- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
I'm unable to use Remote desktop from internet to PC in Trust zone
- LIVEcommunity
- Discussions
- General Topics
- Re: I'm unable to use Remote desktop from internet to PC in Trust zone
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2017 07:08 AM - edited 10-15-2017 07:16 AM
Hello all,
I wanna Remote desktop from my PC in home to PC in my company but not success
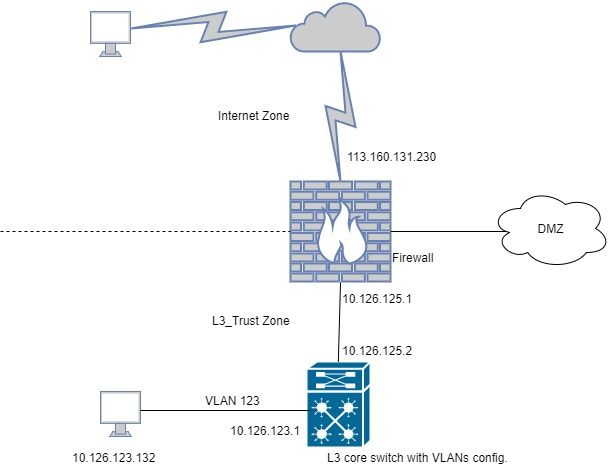
This is my connection diagram
I wanna remote to PC 10.126.123.132 (belong to VLAN 123, I use several VLANs in Core switch) but not success, NAT seems not to work, there's no traffic logs
This is my config..
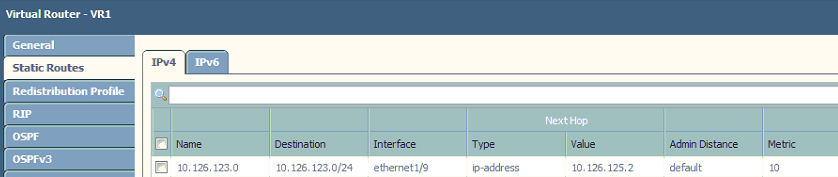

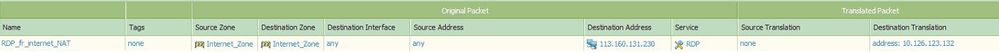
I can remote from internet to a server in DMZ zone successfully but L3_Trust zone, so I think because of using VLAN in core switch, it requires some other config.. Please help me 🙂
P/S: The public IP in the pictures is just an example IP
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-20-2017 12:44 AM
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2017 12:12 PM
In your nat rule try adding source nat 10.126.125.1.
your dmz may have a default route to the internet but maybe your vlans dont.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2017 12:35 PM
take a packet capture on the firewall and the end client.
If you see the syn packet on the end client this would mean the packet is getting forwarded to the client.
Check if you recieve a syn-ack back on the firewall from the client.
If that is not the case then , check the routing on the switch. For testing in the nat rule that you have created for inbound, source nat the traffic to the trustzone interface.
Share the output of pcaps and session if this still does not resolve
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2017 07:04 PM - edited 10-15-2017 07:06 PM
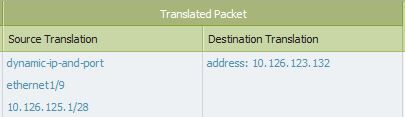
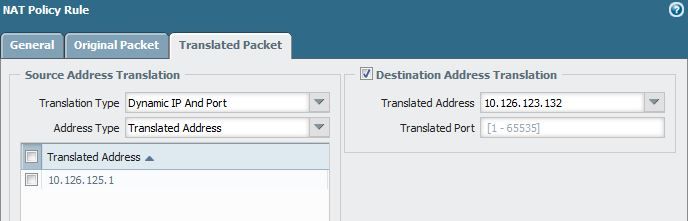
Thank you all for your help, I added source translation to IP of L3_Trust interface (10.126.125.1) but still not success when Remote Desktop 😞
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2017 07:36 PM - edited 10-15-2017 07:37 PM
at this point. take a pcap on firewall and client together. Share the details.
