- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
VPN Proxies
- LIVEcommunity
- Discussions
- General Topics
- VPN Proxies
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2019 06:29 AM
I have a VPN tunnel which is up and running. In the tunnel, I have 2 proxyID's which have the same local address but different remote addresses.
I can only get 1 proxyid to connect.
As an example, I current have proxyID1 connected and I can ping the other side. In the cli, if I type test vpn ipsec-sa tunnel tunnel-name-proxyID2. It does not come up. I also tried doing test vpn ike-sa gateway gateway-name, It still does not work.
Now if I delete, proxyID1, ProxyID2 connects.
It appears that in the proxyID list, only the first proxy gets connected.
Any Ideas?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 09:51 AM
Yes, I have 3 static routes going to tunnel.8
On the Cisco side, it uses access-list. You create the tunnel and then you give the remote side (which is us) what access it has. I have access to the following networks.
extended permit ip 10.16.48.0 255.255.248.0 10.127.0.0 255.255.0.0
extended permit ip 10.65.204.0 255.255.254.0 10.127.0.0 255.255.0.0
extended permit ip 10.65.206.0 255.255.254.0 10.127.0.0 255.255.0.0
id: 67
type: IPSec
gateway id: 6
local ip: 40.135.184.5
peer ip: 166.109.10.2
inner interface: tunnel.8
outer interface: ethernet1/1
state: init
session: 197787
tunnel mtu: 1448
soft lifetime: N/A
hard lifetime: N/A
lifetime remain: N/A
lifesize remain: N/A
monitor: off
monitor packets seen: 0
monitor packets reply:0
en/decap context: 3855
local spi: 00000000
remote spi: 00000000
key type: auto key
protocol: ESP
auth algorithm: NOT ESTABLISHED
enc algorithm: NOT ESTABLISHED
proxy-id:
local ip: 10.127.0.0/16
remote ip: 10.16.48.0/21
protocol: 0
local port: 0
remote port: 0
anti replay check: yes
copy tos: no
enable gre encap: no
authentication errors: 0
decryption errors: 0
inner packet warnings: 0
replay packets: 0
packets received
when lifetime expired:0
when lifesize expired:0
sending sequence: 0
receive sequence: 0
encap packets: 0
decap packets: 0
encap bytes: 0
decap bytes: 0
key acquire requests: 59
owner state: 0
owner cpuid: s1dp0
ownership: 1
I got on a call with tech support and this error message: INVALID_KE_PAYLOAD is due to a different DH-Group.
After the call, I verified with the other side and we both have the same group.
What I find interesting is that we have another tunnel and on the other side they also have a Cisco ASA. I have 5 proxyID's and they all work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2019 01:57 PM
What do your system logs show when both proxy ids are configured.
Clearly, there is a mis-configuration on the FW, whether it is through logic or anomaly. We just need to see more info to help.
Because we do not have access to your network, and there are millions of RFC1918 private networks, can you please show us the proxy IDs that you have configured, so that we can better understand your query?
Also, I am presuming you have a single VPN with 2 proxy ids, versus 2 separate tunnels with overlapping proxy ids, which is not permissible.
This is why we should see all VPN proxy IDs for each tunnel interface you have configured.
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 05:19 AM
Here is the ike logs
2019-12-10 11:02:47.014 -0500 [DEBG]: { 6: }: received notify type INVALID_KE_PAYLOAD
2019-12-10 11:02:47.014 -0500 [DEBG]: { 6: }: ikev2_process_child_notify(0x7ff5f1bbaea0, 0x7ff5e25b7b60), notify type INVALID_KE_PAYLOAD
2019-12-10 11:02:47.014 -0500 [PWRN]: { 6: }: 17 is not a child notify type
2019-12-10 11:02:47.014 -0500 [DEBG]: { 6: 63}: construct TS_r 10.127.0.0 -> 10.127.255.255
2019-12-10 11:02:47.014 -0500 [DEBG]: { 6: 63}: construct TS_i 10.16.48.0 -> 10.16.55.255
There is 1 tunnel with 3 'sub-tunnels'
The other side has a Cisco ASA. The users connect to 10.16.48.0/21, which is a Citrix Netscaler. They click on one of their apps which takes them to the 10.65.204.0 network.
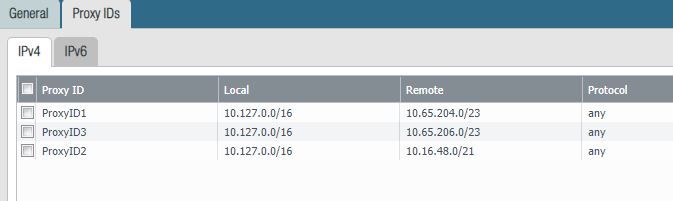
Below is the ProxyID.
