
- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Microsoft outlines their connectivity principles to ensure optimal connectivity to Office 365 resources. By utilizing Cortex XSOAR with Prisma Access, these principles can be followed without continued manual effort. You can read more on Microsoft’s 365 Connectivity Principles here.
Please note that following these principles will allow all IP addresses and URLs in the feeds and bypass some of them from inspection. Organizations should carefully review the feed contents to ensure policy compliance.
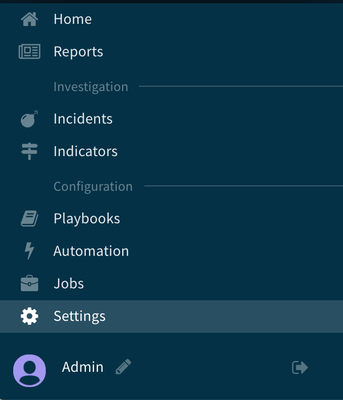
We will start our configuration in the XSOAR console, note that a Threat Intelligence Management license is required. From the menu on the left, select Settings.
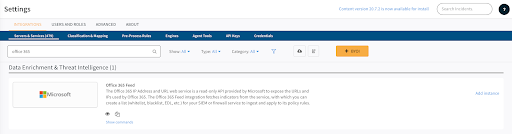
On the settings page, ensure Servers & Services is selected from the Integrations tab. In the search box, type “Office 365”
The Office 365 feed should appear in the results, click Add Instance.
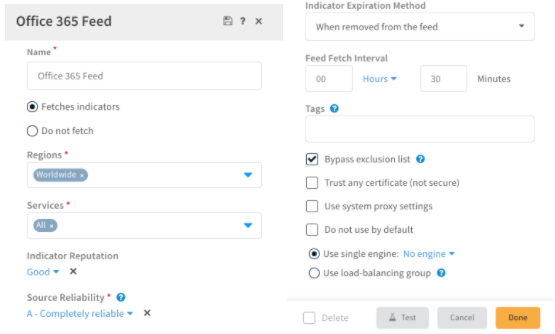
On the Office 365 Feed configuration window, enter a name for the feed. Make note of this feed name for later use. All of the default settings can be kept unless you have a specific need to change them. Click Done.
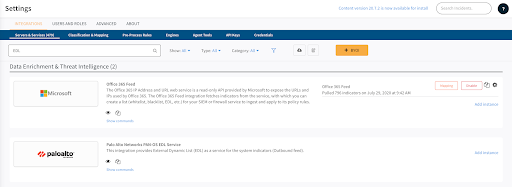
Now that we have configured the Office 365 feed, we will configure the external dynamic list service to use with Prisma Access.
Back on the Servers & Services Settings page, type “EDL” in the search box. The option for Palo Alto Networks PAN-OS EDL Service should appear. Click Add Instance on the right side of the page.
We will start by creating the EDL for Office 365 URLs to use in our Optimize/Allow traffic handling policy. From the PAN-OS EDL configuration window, enter a name for the EDL feed and the following Indicator Query:
sourceBrands:"Office 365 Feed" and (type:Domain or type:DomainGlob) and (office365category:Optimize or office365category:Allow)
NOTE: the sourceBrands section must match the name of you entered for the Office 365 feed. In our example we used “Office 365 Feed.”
Enter a unique port number in the Listen Port field, other settings can be left as default unless you have a need to modify them.
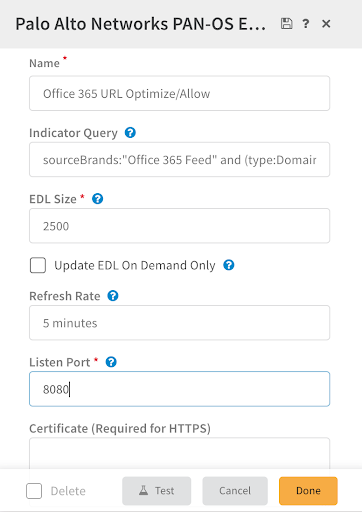
Repeat the EDL configuration three more times for using the following queries. This will configure additional feeds for Optimize/Allow handling IP addresses, Default handling for URLs, and Default handling for IP addresses. Don’t forget to modify your queries with the correct name for your Office 365 feed and use unique ports for each feed.
IPs:
sourceBrands:"Office 365 Feed" and (type:CIDR or type:IPv6CIDR) and (office365category:Optimize or office365category:Allow)
URL:
sourceBrands:"Office 365 Feed" and (type:Domain or type:DomainGlob) and office365category:Default
IPs:
sourceBrands:"Office 365 Feed" and (type:CIDR or type:IPv6CIDR) and office365category:Default
Once these feeds have been configured, you can preview them by visiting the address of your Cortex XSOAR server and the port number you configured. Here is a snippet from the Allow/Optimize URL feed:
officeapps.live.com
*.officeapps.live.com
officeapps.live.com
*.officeapps.live.com
officeapps.live.com
*.officeapps.live.com
officeapps.live.com
*.officeapps.live.com
online.office.com
*.online.office.com
msidentity.com
*.msidentity.com
officeapps.live.com
*.officeapps.live.com
manage.office.com
*.manage.office.com
lync.com
*.lync.com
msftidentity.com
*.msftidentity.com
teams.microsoft.com
*.teams.microsoft.com
portal.cloudappsecurity.com
*.portal.cloudappsecurity.com
Once you have verified that all four feeds are working as expected, switch to Panorama to complete this configuration.
From Panorama, navigate to Objects from the top menu:

