- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Investigation of possible threats
- LIVEcommunity
- Discussions
- General Topics
- Investigation of possible threats
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Investigation of possible threats
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-05-2016 07:31 AM - edited 11-05-2016 07:42 AM
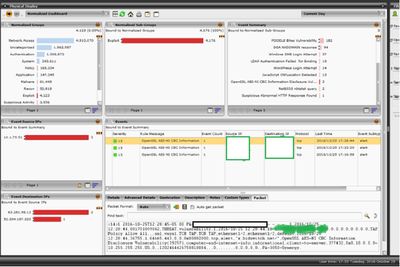
My company has a PA3050. I am new to this device. It is currently setup to mirror/monitor port on current Cisco firewall. The device is reporting that it is finding suspicous files and various other vulnerabilities. There is concern that this is showing that there is active hacker activity on the network. Is there a way to tell the difference between this being active hacker activity or if this is just logging possible vulnerabilities on the network?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2016 02:39 AM
there a way for you to share logs so we can get a feel for what you are looking at ?
the threat logs are oriented so they try to identify the 'attacker'. there is a magnifying glass at the very left of the log that shows you more details about the underlying session (traffic log + threat log correlation) which should give you an idea of where the session is coming from and where the threat is coming from (session could be client to server-http, threat could be server-http to client, which is a traditional 'download')
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2016 08:17 AM
Attached is one of the screenshots from our security team. There are others showing suspicious files or other vulnerabilities.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2016 10:01 AM
Bump. What I am wondering is if this report is telling us there are comprimised hosts or if it is just seeing vulnerabilties that may be on some of the internal hosts and that if we patch those vulnerabilities that it would disappear.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2016 11:53 AM
I'm not sure if everybody else is having the same issue but I can't actually view your image without it getting really distorted to the point I can't actually read anything.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2016 11:54 PM - edited 11-09-2016 11:55 PM
Yes, pic is very distorted. But I think we are talking about this signature:
| Name: | OpenSSL AES-NI CBC Information Disclosure Vulnerability |
| ID: | 39257 |
| Description: | OpenSSL is prone to a information leak vulnerability while parsing certain crafted SSL requests. The vulnerability is due to the implementation of AES-NI. An attacker could exploit the vulnerability by using a padding oracle attack to decrypt traffic. A successful attack could lead to leak of the server sensitive information. |
| Severity: | |
| CVE: | CVE-2016-2107 |
The description is a bit unclear whether this signature actually detects a request which could exploit this vulnerability or just notifies of use AES-NI instruction set in OpenSSL. As the severity is informational I'd assume it's just use of vulnerable instuction set.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-10-2016 01:52 PM
I was actually seeing that alert quite a bit a couple months ago; I've since stopped but I was told that it wasn't that the servers were still vulnerable to it so I imagine that it actually identifies a potential attack. Ask whoever is managing your servers if they have updated them since May, I'm guessing that they have.
- 3621 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- XSIAM Threat Intelligence Management Module in Cortex XSIAM Discussions
- Cortex XDR - Issues auto-grouping under same case due to shared IP - how to manage? in Cortex XDR Discussions
- without overwhelming in Advanced Threat Prevention Discussions
- Continuous Threat Logs Showing Management Server IP as Source in Next-Generation Firewall Discussions
- Need help on this XSOAR Weird behavior on preprocessing scripts in Cortex XSOAR Discussions