- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Inbound TLS/SMTP inspection (to FortiMail)
- LIVEcommunity
- Discussions
- General Topics
- Inbound TLS/SMTP inspection (to FortiMail)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Inbound TLS/SMTP inspection (to FortiMail)
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-04-2021 06:00 AM
Hi,
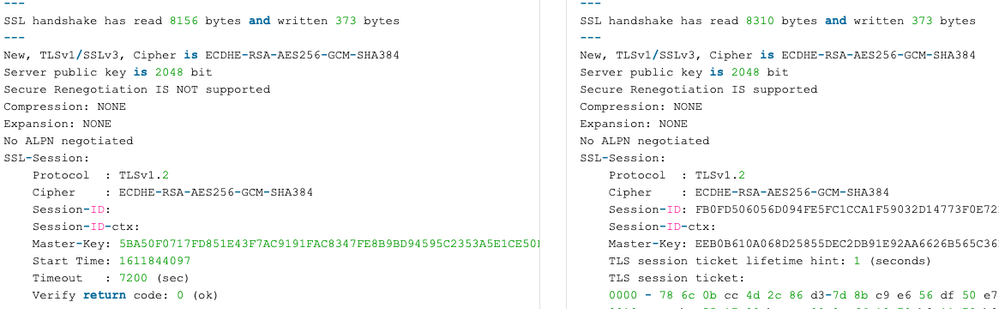
I'm wondering if anyone happens to be doing successful inbound inspection of SMTP/TLS to a FortiMail appliance? Or any other mail server for that matter. I've run in to a brick wall when it comes to renegotiation. The Palo is serving the correct certificate and a manual connections using openssl (openssl s_client -debug -connect mx1.XXXXX.com:25 -crlf -starttls smtp -showcerts) over a "decrypted" session and an "untouched" session shows identical output up until this point:
Decrypted (or well, attempted decryption) on the left and undecrypted normal session on the right.
I've made the decryption profile as generous as possible (i.e. not blocking any sessions and allowing all sorts keys and cryptos) and ECDHE-RSA-AES256-GCM-SHA384 is supported according to the docs. Anyone have any good ideas what to try next?
It feels somewhat like https://live.paloaltonetworks.com/t5/general-topics/ssl-inbound-inspection/td-p/246059 but I have no idea how to configure ciphers on the FortiMail.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-21-2021 03:29 PM
The palo alto may not have openssl tool to test the ciphers but in version 10 there is the improved that will tell you the needed info:
Also SSL handshake can be seen with a pcap from the firewall and you can see what ciphers are send by the server (the fortiMail):
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000CloUCAS
For more info:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClgHCAS
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2024 03:44 AM
Check error under decryption logs.
- 4042 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Can AI Access Security actually inspect RESPONSES generated by AI?? in AI Access Security Discussions
- web file blocking in Next-Generation Firewall Discussions
- Newsletter: Cloud Delivered Security Services, Aug-Sep, 2025 in Advanced WildFire Discussions
- Concerns of Firewall 5250 dropping packets and enabled DSRI (Disable Server Respponse Inspection) relieve issues for a few hours but came back in Next-Generation Firewall Discussions
- Tunnel Traffic from ISP2 IP Working Despite Default Route on ISP1 – Need Insights? in Next-Generation Firewall Discussions