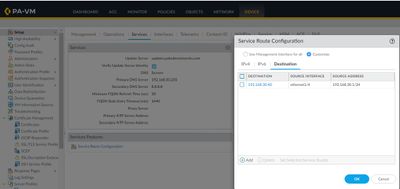
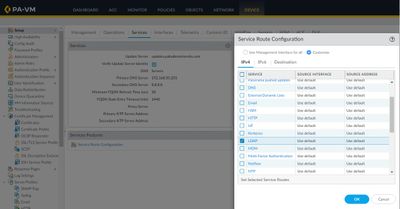
My guess is that the Palo Alto is blocking the traffic. Make sure there is a policy that allows the traffic to/from the Domain Controllers to the subnet the PC is on. Enable logging on all policies and use the Traffic logs to check for blocks, etc. Also from one of the screenshots, looks like the LDAP is still set to use the default ,eg the management interface.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-28-2022 04:35 AM
I agree with @OtakarKlier I would check for dropped traffic, although as pointed out definately in the screenshot the route for LDAP is the MGMT interface so you would have to check which firewall that traffic is going through and this is the intended route.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-29-2022 12:18 AM
When you say "after transfer pc to network 30 i successfully connect to AD", what is the network configured on the PC in which the connection fails?
I would check the routing table on the PC when configured in the problematic network to see if the traffic is forwarded to the firewall? (Basically, tracing the traffic)
**My understanding says -- The service-route settings is for the management-plane traffic. If we are just concerned about the traffic between PC <--> AD, then we can rest assured that the service will not be used.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-29-2022 01:22 AM
I think you are right that this may be simply connecting the PC to the domain, but looking at the rule base, all rules are completely open, this would suggest that any connected network that has a route to the AD server should be OK, I am just wondering if it is the PC or the firewall that the AD connection is for, if @ArtemTokarenko was not trying to connect the firewall then why show the LDAP config on it, however the error message is not from the Palo.
Could you provide some more context please @ArtemTokarenko
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-31-2022 12:25 AM
Hello everyone, I could not understand what is the reason for this problem, I created another Win10 VM and everything was fine. Microsoft Magic
- 3065 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- [FIREWALL] - Commit Issue in Next-Generation Firewall Discussions
- resolve hostname in logs now working in panorama in Panorama Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- Is the unified RPC interface (MonitorDirect.enqueueLogRequest) supported for external use? in Next-Generation Firewall Discussions
- Request for SD-WAN Deployment Documentation in Azure in Advanced SD-WAN for NGFW Discussions