- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect ip-user-mapping issue
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect ip-user-mapping issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
GlobalProtect ip-user-mapping issue
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2013 02:36 AM
PA-500
PAN-OS 5.0.2
Hello, we've deployed GlobalProtect with local user authentication (authentication profile = local database), user identification is enabled both on trust and vpnclient zones.
Also, user mapping is enabled with UID Agent directly from the firewall.
Everything's working fine with vpn authentication, once connected the client shows up as the LOCAL user as expected:
IP address: 10.1.253.10 (vsys1) <<<<<<<<<<<<< assigned ip address range is 10.1.253.0/24
User: abcde <<<<<<<<<<<<<<<<<< this is in the local user database
From: GP
Idle Timeout: 2591965s
Max. TTL: 2591965s
Groups that the user belongs to (used in policy)
When the vpn client starts to generate traffic to/from internal lan accessing active directory resources (i.e. remote desktop or network shares) it has to authenticate towards Active Directory with domain credentials.
This obviously also generates security logs on the DCs, which are read by onboard UID agents causing ip-user-mapping to change from LOCAL user to AD user for the same ip address:
IP address: 10.1.253.10 (vsys1)
User: testdomain\testuser <<<<<<<<<<<<<<<<< this is the AD account used to authenticate when accessing internal lan resources
From: AD
Idle Timeout: 2699s
Max. TTL: 2696s
Groups that the user belongs to (used in policy)
Group(s): cn=vpn_users-all,ou=vpn,dc=testdomain,dc=local
This is causing issues since security policies for vpn clients are setup with LOCAL users and not AD users, as obviuos.
I'm aware that using AD authentication for GlobalProtect would be advisable, but now we have to keep on with local user authentication.
Haw can we prevent AD user-ip-mapping from overwriting the initial (correct) GlobalProtect mapping for vpn client network range 10.1.253.0/24?
ps: I've tried the Include/Exclude Network option in Use Mapping section by entering the exclusion for 10.1.253.0/24, but with no success.
Thank You
- Labels:
-
User-ID
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2013 10:03 AM
I have done a quick test on 5.0.1 on my PA and I do see the same behavior. I have excluded the network 10.101.101.0/24 as shown below in the running configuration from the CLI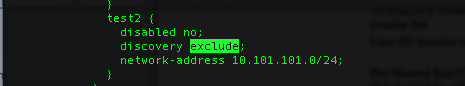
But User-IP-Mappings for the IP of the GP client 10.101.101.125 are still mapped if I access an AD inside my network as shown below
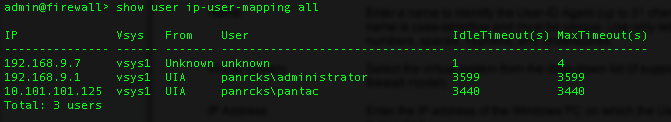
This is not working a expected. I would suggest you to open a ticket with support for further help.
Thanks,
Sandeep T
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2014 11:05 PM
hey
did you managed with this?
we are having almost the same issues.
what have you done?
thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2014 10:20 AM
Hi minov
This topis is near one year old. What version of PAN do you have installed?
Please upgarde to 5.0.9, I'm on 5.0.9 and I haven't such problems.
Regards
Slawek
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-29-2014 09:54 AM
5.0.9 i have a user authenticate through Radius, and then RDP to a server and some shares then the user-ip-mapping changes to the AD user which have different policy
- 4511 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- playbook completely stuck on a simple condition in Cortex XSOAR Discussions
- Is there a difference between issues and alerts in XQL queries? in Cortex XDR Discussions
- Palo Windows ARP Issue - Windows Hosts Not Installing ARP info in Next-Generation Firewall Discussions
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- GlobalProtect Client Quadlet in GlobalProtect Discussions




