- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to verify group-mapping in PRISMA access
- LIVEcommunity
- Discussions
- Secure Access Service Edge
- Prisma Access Discussions
- How to verify group-mapping in PRISMA access
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2020 01:52 PM
Hi all,
I'm wondering, how to verify, that the group-mapping in Prisma-Access is working correctly.
We configured the Prisma as described in the admin guides, but my group-based security policies are not working as expected.
Authentication via LDAP is working via LDAPS, so I guess the LDAP-connection vor retrieving groups is working.
I would like to do a thing like "show user group list" or sth. else, I can do with on-prem firewall.
Also it would be nice to immediately trigger the group-refresh via "debug user-id refresh group-mapping all".
You get my idea, right?
Any ideas?
Regards
Chacko
Chacko
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2020 06:20 AM
As you said if authentication and traffic policies are working properly it indicates, the group mapping is being retrieved.
The ability to directly run those commands is feature request. Please reach out to SE of the account to help to file the feature request
~ Sai Srivastava Tumuluri ~
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2020 07:32 PM - edited 03-24-2020 09:00 AM
Hi Chacko,
Unfortunately, you will have to open a TAC case to troubleshoot this. As you mentioned, you need to run some CLI commands to verify and troubleshoot the configuration.
However, here is my suggestion, from my experience, most of the time the issue is due to a format mismatch on the authentication policy vs the group mapping format.
Here is an example:
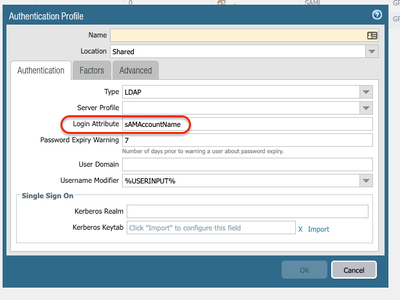
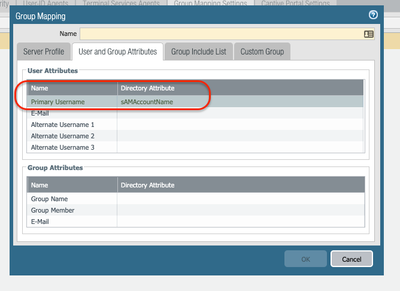
If you are using sAMAccountName on your Authentication Profile, make sure you add the same format on your Group-Mapping configuration.
Also, in a standalone Prisma Access deployment without a Master Device, you can use a group-based policy using long-form DN entries in Panorama. Prisma Access uses the DN entries to evaluate the User-ID-based policies you have configured in Panorama.
For example, given a User named Bob Alice who works in IT for Organization Hooli in the United States, a matching security policy may have ou=IT Staff,O=Hooli,C=US if the policy is to be applied to all IT staff, or CN=Bob Alice,ou=IT Staff,O=Hooli,C=US if the policy is only to be applied to Bob Alice.
Detailed instructions:
- Instructions for the configuration specific to Prisma Access:
- Best practice configuration:
https://docs.paloaltonetworks.com/pan-os/9-0/pan-os-admin/user-id/map-users-to-groups.html
- Multiple Username formats configuration:
I hope this helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2020 06:20 AM
As you said if authentication and traffic policies are working properly it indicates, the group mapping is being retrieved.
The ability to directly run those commands is feature request. Please reach out to SE of the account to help to file the feature request
~ Sai Srivastava Tumuluri ~
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-31-2020 11:34 AM
Hi @Sai_Tumuluri: Thanks, we asked TAC to run show user group name <x> and found out, that the primary user attribute was set to "uid" - I guess that was default behavior in the early days.
A freshly installed Prisma today, got the default sAMAccountName and the audit-logs from the faulty environment found no manual configuration made on this value - however, Feature reqest is sent to local PAN SE and with correct attributes, everything is matching as expected
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-31-2020 11:49 AM
Thank you for sharing update. Yes, TAC can help with them.
From my knowledge "sAMAccountName" was the default.
if the domain name is not populating, netbios communication might be failing. Verify with TAC help the domain is populating for users, it is imp
~ Sai Srivastava Tumuluri ~
- 1 accepted solution
- 14983 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions
- PAC File for Prisma Access China in Prisma Access Discussions
- Prisma Access (SWG):- Need to give access of Github's specific repositories to specific prisma access users in Prisma Access Discussions
- Prisma Access Agent Stability in Prisma Access Agent Discussions
- Prisma Access Service Connection to Palo Alto FW in HA-AA in Prisma Access Discussions