- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Whitelisting o365
- LIVEcommunity
- Discussions
- General Topics
- Whitelisting o365
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2016 12:22 PM
I want to make sure I understand the workflow on this correctly. To whitelist o365 I would perform the following:
1) Clone the o365 miners I want, prefixing them with wl
2) Edit the input for wlwhitelist and add the wlo365 miners I created.
Is there anything I'm missing here?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2016 02:03 AM
Hi chirsf,
no, this is the best way to do it. Basically you should:
- create the o365 Miners *without* wl prefix
- create an aggregator *with* wl prefix
- attach your wl aggregator to your threat indicators aggregator
I would also define a static list Miner for each wl aggregator to use for manually whitelist false positives.
Something like the schema below:
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2016 01:15 PM
Hi chrisf,
let's say you are aggregating multiple C2 IPv4 feeds using an aggregator node called C2Aggregator. You want to whitelist o365 IPs to avoid blacklisting o365 by mistake. Steps:
- create a new o365 Miner and prefix the name with "wl". Like wlO365
- select the INPUT fields of C2Aggregator and add wlO365
- COMMIT
C2Aggregator will consider IPv4 addresses/networks coming from wlO365 as whitelist and will remove the C2 indicators overlapping the o365 networks from the aggregated feed.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2016 01:23 PM
OK to take that one step further. Say I have 25 whitelist miners and I want to add them to a single aggregator, and then any time I bring up a new aggregator I wanted to point the wlAggregator as an input. Would this work?
Ideally I could white list all internal ip ranges, then anything for services required by the business.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2016 01:30 PM
Never tried, but it should work.
Note: aggregators for domains and URLs currently (0.9.22) do not support pattern matching. That means you can't use *.example.com to whitelist all the indicators with domain example.com.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-26-2016 03:16 PM
My goal would be not to have to add 25 whitelisted miners to every single aggregator since I'd likely want to globally whitelist. Is there a better way to go about this?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2016 02:03 AM
Hi chirsf,
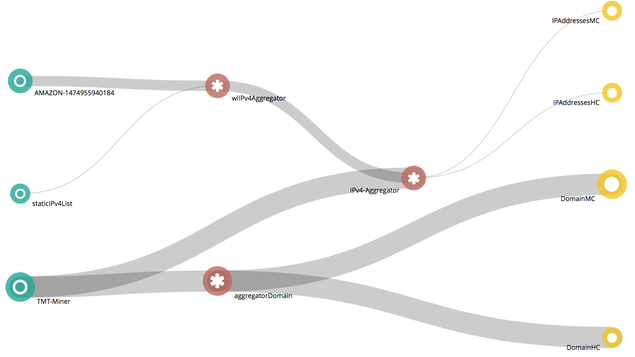
no, this is the best way to do it. Basically you should:
- create the o365 Miners *without* wl prefix
- create an aggregator *with* wl prefix
- attach your wl aggregator to your threat indicators aggregator
I would also define a static list Miner for each wl aggregator to use for manually whitelist false positives.
Something like the schema below:
- 1 accepted solution
- 6850 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Configuration/Whitelistings accross mutliple Cortex Tenants in Cortex XDR Discussions
- O365 Email integration question in Cortex XSIAM Discussions
- GUEST WIFI for new client in Next-Generation Firewall Discussions
- Blocking Google in General Topics
- XDR as "SIEM" (challenge for discussion) in Cortex XDR Discussions