
- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Protecting your network begins with a secure firewall deployment. It is very important to secure the management interface and management network to prevent exploitation. So even when an attacker knows the login credentials of your devices, you can still prevent them from getting in.
Best practice is to use the out-of-band (mgt) port for the firewall administrative tasks. We understand that there are some scenarios where, instead of using the mgmt-port, one would configure one of the data ports for mgmt access to the firewall. Whatever your setup is, it is key to make it a hard target for the attackers and protect the firewall/Panorama and NEVER enable access to your mgmt interface from the internet or from other untrusted zones. This applies whether you use the dedicated management port (MGT) or you configure a data port as your management interface.
Below are some guidelines to reduce exposure to your management interface (Device > Setup > Interfaces > Management):
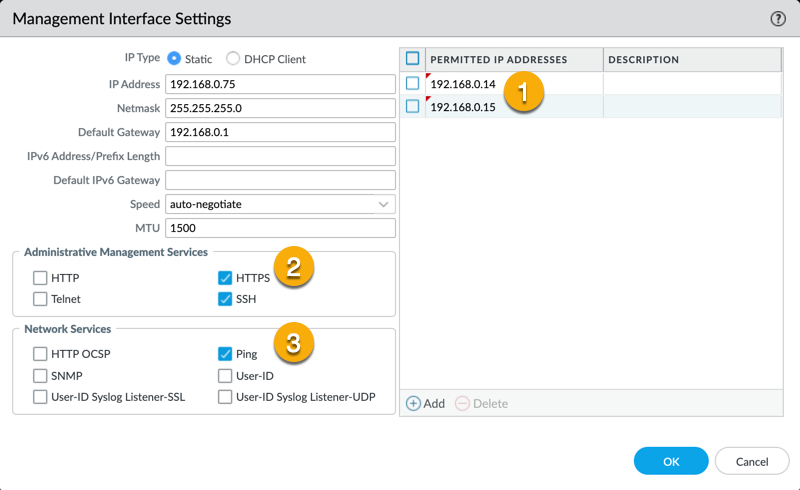 Device > Setup > Interfaces > Management
Device > Setup > Interfaces > Management
 Network > Network Profiles > Interface Mgmt
Network > Network Profiles > Interface Mgmt
Aside from limiting access to the management interface, there are also guidelines for the administrator accounts:
 Default admin account was deleted by supremeleader
Default admin account was deleted by supremeleader
 Use one of the predefined profiles or create your own custom profile
Use one of the predefined profiles or create your own custom profile
Configure a strict password policy, including requiring frequent password changes (Device > Setup > Management > Minimum Password Complexity). Strong password policies protect you from various password hacking techniques.

Can you think of other ways to secure your device management ? Feel free to add your comments below!
Thank you for taking time to read this blog.
Don't forget to hit the Like (thumbs up) button and to Subscribe to the LIVEcommunity Blog area.
Kiwi out!
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
| Subject | Likes |
|---|---|
| 3 Likes | |
| 2 Likes | |
| 1 Like | |
| 1 Like | |
| 1 Like |
| User | Likes Count |
|---|---|
| 3 | |
| 2 | |
| 2 | |
| 1 | |
| 1 |