Provide the below details
After trying rdp connection ,in the command line type
1) show session all filter source<your_public_src_ip> destination 113.160.131.230 destination-port 3389
this command will list the running sessions and the left most column is session id. Select a session id
2) show session id<session_id>
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2017 11:06 PM
Try modifying your source translation
address type = translated address
translated address = 10.126.125.1
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 01:17 AM - edited 10-16-2017 01:20 AM
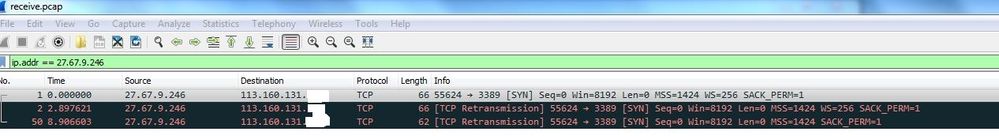
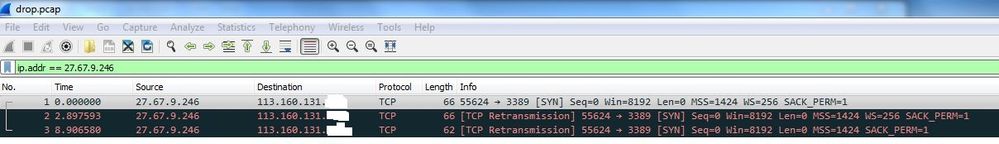
Thank you Sir, this is the picture of recive.pcap and drop.pcap, there's nothing in transmit.pcap and firewall.pcap. I'm sorry, due to security reason, I'm not allowed to upload capture file here
27.67.9.246 is my public IP from internet zone
I also run command show session all filter source<your_public_src_ip> destination 113.160.131.230 destination-port 3389 but there's no active session
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 01:19 AM
I change the source translate to "translated address" but it still not working
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 01:30 AM
from the cli.
ping source 10.126.125.1 host 10.126.123.132
do you get replies?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 01:33 AM - edited 10-16-2017 01:34 AM
Yes sir, Ping successful
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 01:56 AM
change your security policy/action/log settings to session start.
attempt a connection and find connection attempt in monitor/traffic.
if you can see the session start then select magnifying glass on left column and post
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 02:06 AM - edited 10-16-2017 02:07 AM
I've already choosen both Log at session start and end before 😞
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 02:16 AM
in your security policy, should the destination address be 10.126.123.132 and not 113.160.131.230
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 02:24 AM
I think it must be 113.160.131.230 but anyway, I tried changing it to 10.126.123.132 or any, it's not working 😞
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2017 02:48 AM
Of cource it wouldn't work...When using destination NAT, Security policy must contain PRE-NAT addresses and POST-NAT zones. Which means that your original configuration configuration is actually correct.
In my humble opinion your original configuration was correct (correct NAT and correct security policy). There was suggestion to set source NAT and I saw you have enabled source and destination - I would say this is wrong... I believe the suggestion was to configure source static nat and enable bidirectional. That way you should accomplish the same think create static NAT. But you shouldn't enable both source and destination in the same rule.
In the capture you can see that drop capture is filling with with the SYN, so
So my suggestion:
1. Put everything back as you configure it originally.
2. I saw that you are using service group RDP, can you confirm that this service group contain TCP port 3389?
3. Enable log on start for the security rule
4. Check traffic log for log matching your source address. send screenshot for this entry (you can hide the real addresses if you like)
- 1 accepted solution
- 20434 Views
- 32 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- New cert GP cert prompt for people testing Yubikeys for windows logon in GlobalProtect Discussions
- False positive (generic.ml): HelpDesk Viewer in VirusTotal
- False Positive request for RemotePC HelpDesk Viewer in VirusTotal
- False positive : HelpDesk Viewer in VirusTotal
- False positive (generic.ml): HelpDesk Viewer in VirusTotal