- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
- LIVEcommunity
- Products
- Cloud Native Application Protection
- Prisma Cloud
- Prisma Cloud Articles
- Who rated this article
Who rated this article
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 01-23-2024 10:44 AM - edited on 10-29-2024 12:17 PM by RPrasadi
By Omoniyi Jabaru, Senior Customer Success Engineer
and
Juan Montufar, Senior Customer Success Engineer
Introduction
Definition
A Secrets Manager is a secure and centralized tool or service used in the field of information technology and cybersecurity to store, manage, and access sensitive information, commonly referred to as "secrets". These secrets can include credentials, API keys, encryption keys, certificates, and other sensitive data that applications and services require for secure operation.
Secret Manager systems can vary depending on the platform or service you use. For example:
Cloud-Based: Cloud providers like AWS Secrets Manager, Google Cloud Secret Manager, and Azure Key Vault offer secret management services tailored for their respective cloud ecosystems.
Containers often require sensitive information, such as passwords, SSH keys, encryption keys, and so on. Prisma Cloud integrates with many common secrets management platforms to securely distribute secrets from those stores to the containers that need them.
Purpose
This document presents a step-by-step guide for testing Prisma Cloud’s secret manager. You will set up an AWS secret manager, store a secret in it, inject the secret into a running container, and then validate it so that it can be seen from within the container.
Objectives
- Centralization: Secrets Manager centralizes the storage of secrets, reducing the risk of secrets being scattered across various code repositories, configuration files, or hard-coded within applications. Centralization makes it easier to manage, rotate, and audit secrets.
- Security: Secrets Manager ensures that sensitive information is stored securely, often using encryption and access control policies. This helps protect against unauthorized access and data breaches.
- Access Control: Secrets Manager typically includes access control mechanisms to restrict who can view or modify stored secrets. This ensures that only authorized individuals or applications can access sensitive data.
- Rotation: Many secrets management systems provide the ability to periodically rotate (change) secrets automatically. This is essential for maintaining security as it limits the exposure of a secret if compromised.
In summary, a Secret Manager is a critical component of modern software development and infrastructure management, ensuring that sensitive information remains confidential and is handled securely throughout an application's lifecycle.
Requirements
You have the option to establish integration between Prisma Cloud and AWS Secrets Manager. Begin by setting up Prisma Cloud to connect with AWS Secrets Manager, and subsequently, establish rules for injecting the necessary secrets into corresponding containers.
Before proceeding, ensure that the credentials employed by Prisma Cloud for accessing the secrets storage have the subsequent permissions:
- secretsmanager:GetSecretValue
- secretsmanager:ListSecrets
These permissions are essential for the proper functioning of this integration. You’ll also need a user that is capable of creating secrets on AWS.
Part 1: Create a new secret in AWS Security Manager
Step 1: Create a secret in AWS Console:
1. Open the Secrets Manager console at AWS Secrets Manager.
2. Choose Store a new secret.
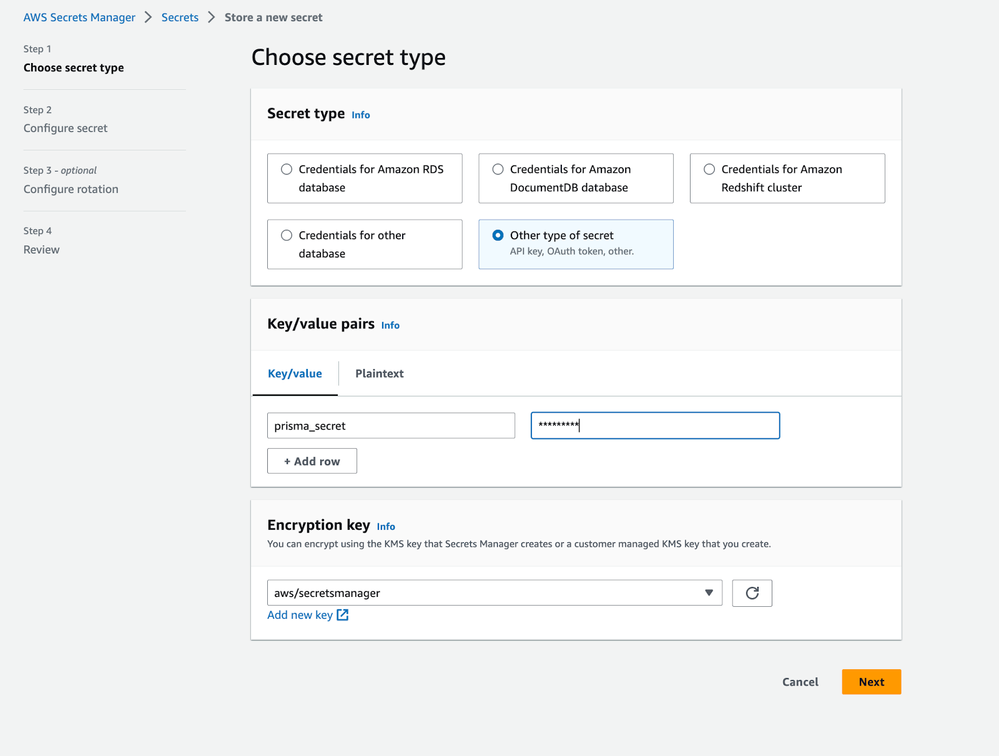
3. On the Choose secret type page:
a. For Secret type, choose Other type of secret.
