- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Nominated Discussion: Query For Routing Table
- LIVEcommunity
- Articles
- General Articles
- Nominated Discussion: Query For Routing Table
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
This Nominated Discussion Article is based on the post "Query For Routing Table" by @Matlu_NN and responded to by @seb_rupik , @Alin.Scarlat and @TomYoung. Read on to see the discussion and solution
In Palo Alto Networks Firewalls, what is the correct command in the CLI, to "validate" if I have or don't have a route, to reach a particular destination?
The correct command is "show routing route" or "show routing fib" ???
What is the command that can help me to know if my Firewall has a route to a particular destination?
The FIB is used to determine the egress interface to reach a particular destination, typically the next-hop. The routing table contains all unfiltered/permitted prefixes and their preferred next-hops.
The CLI command you want is:
show routing route
It is worth noting that the RIBs associated with dynamic routing protocols may contain additional prefixes which due to routing which have not been added to the routing table.
I want to "validate" if I have a route to reach an IP from my Firewall.
The IP is 10.7.25.107.
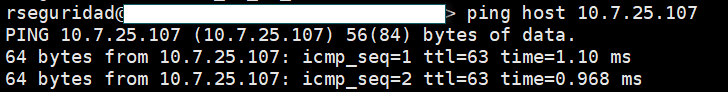
When I test the "connectivity" from the Firewall, with the command "ping host 10.7.25.107". the result is successful, but I have "understood" that this command "pulls all the traffic" through the MGMT Interface of the Firewall, is this correct?
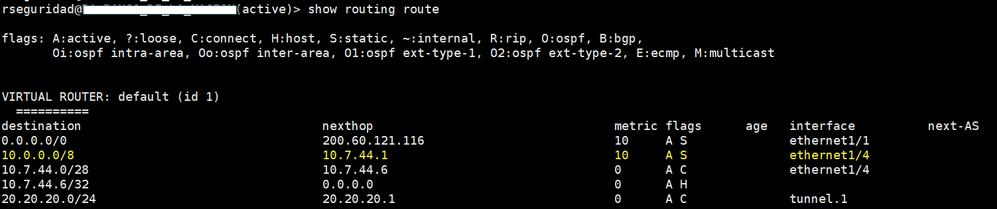
When I query the "show routing route", the command shows me the following.
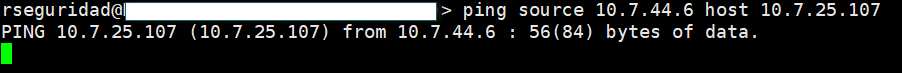
I understand from the output of the command, that to reach that destination, I do it through the ethernet interface 1/4, but I do not understand why when I do a "ping" with origin, it does not work (And according to what I understand, it should work).
I have the idea that the "ping host x.x.x.x.x" should not work, and the "ping <source> host <destination>" should work.
If the source interface is not specified then "ping host x.x.x.x" will be sourced from the management interface.
https://live.paloaltonetworks.com/t5/blogs/tips-amp-tricks-how-to-ping-from-the-cli/ba-p/468784
It is clear to me that the "ping hos x.x.x.x.x" takes out all the traffic through the mgmt interface, in my scenario, this should not happen, because for me to reach the destination 10.7.25.107, according to the routing table, I must reach it through the Ethernet1/4 interface.
So, the correct way to test the connectivity to that destination, should be with a "ping with source", that is with the command "ping source <IP of the interface Eth1/4 source 10.7.25.107" (As it is in the pictures that I attached above the case), but when you do this test, it simply does not work, and I do not understand why.
You say that traffic sourced from the mgmt interface shouldn't be able to reach 10.7.25.107, but remember that interface will probably have been configured with a default gateway. Now unless this mgmt subnet is truly out-of-band, it is highly likely that it is routed on your 'core' router. Does the router with the interface 10.7.44.1 receive the palo alto mgmt subnet via an IGP update or have a static route installed for it or an aggregate route which directs back to your 'core' router? It would be great to see a topology to determine if this path is not possible.