On the left menu, select External Dynamic Lists:
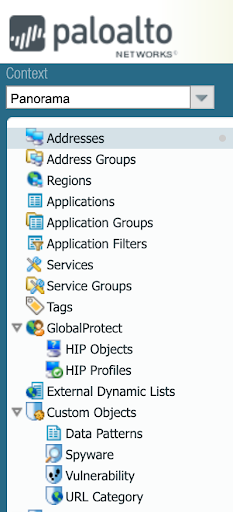
From the External Dynamic Lists page, click Add at the bottom left.

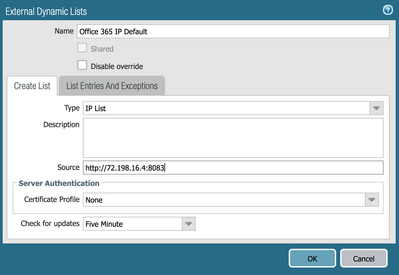
On the External Dynamic Lists window, input a name for the list. Select URL List for the type and input the address and port number of your Optimize/Allow URL feed.
Please note you may need to configure a certificate profile depending on your feed configuration in XSOAR. Learn how to configure certificate profiles here.
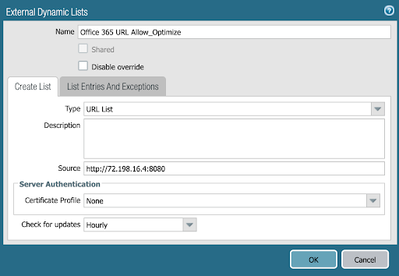
Click OK. Repeat this process for the URL Default feed: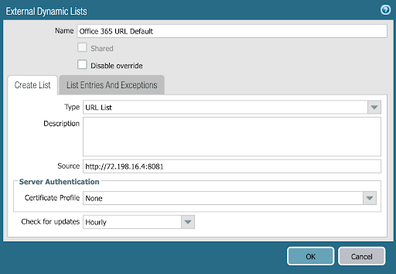
Next, we will add the IP based feeds. Click Add again from the bottom left:

On the External Dynamic Lists window, input a name for the feed. Ensure the IP List type is selected and input the address and port number of your IP optimize/allow feed.

Click OK. Repeat this process for the IP Default feed:
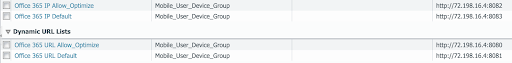
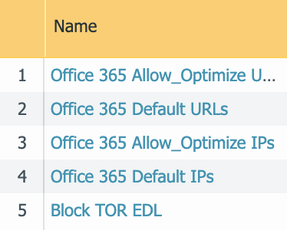
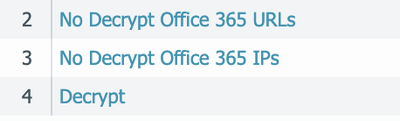
Once completed, verify that you have four different lists with four different port numbers:
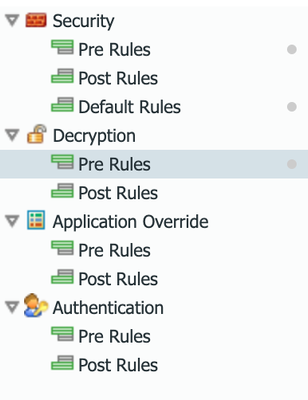
Next we will configure policies to use these EDLs. Click Policies from the top menu:

Ensure that Security > Pre Rules is selected on the left:

Click Add at the bottom left:

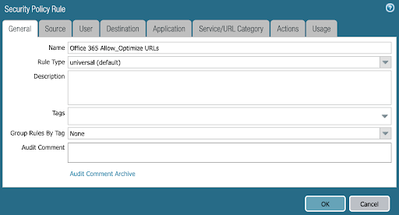
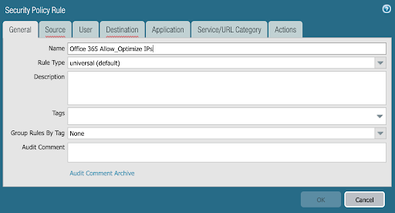
Input a name for the policy rule, then click the source tab.
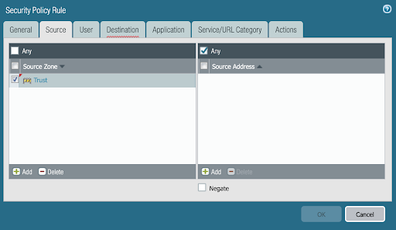
On the Source Tab, click Add and add your Trusted zone to the policy rule. Next, click the Destination Tab:
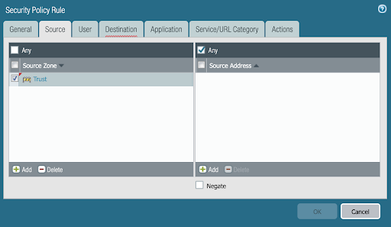
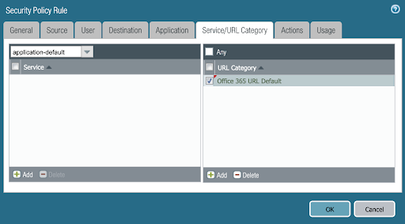
On the Destination Tab, click Add and add your UnTrust zone to the policy rule. Next, click the Service/URL Category Tab:

On the Service/URL Category Tab, click Add. Add the Office 365 URL Allow Optimize feed and then click the Actions Tab.
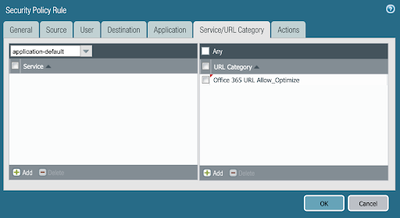
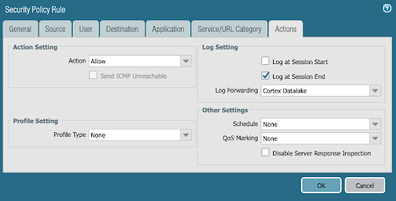
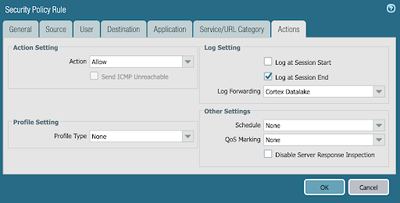
Verify the Action setting is set to Allow and configure log forwarding if desired. Click OK.
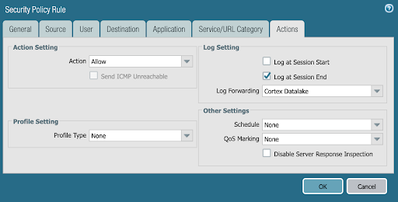
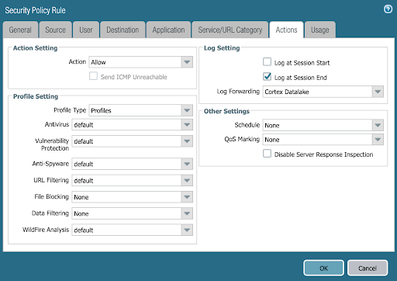
Repeat these steps to create a policy for Default URLs, selecting the Default URL EDL list on the Service/URL Category Tab. On the Actions Tab you can also specify security profiles for Default traffic.
Next we will create policies for our IP based EDL feeds. Click Add at the bottom left of the Policies page.

Input a name for the policy rule, then click the source tab.
On the Source Tab, click Add and add your Trusted zone to the policy rule. Next, click the Destination Tab:
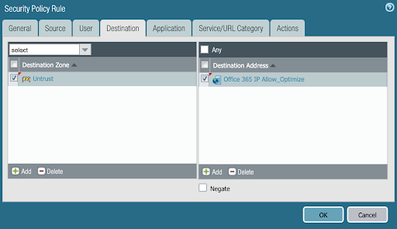
On the Destination Tab, click Add on the left and add your UnTrust zone. In the Destination Address section, click Add and add your Office 365 IP Allow Optimize EDL to the policy rule. Next, click the Actions Tab:
Verify the Action setting is set to Allow and configure log forwarding if desired. Click OK.
Repeat these steps to create a policy for Default IPs, selecting the Default IP EDL list on the Destination Tab. On the Actions Tab you can also specify security profiles for Default traffic.