Figure 1: Create a secret on AWS console_palo-alto-networks
b. In Key/value pairs, either enter your secret in JSON Key/value pairs, or choose the Plaintext tab and enter the secret in any format. You can store up to 65536 bytes in the secret.
c. For the Encryption key, choose the AWS KMS key that the Secrets Manager uses to encrypt the secret value. For more information, see Secret encryption and decryption.
For most cases, choose aws/secretsmanager to use the AWS managed key for Secrets Manager. There is no cost for using this key.
d. Choose Next.
4. On the Configure secret page:
a. Enter a descriptive Secret name and Description. Secret names must contain 1-512 Unicode characters.
b. (Optional) Use the Tags section to add tags to your secret. For tagging strategies, see Tag AWS Secrets Manager secrets. Don't store sensitive information in tags as they are not encrypted.
c. (Optional) To add a resource policy to your secret, go to Resource permissions, select Edit permissions. For more information, see Attach a permissions policy to an AWS Secrets Manager secret.
d. (Optional) If you would like to replicate your secret to another AWS region, select Replicate secret. You can replicate your secret now or come back and replicate it later. For more information, see Replicate a secret to other Regions.
e. Choose Next.
5. (Optional) On the Configure rotation page, you can turn on automatic rotation. You can also keep rotation off for now and then turn it on later. For more information, see Rotate secrets. Choose Next.
6. On the Review page, review your secret details, and then choose Store.
Secrets Manager returns to the list of secrets. If your new secret doesn't appear, choose the refresh button.
Figure 2: Review secret created_palo-alto-networks
Part 2: Injecting Secrets
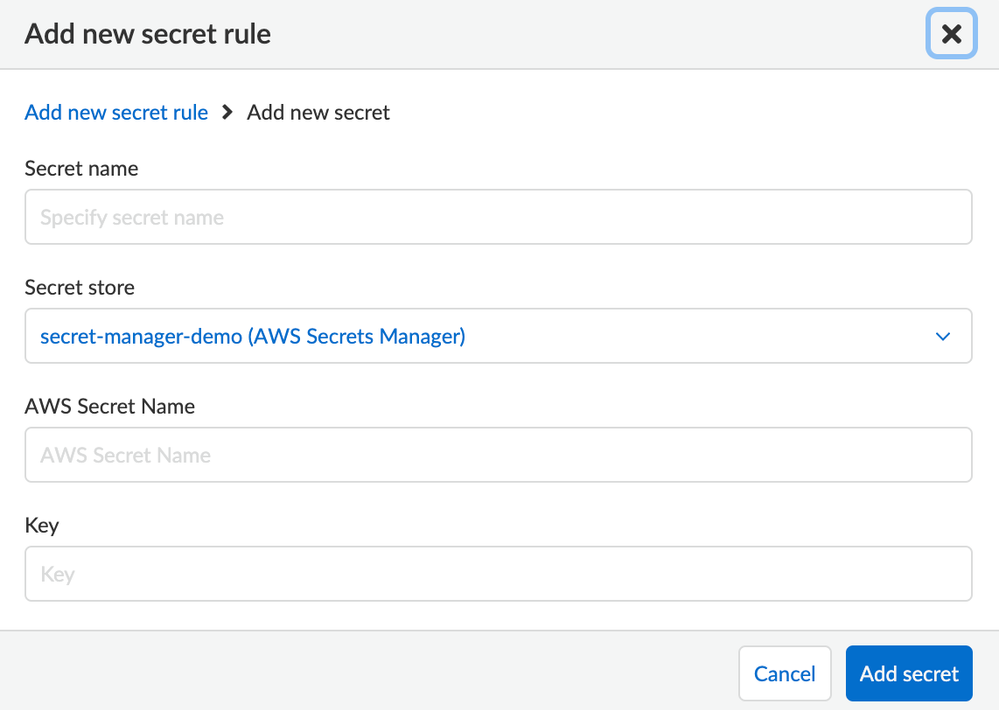
Step 1: Integrate Prisma Cloud with AWS Secret Manager
1. Open Prisma Cloud Runtime Security Console.
2. Integrate Prisma Cloud with the secrets store.
a. Go to Manage > Authentication > Secrets, and click Add store.
b. Enter a name for the store. This name is used when you create rules to inject secrets into specific containers.
c. For Type, select AWS Secrets Manager, then fill out the rest of the form, including your credentials.
d. Fill out the rest of the form, specifying how to connect to the Secrets Manager.
