- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
PA-500 6.1.4 Policy and URL filtering
- LIVEcommunity
- Discussions
- General Topics
- PA-500 6.1.4 Policy and URL filtering
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-15-2015 11:45 PM - edited 10-15-2015 11:51 PM
Hi,
I have very big problem with my firewall. I have a few URL filtering rules which I block some of sites.
Example:
1. Allow social network(linkedin) block youtube -> name AllowSN
2. Allow youtube block social network(linkedin) -> name AllowYT
3 and so on
And I create for this URL filtering policies where specific users(by ldap) can access to specif sites.
Example:
1. AD group allow_yt -> url filtering AllowYT
2. AD group allow_sn -> url filtering AllowSN
And I have users who is in all of this groups(allow_yt,allow_sn). In this hierarchy they can access to YT but not social network but when I change policies order they can get to SN but not to YT 😞
Can someone provide information How can I improve my policies that users which are in both group can access to YT and social network?
Thanks for help.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2015 04:47 AM - edited 10-16-2015 04:49 AM
Security profiles is always my first choice because it keeps security rules cleaner.
But with your requirement you should create security profile and AD group for every possible setup.
- permit youtube
- permit social
- permit youtube and social
Pao (and firewalls in general) evaluate rules from top to bottom.
First rule matches source and destination will be taken into account.
If in first rule you allow HR department to visit social networking sites with security profile but at the same time block streaming media in the same URL filtering profile then person in HR group can never go to youtube (even if same person is also in streaming media group and you allow streaming media with next rule below).
Rules are not mixed together - only one rule will be taken into account.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2015 01:47 AM
Hi
the security policy will be processed from the top to bottom and once a positive match (source+destination+source user/group+application/port) is made, the security policy will be applied and any subsequent rules are not checked
so what you could try is to create a rule at the top that allows application youtube for the youtube group, then add the rule that allows youtube URL filtering below and then social networking
1. AD group allow_yt -> application YouTube, NO url filtering
2. AD group allow_yt -> url filtering AllowYT
3. AD group allow_sn -> url filtering AllowSN
regards
Tom
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2015 02:48 AM
Thanks for answer.
But how does it work? If security policy are processed from thr top to bottom then someone who is in the group allow_yt and allow_sn will be access to YT but not to SN.
Or am I wrong?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2015 03:23 AM
Try chaning the order
1. AD group allow_yt -> application YouTube, NO url filtering
2. AD group allow_sn -> url filtering AllowSN
3. AD group allow_yt -> url filtering AllowYT
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2015 03:24 AM - edited 10-16-2015 03:28 AM
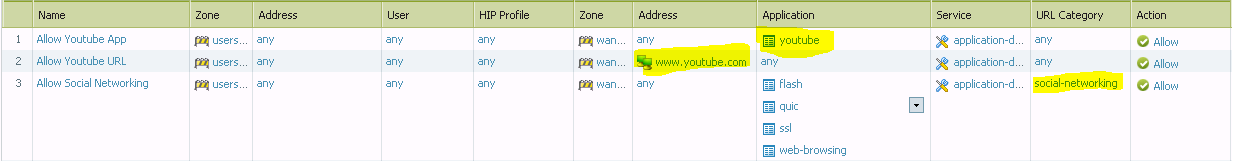
You can start with something like this and then tighten it down (allow only limited applications like youtube, web-browsing, ssl etc from www.youtube.com and permit only limited social-networking FQDN's etc).
And change User-Any to your AD group accordingly.
So first 2 rules source user is youtube group and third is social networkng group.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2015 04:47 AM - edited 10-16-2015 04:49 AM
Security profiles is always my first choice because it keeps security rules cleaner.
But with your requirement you should create security profile and AD group for every possible setup.
- permit youtube
- permit social
- permit youtube and social
Pao (and firewalls in general) evaluate rules from top to bottom.
First rule matches source and destination will be taken into account.
If in first rule you allow HR department to visit social networking sites with security profile but at the same time block streaming media in the same URL filtering profile then person in HR group can never go to youtube (even if same person is also in streaming media group and you allow streaming media with next rule below).
Rules are not mixed together - only one rule will be taken into account.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2015 04:52 AM - edited 10-16-2015 04:53 AM
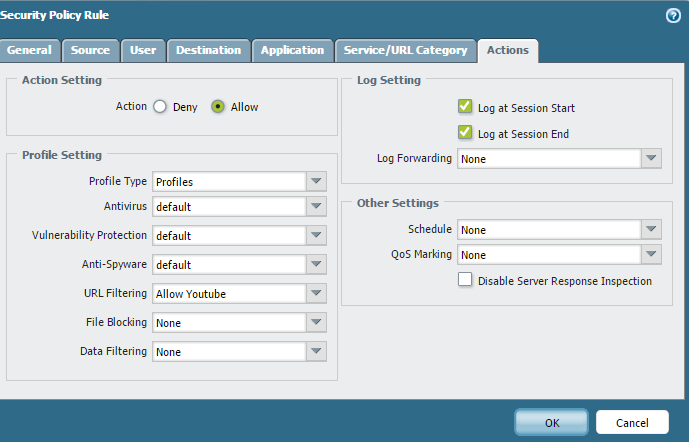
By the way "log at session start" should be used only for troubleshooting purpouses.
It generates a lot more log (every application shift) so your log will fill up faster and you can't go back as long as you could with less logging.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-16-2015 05:53 AM
The firewall is a security tool. We should be first asking what's important...What's critical to have. It's annoying that everytime I'm on a TAC call I usually get the "you really shouldn't log on session start" comment.
The problem with not logging on session start is you're only notified when the session has ended (obvious.) The problem with saying "only use it for troubleshooting" is how do you troubleshoot something in the past?
Say for instance an FTP session, that session could be open for minutes, hours, or even days. You'd never be notified about that traffic until the session was closed.
Every one of my rules logs session start. Over 20k user network and we generate about 3 million logs a day. Our Panorama has 2TB of storage and we just shy of 2 months of on box retention.
- 1 accepted solution
- 5352 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- XFF IP Address Logging clarification and impact in General Topics
- Not able to log XFF (Actual Client IP) in PaloAlto Logs even when we enable XFF and URL filtering profile in Palo's in Next-Generation Firewall Discussions
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions
- We are trying to allow particular website to particular user but the same is not occuring in Advanced URL Filtering Discussions
- Policy destination field when using URL filtering in Next-Generation Firewall Discussions