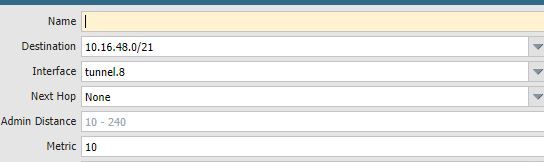
I also have static routes for the tunnel traffic
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 06:44 AM
Are these 3 proxy ids identical on the Cisco side, or perhaps you super-netted them?
I do not see any info (or rather, not enough info) in your snippet of logs to confirm that proxyID2 is not up and operational.
Do you have anything to show us errors/warning/messages surrounding this.
Lastly.. (and may this is the key)
You have 3 static routes, pointing to tunnel.8 (yes)?
Again, we do not have the screen captures to confirm this.
Please advise and lets keep working on this. 😛
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 09:51 AM
Yes, I have 3 static routes going to tunnel.8
On the Cisco side, it uses access-list. You create the tunnel and then you give the remote side (which is us) what access it has. I have access to the following networks.
extended permit ip 10.16.48.0 255.255.248.0 10.127.0.0 255.255.0.0
extended permit ip 10.65.204.0 255.255.254.0 10.127.0.0 255.255.0.0
extended permit ip 10.65.206.0 255.255.254.0 10.127.0.0 255.255.0.0
id: 67
type: IPSec
gateway id: 6
local ip: 40.135.184.5
peer ip: 166.109.10.2
inner interface: tunnel.8
outer interface: ethernet1/1
state: init
session: 197787
tunnel mtu: 1448
soft lifetime: N/A
hard lifetime: N/A
lifetime remain: N/A
lifesize remain: N/A
monitor: off
monitor packets seen: 0
monitor packets reply:0
en/decap context: 3855
local spi: 00000000
remote spi: 00000000
key type: auto key
protocol: ESP
auth algorithm: NOT ESTABLISHED
enc algorithm: NOT ESTABLISHED
proxy-id:
local ip: 10.127.0.0/16
remote ip: 10.16.48.0/21
protocol: 0
local port: 0
remote port: 0
anti replay check: yes
copy tos: no
enable gre encap: no
authentication errors: 0
decryption errors: 0
inner packet warnings: 0
replay packets: 0
packets received
when lifetime expired:0
when lifesize expired:0
sending sequence: 0
receive sequence: 0
encap packets: 0
decap packets: 0
encap bytes: 0
decap bytes: 0
key acquire requests: 59
owner state: 0
owner cpuid: s1dp0
ownership: 1
I got on a call with tech support and this error message: INVALID_KE_PAYLOAD is due to a different DH-Group.
After the call, I verified with the other side and we both have the same group.
What I find interesting is that we have another tunnel and on the other side they also have a Cisco ASA. I have 5 proxyID's and they all work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 10:06 AM
Hi John
A few things (that you are already aware of...) but need to shed light on them.
The state of the VPN on the PANW side is
state: init
Meaning that the PANW is attempting to xmit traffic to setup the tunnel.
This does not make sense if you stated that proxyID is working.
You cannot have an "init" on a firewall with a working VPN.
What am I missing.
Do you have time for an actual phone call..
You can send me a PM and we can take a look at this.
If you have remote desktop (zoom, webex, etc) that would be great as well.
Let me know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 10:48 AM
I have to step out now. I can send you a PM on Thurs. I do not have a zoom account.
You are right, I cannot make sense of this. If I delete Proxy-1 that goes to 10.64.204.0 and create another ProxyID that goes to 10.16.48.0. This works. Somehow the PANW does not like both of these proxies working together.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2019 10:55 AM
If you can schedule for later in day (after 4pm EST) that works best for me.
I have Zoom.
email me at steven.cantwell@cloudharmonics.com and I will schedule it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-04-2020 03:07 PM
What was the end resolution to this? I'm having this identical problem with a tunnel to a Cisco ASA. I have 4 proxy ID's and only one will work. If i clear the tunnel and start with a different host it too will work but the others won't. This post says resolved but I don't see the resolution. Thanks
Scot
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-08-2020 01:16 PM
Scottt
Ensure all 4 remote networks (from the Cisco side) are configured as Proxy IDs in the PANW FW.
Ensure that the routing table on the PANW shows 4 routes, one for each proxy ID network, that you created.
Thanks
Steve
- 1 accepted solution
- 9567 Views
- 9 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect Gateway behind reverse proxy in GlobalProtect Discussions
- Prisma Access Explicit Proxy — Anti‑Spyware behavior when DNS bypasses Prisma (logging subtype + test methodology) in Prisma Access Discussions
- GloablProtect + Explicit Proxy blocks WSL traffic. in Prisma Access Discussions
- DNS-Proxy vs management dns queries in Next-Generation Firewall Discussions
- SSH Proxy Decryption issue in Next-Generation Firewall Discussions