- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Pushing Local Admin Accounts from Panorama
- LIVEcommunity
- Discussions
- General Topics
- Pushing Local Admin Accounts from Panorama
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Pushing Local Admin Accounts from Panorama
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-05-2019 02:51 AM
Hi,
Please forgive me if this is a stupid question as I am quite new to Palo Alto firewalls and Panorama.
We currently have Panorama running on PanOS 8.1.6 and the same for our firewalls.
We are using AD accounts for all our Administrators using radius authentication which works fine but we are discovering things that we cannot do with them and there is no option to give them the permissions to do so such as Software updates due to being unable to request a reboot.
In instances where we cannot use our AD Authenticated accounts we will need a local admin account on each of the firewalls in a break glass sort of scenario.
This is my problem.....
If I create a Local Admin account for the firewalls in the templates it is fine, except that when I login to a firewall it then asks me to change the password. This isn't an issue at the moment but we are soon to grow our estate from 8 firewalls to 200 and this would then become quite a laborious job to update all the firewalls individually.
Is there something that I am missing and is there any way around this.
Regards
Carl
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2019 04:51 AM - edited 03-07-2019 04:56 AM
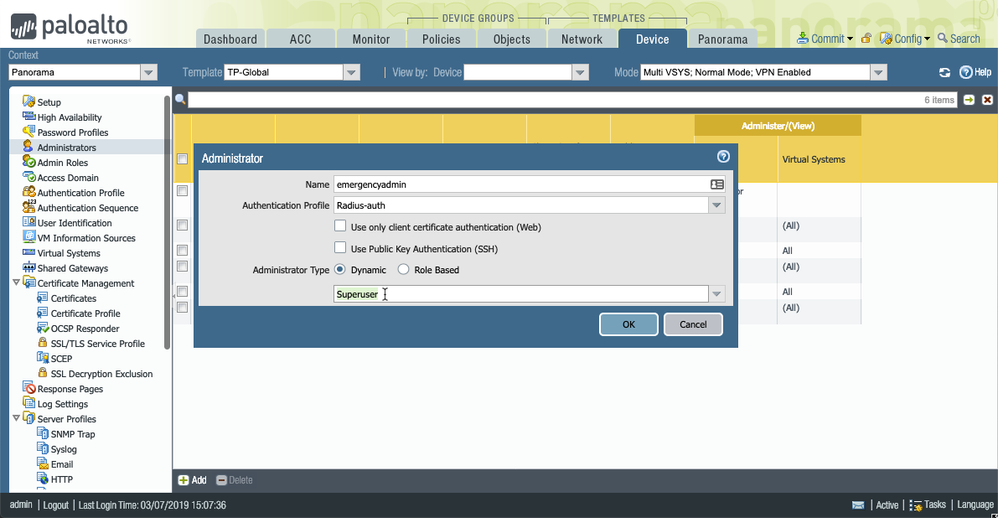
how about a break glass radius/activedir/.. admin with superuser privileges?
This would allow you to push one admin account to all firewalls which is centrally managed and as superuser is able to perform all tasks. you could set this up with MFA so for example, a token is needed to log on. The token is stored in a safe place until needed
you could still push out a local admin account as last resort disaster recovery but you would not need it nearly as much
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2019 05:26 AM
Hi Reaper'
Thank you for your reply.
I believe our admin accounts are setup as super users. as the AD\Radius is account is not setup locally on Panorama or the firewall we pass back the Admin Role they are given. The one in question configured on the firewalls is a Device Admin that has full access on the Web UI, nothing on the XML API and is configured as a SuperUser under the CLI section.
In my mind I thought this would be sufficient to allow those admins to do everything but I am finding certain functionalty that cannot be carried out under those accounts. Mainly mine that I am testing with at the moment. There does not seem to be an option to allow me to perform upgrades by rebooting the box.
Not an issue at the moment as there is a local account for me to use, but I am supposed to be deleting those and only having a breakfix with a super secure passowrd that is locked away.
I hope I have explained things correctly but let me know if not.
Regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2019 05:39 AM
to be able to reboot etc, the account needs to be a full super user, not a role based admin
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2019 06:02 AM - edited 03-07-2019 06:05 AM
Hi,
Which is why I am trying to get Panorama to push out local accounts that can be full super user and only be used to upgrade firewalls and anything else that an Admin Role cannot carry out.
But I do not understand why I need to change the password when we log onto the firewall for the first time. In a small environemnt this is possible but in a large environemnt it becomes very tedious indeed. When staff Leave or just to enforce our password policies we will need to change the local Admin accounts at least every couple of months and I was hoping to use Panorama for this.
Thank you for your replies so far, if nothing else it is providing clarity around what I can and cannot do.
Regards
Carl
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2019 07:38 AM
thats why a radius enabled admin (but set to dynamic>superuser instead of role based > role) would solve your issue
PANgurus - Strata & Prisma Access specialist
- 7702 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Rename security zones on panorama and push it to the firewalls in Panorama Discussions
- How to push Bulk IOC list in file format to panorama firewall? in Panorama Discussions
- Does thePAN 11.1.13 on panorama will work on local FW that is using 10.1.13-hr? in Panorama Discussions
- Few Objects are missing on firewall while Migrate a Multi-vSYS enabled Firewall HA Pair to Panorama Management in Panorama Discussions
- How to allow a user only to push the changes made by him/her on Panorama in Next-Generation Firewall Discussions