- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Elaboration on the differences between the PAN-OS root certificate, the device certificate, and the certificate under cert management?
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- Re: Elaboration on the differences between the PAN-OS root certificate, the device certificate, and the certificate under cert management?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Elaboration on the differences between the PAN-OS root certificate, the device certificate, and the certificate under cert management?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-10-2024 01:09 AM
I've been requested to get as much information as I can on this topic, and I've found a good one on Reddit.
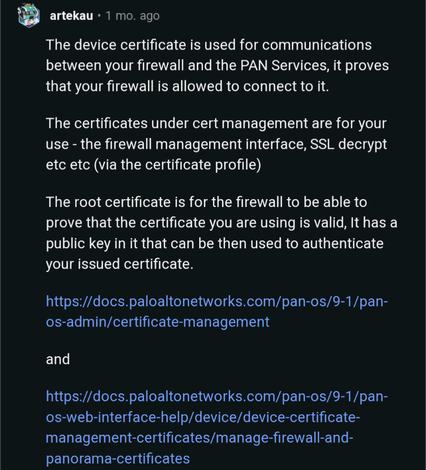
It's great, but somehow I still need much more elaboration on this.
Could anyone provide me a document that elaborates on the differences between the PAN-OS root certificate, the device certificate, and the certificate under cert management?
I've contacted TAC support, but they seem to be a bit unresponsive.
Thank you
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-04-2024 02:49 PM
Hello @MFEC - there are lots of different certificates in use within PAN-OS, and I'm not aware of a singular document describing them all and what they are all there to do. Generally speaking though:
- Root certificates are generally installed on the devices in order to provide a chain of trust for the client - in this case, the NGFW or Panorama or similar - to a server. These servers will typically in our case be cloud-delivered security services (WildFire, Advanced WildFire, URL Filtering, and similar), or used for authenticating the server to the client for things like content updates, firmware updates, and the like. They're, in many cases, not visible directly - you can see them in a packet capture, but in many cases there is no accessible CLI or GUI option to look at them. In many cases they're very long lived.
- Default certificates are something we're generally trying to move away from, and our best practice advice is to install custom or device certificates where you can. These are typically used to authenticate the device (NGFW, Panorama, etc) against some other service, be it CDSS or similar. Again, these tend to be long lived, and tend not to be that visible in the CLI or GUI.
- Device certificates are used to provide a stronger chain of trust than a default certificate: they're generally short lived (90 days, with refresh occurring between 75 and 90 days), and automatically installed and replaced once the initial certificate has been generated. These provide mutual authentication of the client against the server (ie, NGFW to a cloud-delivered security service or similar). In some cases and in newer code releases there are commands to see these certificates and their remaining lifetime.
- Custom certificates can be used for mutual, internal authentication - for example, Panorama to NGFW and vice-versa. These can generally be tied to an organisational CA, and allow customers to comply with their own authentication and encryption policies without so much dependence on Palo Alto Networks' services. The scope and use of these was expanded significantly with and beyond 10.0, to include various forms of content redistribution (that is, things like User-ID redistribution between firewalls or between firewalls and Panorama). These are visible in and manageable from the GUI and CLI.
- Certificates under certificate management can form part of an SSL inspection regime, and again can be tied to an enterprise or organisational CA. They can also be used for things like device/user authentication. Again, visible in and manageable from the GUI and CLI.
I hope this helps?
Senior Customer Success Engineer, NGFW, Palo Alto Networks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-17-2024 04:10 AM
@iarobertson I have a question on using "predefined" certificate and custom certificate for secure communication between NGFW and Panorama. In one of my project even for Internal CA they are charging commercially. And we will be deploying NGFW 400+ in numbers. In such cases Can we go for "predefined" certificate also we need to do rotation of SSL certificate for firewall management every 90 days or year. What would be Paloalo Best BPA recommendation
For Firewall Management Web Interface [Web GUI] If we want to avoid warning pop-ups, do we need to generate CSR for each firewall[400+] and get Inter CA singed, that CA [.pem/.cert+PFA] to install all the firewall [such in case from Device Template] again its cost involved for each CSR].
Any cost effective and Best practice approach?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-17-2024 04:22 PM
Hello @ramakrishnan.v05 - In general, SSL best practice is not to share or reuse device or server certificates or any private key material, and current best practice advice is to rotate these certificates every 90 days. However, your security posture should define your level of accepted risk, and with that your willingness to trade off best practices against practical matters such as commercial or operational considerations.
Senior Customer Success Engineer, NGFW, Palo Alto Networks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-17-2024 10:08 PM - edited 04-18-2024 12:11 AM
Thanks for your response. It's got clear now. I need some validation on the below option. I have three options in this case w.r.t commercial and operation overhead.
Option1: “Predefined” –> In this method No device certificate is configured, and the default predefined certificate is used.
Question: Need some clarity on this device certificate vs predefined certificate both are same? Is that not manageable, correct?
Option2: “Local” [self-signed Root CA – signed by self-entity] - > In this method the firewall uses a local device certificate and the corresponding private key generated on the firewall, this can be a common certificate used by all firewall that will connect to Panorama communication. Is that something BPA recommends it.
High level steps:
- Generate a Self-Signed Root CA Certificate on the Firewall/Panorama
- Create a Client Certificate Signed by the Root CA
- Export the Root CA Certificate [.pem/.crt] format.
- Import the Root CA Certificate into Panorama
- On FW configure under secure communication > choose client certificate
- On Panorama under secure communication > create SSL/TLS profile, then select imported root certificate.
Question: Will this word technically?
Option 3: “Custom Certificate” [Root CA -signed by Intern CA] - > Consider control does not allow to use device certificate. In this method, will generate a CSR in Panorama as common name, get that signed Root CA then trust will be established with generating client certificate, install on all firewalls.
High level steps:
- Generate a CSR with common name with Panorama and send to Internal CA for signing
- Then import both signed and CA certificate on Panorama
- On Panorama and firewall under secure communication > create SSL/TLS profile, then select imported certificates
Regards,
Ram
- 5189 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Multi-VSYS 11.2.8 - How to assign a dedicated Forward Trust Certificate per VSYS for SSL Decryption in Next-Generation Firewall Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- NGFW unable to fetch device certificate due to bug in Next-Generation Firewall Discussions
- Decryption policies and Short-Lived Certificates in Next-Generation Firewall Discussions




