- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Secure LDAP Policy Rule Setup
- LIVEcommunity
- Discussions
- General Topics
- Re: Secure LDAP Policy Rule Setup
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-19-2015 09:48 AM
Hello.
I am trying to setup an application policy rule to allow secure LDAP from our hosting company back to our internal domain controller running MS AD. I have the appropriate NAT statement setup.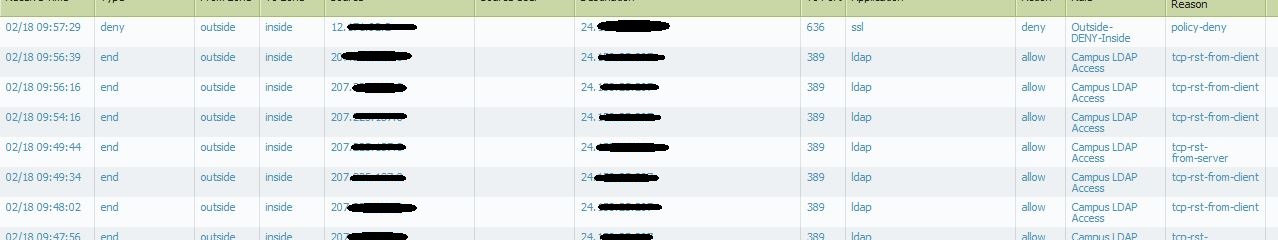
If you look in the log screenshot above, you'll see that the first entry is being denied. For my list of allowed applications in that rule, I have added LDAP and SSL. My services tab is set at Application-default.
For testing, I also tried just using regular LDAP with with just LDAP for application allowed, and services as Application-default. That worked fine, as you can see in log entry 2-8.
Do I need to change the services to TCP-636 to get LDAPS to work? I looked at the LDAP application object, and it lists 389, 636 as the ports it uses.
Thanks.
Dannon
- Labels:
-
Troubleshooting
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-19-2015 12:24 PM
Hi dannon
You will have to allow SSL on service TCP-636 to make this work.
Firewall will not be able to identify it as LDAP unless you enable decryption.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-19-2015 12:24 PM
Hi dannon
You will have to allow SSL on service TCP-636 to make this work.
Firewall will not be able to identify it as LDAP unless you enable decryption.
- 1 accepted solution
- 13094 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions
- XFF IP Address Logging clarification and impact in General Topics
- Foward Trust Cert and MacBook Pro in General Topics
- Security Policy Disappears After Commit – Palo Alto in Azure with Panorama in Next-Generation Firewall Discussions
- Cloud NGFW: Mandatory Panorama Upgrade to 11.2.7-h4 or higher for managing Cloud NGFW Firewalls. in General Topics