Figure 3: Create secret rule on Prisma Cloud_palo-alto-networks
e. Click Add.
f. After clicking Add, Prisma Cloud tries connecting to your secrets manager. If successful, the dialog closes, and an entry is added to the table. Otherwise, connection errors are displayed directly in the configuration dialog.
Next, inject a secret into a container.
Step 2: Verify secret is successfully injected
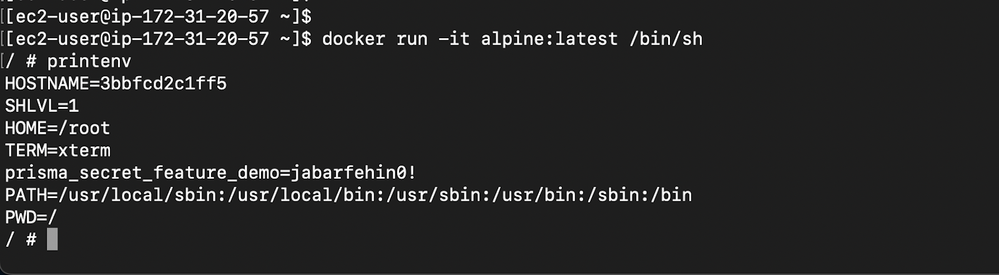
Let's assume the rule is designed to apply to the alpine container.
By default, rules are configured to encompass all resources within the environment. The fields for Containers, Images, Hosts, and Labels are set to wildcards. If the rule is configured in this manner, the secrets will be automatically injected into the alpine container.
Please note the secret name: prisma_secret_feature_demo
Figure 4: Edit secret rule_palo-alto-networks
Note: the secret value “jabarfehin0!” from the AWS Secret manager
Figure 5: Secret to inject_palo-alto-networks
If the secret was injected as environment variable run the following command:
$ docker run -it alpine:latest /bin/sh
/ # printenv
Figure 6: Verify injected secret as environment variable_palo-alto-networks
As seen above, the secret has been successfully injected to the environment variable as prisma_secret_feature_demo=jabarfehin0!
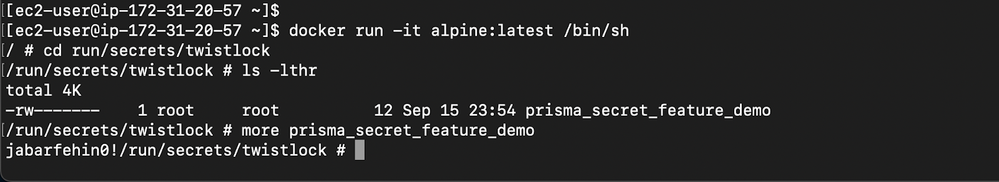
If the secrets are injected as files, and the Target directory is unspecified in the rule, then the secrets are injected into /run/secrets/, where <SECRET-NAME> is the name of the injected file, as specified in the rule.
$ docker run -it alpine:latest /bin/sh
/ # cat /run/secrets/twistlock/prisma_secret_feature_demo
Figure 7: Verify injected secret as a file_palo-alto-networks
As seen above, the secret has been successfully injected as a file
Conclusion
The integration of Prisma Cloud Secret Manager with AWS Secret Manager enhances security and streamlines access control by providing a unified and centralized platform for managing sensitive information, ensuring efficient and robust protection of critical assets in cloud environments.
The adoption of a Secrets Manager is imperative for various reasons in the field of information technology and cybersecurity:
- Enhanced Security: Secret Managers employ robust security measures such as encryption, access controls, and auditing capabilities to safeguard sensitive data from unauthorized access and potential breaches.
- Centralized Management: Secret Managers provide a centralized repository for storing and managing secrets, reducing the risk of secrets being mishandled or scattered across various applications and repositories.
Reference
[1] Secret encryption and decryption
[2] Tag AWS Secrets Manager secrets
[3] Attach a permissions policy to an AWS Secrets Manager secret
[4] Replicate a secret to other Regions
[5] Rotate secrets
[6] Inject a secret into a container
About the Authors
Omoniyi Jabaru and Juan Montufar are senior customer success engineers specializing in Prisma Cloud, Next-Generation Firewall, AWS, Azure, GCP, containers and Kubernetes. They use collaborative approaches to break down complex problems into solutions for global enterprise customers and leverage their multi-industry knowledge to inspire success.