- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
SSL Inspection fails even after Intermediate CA imported
- LIVEcommunity
- Discussions
- General Topics
- SSL Inspection fails even after Intermediate CA imported
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-25-2020 08:54 AM
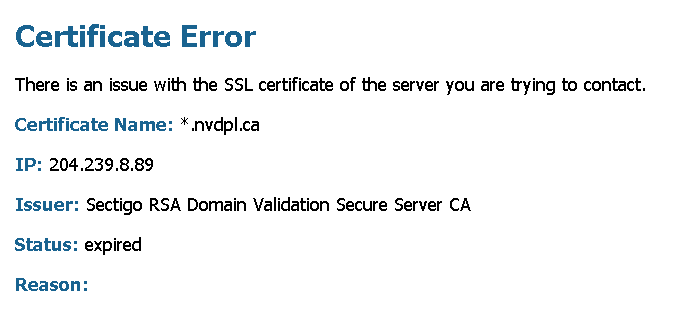
I have imported the intermediate CA, from 'Sectigo RSA Domain Validation Secure Server CA' and root CA 'USERTrust RSA Certification Authority' is already there on firewall default, but still outbound decryption fails.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-25-2020 11:11 AM
This is a known issue with the COMODO (now Sectigo) and some RSA certs
Details and work-arounds can be found here:
https://live.paloaltonetworks.com/t5/general-topics/sectigo-ca-chain-decryption-issues/td-p/330802
Also, I think this may be a "fix" in the latest PANOS: PAN-148068
PAN-148068 | Fixed an issue where SSL connections were blocked if you enabled decryption with the option to block sessions that have expired certificates. This issue included servers that sent an expired AddTrust certificate authority (CA) in the certificate chain. |
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-25-2020 11:11 AM
This is a known issue with the COMODO (now Sectigo) and some RSA certs
Details and work-arounds can be found here:
https://live.paloaltonetworks.com/t5/general-topics/sectigo-ca-chain-decryption-issues/td-p/330802
Also, I think this may be a "fix" in the latest PANOS: PAN-148068
PAN-148068 | Fixed an issue where SSL connections were blocked if you enabled decryption with the option to block sessions that have expired certificates. This issue included servers that sent an expired AddTrust certificate authority (CA) in the certificate chain. |
- 1 accepted solution
- 4427 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Forward Proxy & SSL Inbound Inspection Certificate Comparasion in Next-Generation Firewall Discussions
- How to use a Machine Cert with a Private Key for Global protect prelogon in GlobalProtect Discussions
- SSL inbound inspection certificate issue in General Topics
- EDL - unable to get local issuer certificate in Next-Generation Firewall Discussions
- Adding an External Dynamic List Object and importing the Intermediate CA certificate from the external web server that the EDL is hosted on in Next-Generation Firewall Discussions