- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Prioritize Tunnel Static Route over L2 physical route
- LIVEcommunity
- Discussions
- General Topics
- Prioritize Tunnel Static Route over L2 physical route
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Prioritize Tunnel Static Route over L2 physical route
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-09-2023 04:56 AM
Hi,
I have an IPSec Tunnel between a remote central site and a PA-220.
This tunnel advertises it's remote internal network in 10.100.10.0/27.
A static route has been created in the PA with a metric > 1 (10), to route traffic in direction of 10.100.10.0/27, through the IPSec tunnel interface, tun.254.
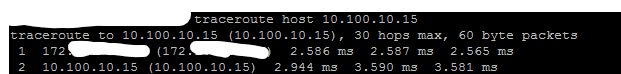
This route is effectively working, as an ICMP trace shows traffic flowing from the tunnel local IKE Peer interface (172.X.X.X) to a remote network host (10.100.10.15).
Now here is where things gets problematic, we also have a physical network directly connected to the PA appliance, covering all the range of the 10.0.0.0/8 subnet.
As such this creates by default a route with a metric of 0, which directs all traffic in direction of 10.0.0.0/8 through the physical interface that is connected to that network, as you may observe in the 2nd row of the following table :
As 10.100.10.0/27 is included within 10.0.0.0/8, this rule (2nd row) takes precedence over my tunnel static route (3rd row), and therefore, the traffic that should be tunneled is routed through the physical interface (10.255.2.62), and never find it's proper destination.
In concrete terms, a local device that is behind the firewall would be unable to contact a remote host in the 10.100.10.0/27 network (10.100.10.15), because of this metric issue.
I am aware this is keen to a design problem in the infrastructure, but I am just wondering how to engineer a solution to make such communication possible, a solution that doesn't involve changing existing addresses.
Kindly yours
Please note you are posting a public message where community members and experts can provide assistance. Sharing private information such as serial numbers or company information is not recommended.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-09-2023 05:36 AM
Try to change metric of second route to 10.
As /24 mask is more specific then this routing logic should work without issues.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-09-2023 06:03 AM
Hey,
Would love to do just that, however that route is not static, it got added by the PA automatically after assigning an address to the corresponding interface.
I am investigating the CLI as it seems impossible to edit in the UI.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-09-2023 06:06 AM
Policy Based Forwarding is checked before routing table.
If you have PBF to send 10.100.10.0/27 into the tunnel then virtual router is not checked for IPs in that subnet.
Palo Alto Networks certified from 2011
- 3622 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!