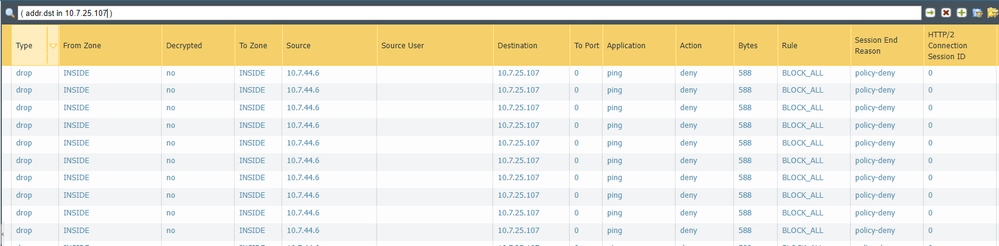
Regarding using the ping command and specifying the Eth1/4 interface IP, what does your security policy look like? Is intra-zone communication permitted? If not, then does a rule exist to permit icmp/ping sourced from your eth1/4 interface ?
Is it necessary to have a security rule to allow traffic from the Ethernet1/4 Interface for ping tests to my destination 10.7.25.107?????
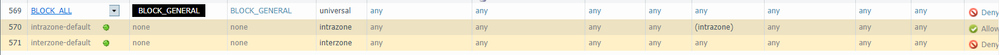
I have checked the rules, and also the logs, and this is what I found.
It is necessary to create an explicit rule to allow me to simply ping from the eth1/4 interface to my destination ????.
What I do not understand so far, is why the "PING HOST X.X.X.X.X" responds me positively, if in the routes, I do not have any evidence that to reach this destination, I do it by the MGMT.
Unfortunately, I do not have the routes of the router with IP 10.7.44.1
The default intra-zone permit rule would have allowed this particular flow to work, but as you have shown, your 'BLOCK-ALL' rule is denying it.
Since you are pinging within the subnet from the eth1/4 interface this is covered by the intra-zone rule which cannot be reached, so yes, you need to explicitly permit it.
Regarding the mgmt interface routing, this does sound like a case of that particular prefix being advertised explicitly or as part of an aggregate to the other router.
Can you share the routing table of the router which has the DGW interface for the mgmt subnet? Also what is the mgmt subnet Id?
Unfortunately the router that is the DGW of the MGMT interface, is managed by another "Team", and I do not have that information now, but I will talk to them to provide me the route that they have from their equipment, to reach the IP that has my MGMT interface of the Firewall.
Is this type of scenario common?
I mean, if I validate that to get to any destination, I leave through a specific interface (any, for example eth1/5, eth1/8, etc], and if I want to test PING with ORIGIN, from the Firewall CLI, I must always have an Intazone rule enabled and in "permit"?????
This is as a general concept????
To understand why in my case, "ping host x.z.z.z" works, you need the routing from the Router, right?
For now, I can assume that for any kind of traffic to reach my specific destination, it is going out on the eth1/4 interface????.
Looking at your screenshots,I notice that the zone which your destination IP resides is 'Inside'. Your mgmt subnet even if not part of the inside zone is clearly going to be routed on a router somewhere in this inside zone. This makes your mgmt subnet and the destination IP subnet highly likely to exist on the same routing table.
Has your mgmt subnet been sold to you as out of band ?
Regarding your intra-zone question, a ping is typically sourced from the interface 'closest' to the destination, for this reason it will typically be an intra-zone flow. Arguably you could source the ping from another interface in a different zone therefore requiring an inter-zone rule.
The default intra-zone rule is set to permit, and unless you override it or place a block above it, this scenario wouldn't normally be a problem.
I'd wager that most firewall admins have a setup like yours, which necessitates an explicit rule for every flow, even those originating from the firewall. Life is better this way!
Your final assumption is correct, for that particular prefix the FIB would ensure that your packets leave via Eth1/4, unless they come from a ping flow initiated on the CLI !
Right now, I have no idea, if the MGMT interface, was "sold" as "Out of band".
Is this something I should check with the project implementer?
Or can I answer this question myself by checking the configuration?The only thing I know is that the Firewall model, which is a 3020, has a dedicated leg to be MGMT.
In your experience, I ask you 2 questions.
When you have connectivity problems between a source and a destination, and you want to validate if that destination is "available or reachable" from the Firewall point of view, you do troubleshooting tests, involving the simple PING from the FW CLI ?
