- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- Who Me Too'd this topic
Who Me Too'd this topic
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-23-2018 08:36 AM - edited 10-24-2018 02:46 PM
Hello folks,
I am so close to a successful AWS IPSec tunnel to my on premise (test) PA200 7.1.15.
I've downloaded the configuration file and using it as a guide, IPs, etc.
But I've been using this article to configure. Main difference is I created a specific AWS zone like I do for all my IPSec Tunnels.
http://www.richardyau.com/?p=240
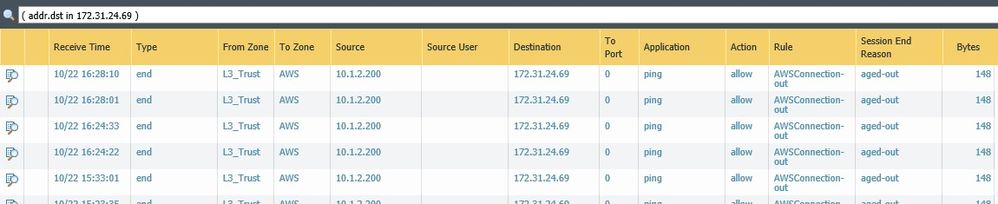
I am able to access my on premise environment from the AWS EC2 instance, but not from on premise to AWS EC2 172.31.24.69.
I can't ping it or connect to the EC2 via RDP. I see the ping tries in traffic log, but nothing shows up in packet trace for the RDP attempts. <UPDATE> Resolved after correcting IPs for PBF and RDP connection from LAN.
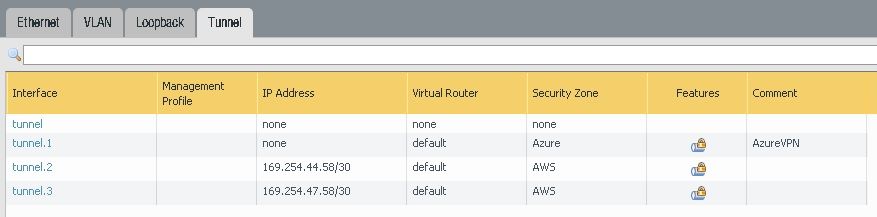
AWS has two VPN connections for redundancy. I have both configured and active.
NOTE: My Azure IPSec tunnel works great!
Configured tunnel interfaces according to AWS text document.
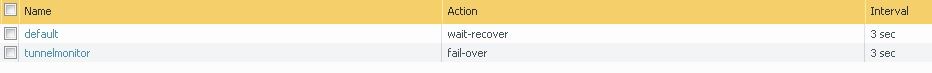
Configured tunnel monitor profile.
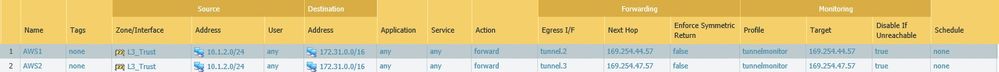
Configured PBF like referenced in documentation. <Corrected>
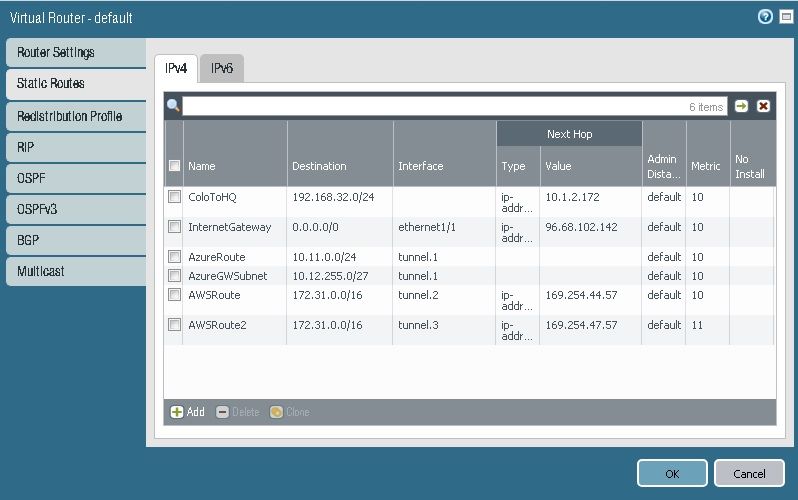
Configured Static routes for both VPN connections (different metric).
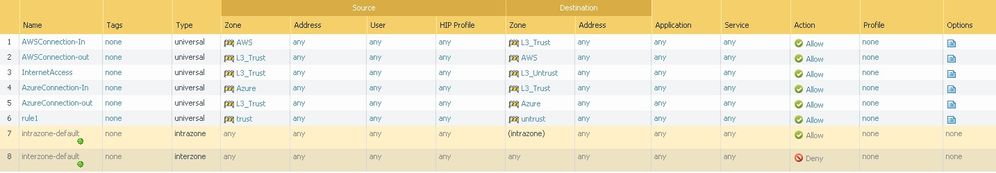
Created security rules in and out for AWS zone, open.
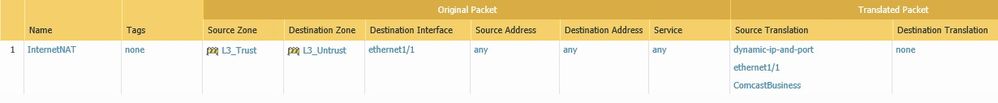
No additional NAT rules. Just basic outbound internet rule to Untrust. <corrected>
A ping from a VM inside my LAN ages out. Nothing shows up when I try to RDP, including a packet trace, not even a drop file.