Once done, you should have four newly created policies for Office 365 traffic. Ensure the policies are near the top of the list so they will be applied appropriately.
Next we will bypass the Allow/Optimize URLs and IP addresses from SSL Decryption. On the left menu, click Decryption > Pre Rules:
Click Add at the bottom left:
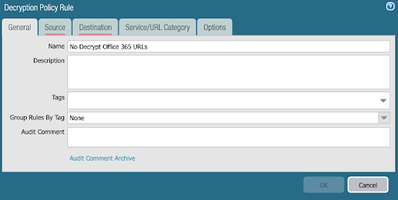
Input a name for your decryption policy rule and then click the Source tab:
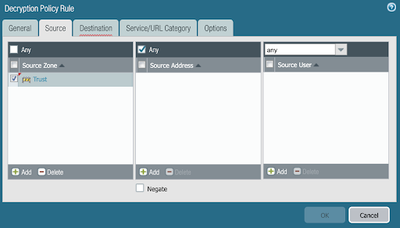
Add your Trusted zone to the Source Zone section and then click the Destination tab:
On the Destination tab, add your UnTrust zone to the Destination Zone section and then click the Service/URL Category tab.

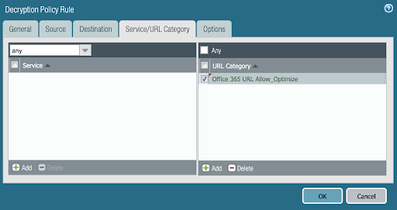
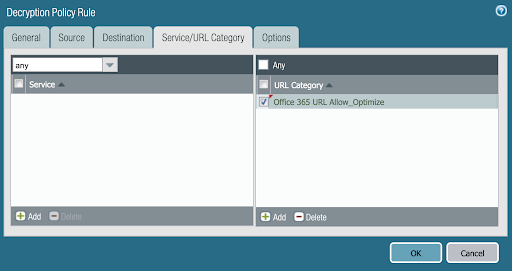
On the Service/URL Category tab, add your Office 365 Optimize/Allow EDL under URL Category, then click Options:
On the options page, ensure that No Decrypt is selected and click OK.
Click Add again on the bottom left to create the policy for IPs.
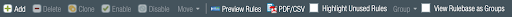
Input a name for your decryption policy rule and then click the Source tab:
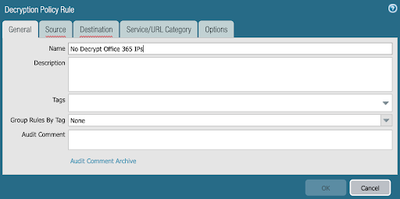
Add your Trusted zone to the Source Zone section and then click the Destination tab:
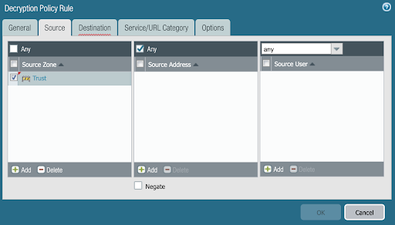
On the Destination tab, add your UnTrust zone to the Destination Zone section and your IP Optimize/Allow to the Destination Address section, then click the Options:
On the options page, ensure that No Decrypt is selected and click OK.

You should now have 2 Decryption policies for Office 365. Ensure they are above your primary decrypt policy to ensure proper application.
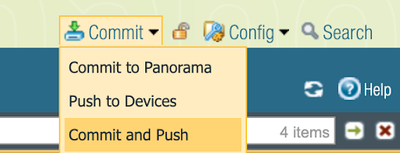
Click Commit > Commit and Push at the top left:
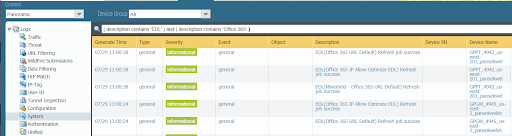
Now that you have configured the EDLs and the policies, you should see log entries for the EDL jobs if you navigate to the Monitor tab. Ensure you select Logs > System from the left side. Note that logs may take a few minutes to populate.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
| Subject | Likes |
|---|---|
| 3 Likes | |
| 2 Likes | |
| 1 Like | |
| 1 Like | |
| 1 Like |
| User | Likes Count |
|---|---|
| 3 | |
| 3 | |
| 2 | |
| 2 | |
| 1 |