For you to validate if you have a route or not, to reach a destination, from the FW, it is valid to use the command "show routing route"?I still have pending, the routing table of the Router that GW from the MGMT of the FW.
For troubleshooting connectivity, you first want to check that a valid route exists (your CLI command is valid for this, or the virtual router runtime info via the webgui). I would then start looking at security policy, traffic monitor logs, session browser, packet capture and policy match troubleshooting. As you have seen from the ping command, trying to troubleshooting connectivity from the firewall does not give a representative test.
I got this information regarding the SwitchCore machine that has the IP 10.7.44.1, which is the GW of my Palo Alto.
The Router with IP 10.7.44.1, knows my MGMT IP (eth1/4 of the FW), by a static route, as I show you in the following image.
All your explanation is clear, I just want to give "sense" to the explanation of why the "ping host 10.7.25.107" works, if according to the routing table, to reach that destination, I must leave through the eth1/4 interface and it does not work, but it seems that it does reach that destination through the MGMT interface of the Firewall (with IP 10.7.15.166).
Your image only gives half the picture, but lets assume the routing table on the 'inside' router also includes the FW Eth1/4 subnet.
On the firewall when you issue the 'ping host xxx' command, the traffic is sourced on the MGMT interface, the next-hop is the router shown in your screenshot. I'd imagine the the destination subnet 10.7.25.0/24 (?) is also directly routed on this router, you therefore have a routable path with not security policy to get in the way.
When you use the 'ping source <eth1/4_ip> host xx' command, traffic should egress the firewall towards the inside router and then onto the destination subnet, again you have a routable path between the endpoints. The issue you have when sourcing from any interface other than mgmt0 is that an intra-zone policy must exist to permit those flows.
Another point that is probably worth looking at is that your mgmt interface is not out-of-band and can be reached by any 'inside' device. Without re-architecting your logical design, I suggest you edit the allowed-hots ACL on that interface to permit access from an operations subnet/ jump box.
- 3610 Views
- 0 comments
- 0 Likes
- Nominated Discussion: Configure Split Tunneling by Domain in General Articles
- Nominated Discussion - Sorting Question in General Articles
- Nominated Discussion: Using the REST API to Create a Bunch of Address Objects in General Articles
- A Guide to NAT on Palo Alto Networks Firewalls in Support FAQ
- Nominated Discussion: Check Which IP Address (or User, AD Group) is Utilizing More Bandwidth in General Articles
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
ADNS
1 -
Advanced DNS Security
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
2 -
AI Security
1 -
AI Threat
1 -
AIOPS
1 -
Analytics
1 -
Ansible
2 -
antivirus
1 -
API
2 -
API & SDK
1 -
App-ID
1 -
applications
2 -
APS
1 -
Artificial Intelligence
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
6 -
AWS
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
7 -
Block List
1 -
Cardinality
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CI CD Integration
1 -
CICD integration
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud ngfw
1 -
Cloud security
2 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Configuration
8 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Container
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
Cortex XSIAM
1 -
Cortex XSOAR
2 -
CPSP
1 -
Custom Signatures
3 -
custom-featured-post
1 -
cyber elite
1 -
cyberelite
13 -
Cybersecurity
1 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
DLP
1 -
Docker
2 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
End to End Encryption
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
3 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
GKE
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
4 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
HyperLogLog
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector Design
2 -
Log Management
1 -
Logging
1 -
login
1 -
Logs
3 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
Network Security
35 -
Network Security Management
1 -
Network-Security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
31 -
NGFW Configuration
12 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Prisma Access
1 -
Panorama
12 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
7 -
Prisma AIRS
1 -
Prisma SASE
2 -
Prisma SD-WAN
1 -
proactive insights
2 -
Prompt Poaching
1 -
Public Cloud
1 -
Python
2 -
Radius
1 -
Ransomware
1 -
RBI
2 -
region
1 -
Registration
1 -
Remote Browser Isolation
3 -
Reporting
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Site-to-Site VPN
1 -
Software Firewalls
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
2 -
Strata Logging Service (SLS)
1 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Terraform
3 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
7 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
Upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
8 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WhatsApp
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next