- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Site to site tunnel routing issue
- LIVEcommunity
- Discussions
- General Topics
- Site to site tunnel routing issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-08-2020 11:44 AM
I have 2 ISP. My site to site VPN is configured at on 1/10 (ISP A).I want to move my all vpn to other isp1/9(ISPB). Once i change is interface from ike gateway and add the virtual route toward (ISP B) tunnel is up but traffic is not passing through tunnel.when i ping from my PC toward destination ip traffic is still passing via (ISP A). When i check the route i found that destination ip goes from both virtual route old and NEW VR. As i have given my all traffic from inside route like 0.0.0.0--> ISP A NEXT hop. So i have configure the PBF for destination ip but still traffic passing via default IP address for ISP A. Is it behavior of paloalto please suggest.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-08-2020 12:35 PM
PBF doesn't work for anything originating/terminating on the firewall itself. You'll need to pass the traffic to your new VR through your route table and setup proper routing.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-08-2020 12:35 PM
PBF doesn't work for anything originating/terminating on the firewall itself. You'll need to pass the traffic to your new VR through your route table and setup proper routing.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-08-2020 12:58 PM
thanks for reply
As my First VR configure like this 0.0.0.0/0 traffic toward ISP 1 nexthop.interface 1/10 (matric 10)
and back link configure like my NEW VR like 0.0.0.0/0 traffic toward ISP 2 NEXT hop interface 1/9 (matric 10)
As i have remove the tunnel route from FIrst VR and configure to New VR. When i see the traffic now traffic is passing from both VR.
Here Tunnel 105 is configured on interface 1/9
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2020 01:24 AM
Hi @Joshan_Lakhani,
As I understood: two ISPs, two VRs. After you moved IKE Gateway from interface connecting to ISP A to interface connecting to ISP B the VPN Tunnel is "up" (SAs between peers are successfully negotiated) however traffic FROM your internal network TO remote network "behind" the VPN Tunnel is not passing through to the remote site.
I assume the Virtual Router "VR ADSL1 Internet VPN and LAN" (from the screenshot you provided) is the one to which "my PC" from your first post is connected to.
The beauty in design of Virtual Routers is that they are separated. Every one has its own routing table. Routing lookup you are doing are per-VR, not device-level. Traffic from your PC will "arrive" and use the routes present in the "VR ADSL1 Internet VPN and LAN"; as there is no specific route for the network behind the VPN route toward ISP, the default one, will be used to forward those packets.
You have to "push" the packets from "VR ADSL1 Internet VPN and LAN" to "VR for New ADSL" and from there - to the tunnel. Easiest solution to do so would be to add static route in the "VR ADSL1 Internet VPN and LAN" to
192.168.12.17/32 (or whatever the remote network behind tunnel is) with Next Hop - Next VR "VR for New ADSL".
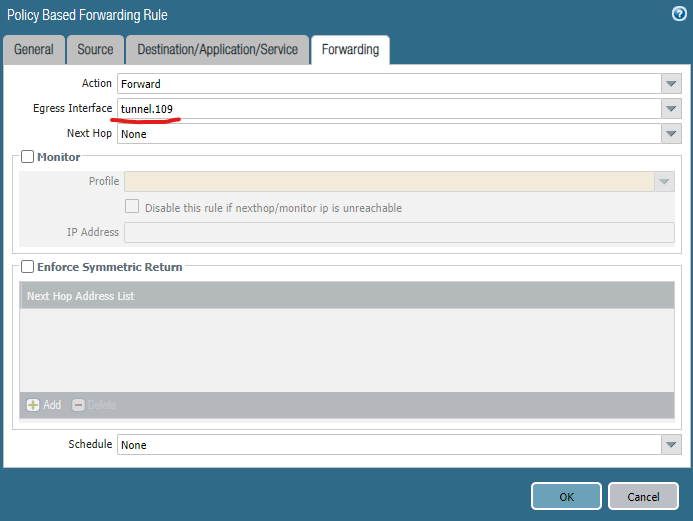
PBF you mentioned is also an option - you would have to define a PBF Rule for Destination 192.168.12.17/32 (or whatever the remote network behind tunnel is) with egress interface tunnel.105 (basing on your screenshot).
I must mention that egress interface used in PBF Rule must have an IP address (does not matter what address, it is not actively used, any valid will do).
Personally I like to create three VRs for such a setup - one per ISP and one for Internal LAN then do traffic steering with PBF or static routes, where needed.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2020 03:34 AM
thanks for reply
As i have configure two separate VR. One for ADSL Link and one for DHCP ISP. As i have add the static route for 192.168.12.17 towards DHCP(192.168.0.1) link in new VR but site traffic is passing from both VR. we have also changed the Matrices of the tunnel as well as for 1/9(ISPB) for a specific route but still the same.Traffic is passing from ADSL due to default route is configured on ADSL So, all the interface as well internet traffic is passing via ISP1 A.we have configure PBF for ISPB is this link is DHCP as the next hop is changed so we have configure as none, but still passing from ADSL Link.Please suggest
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2020 04:06 AM
I think you misunderstood me.
If "192.168.12.17" is the IP address behind the VPN tunnel, traffic inside the tunnel, not the IKE Peer (looks that way) then you have to direct it into the tunnel interface assigned to the tunnel (tunnel.109, I presume).
You have to direct the traffic to be tunneled through the VPN Tunnel into the tunnel interface or it will not be, err..., tunneled.
"As i have add the static route for 192.168.12.17 towards DHCP(192.168.0.1) link" - this is an error, will not work.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2020 06:15 AM
thanks for you reply
As i found this KB
PBF does not function for IPSec Tunnel traffic to the Palo Alto Networks firewall.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClbDCAS
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2020 06:32 AM
"PBF does not function for IPSec Tunnel traffic to the Palo Alto Networks firewall." - yes, but from what you wrote thus far it seems that it is not relevant to your situation because you are working on passing traffic from/through Palo Alto Networks firewall.
Also in mentioned KB:
"The PBF will only work for the traffic sourced from a machine behind the firewall and not for the traffic sourced from the firewall.".
Maybe a drawing of the topology...?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2020 12:41 PM
Hello,
I prefer to use 1 VR and OSPF to trade route information. If I have two paths, I just weigh the less desirable one heavier so its not used unless the other one is not available.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2020 01:46 PM
In the 1 VR environment you lose a bit from the dual-ISP setup - precisely tying the PA-originating packets to the interface-ISP pair.
My most-loved is the 3 VRs setup with EBGP - most control and granularity, especially if VPN is setup with 3-rd Party 😉
- 1 accepted solution
- 12363 Views
- 9 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- PAN-308564 Known Issue in Advanced SD-WAN for NGFW Discussions
- return traffic being dropped, not being sent through the vpn tunnel in General Topics
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- Palo Alto Global Protect clients failing to connect intermittently in GlobalProtect Discussions