- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Site-to-site VPN with Strongswan (opensource)
- LIVEcommunity
- Discussions
- General Topics
- Site-to-site VPN with Strongswan (opensource)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Site-to-site VPN with Strongswan (opensource)
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-23-2014 12:53 PM
Hi all,
I wonder whether anyone has successfully configured site-to-site IPSec VPN tunnel with CalAmp LTE Fusion device (a cellular mobile router). Somehow I cannot establish the vpn tunnel under different configurations and I know it is running opensource strongswan. Interestingly, CalAmp has an older model Vanguard 3000 for 3G and the vpn tunnel works fine. Any advice will be invaluable.
Thanks!!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-23-2014 01:54 PM
Hello Sir,
Have you got a chance to take a pcap on this, from that pcap, we will come to know whether the point of failure in phase-1 or in Phase-2 negotiation.
You can verify the same from the PAN system logs as well.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-17-2019 11:55 AM
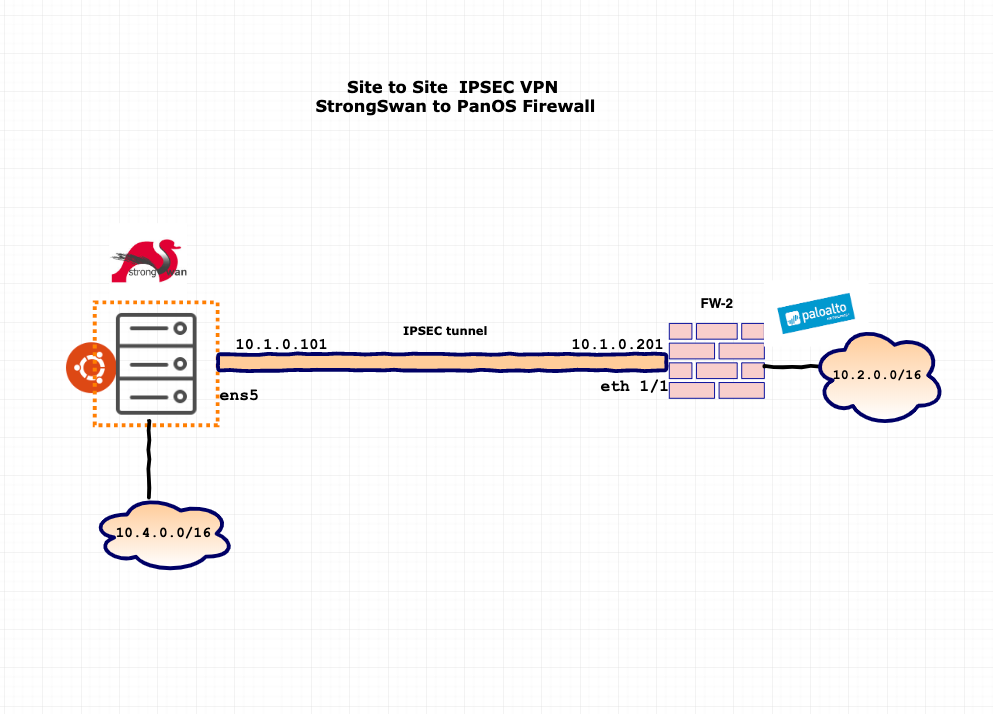
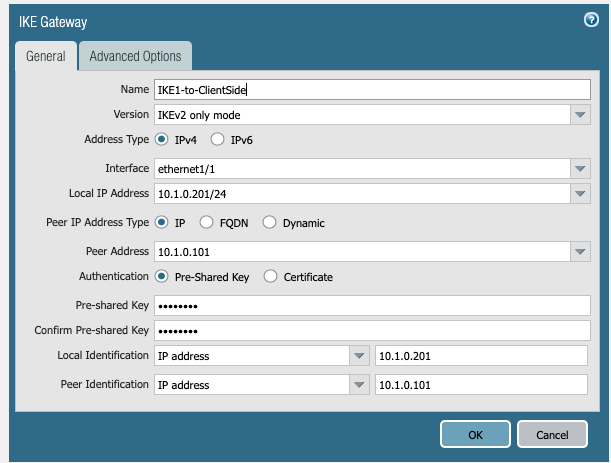
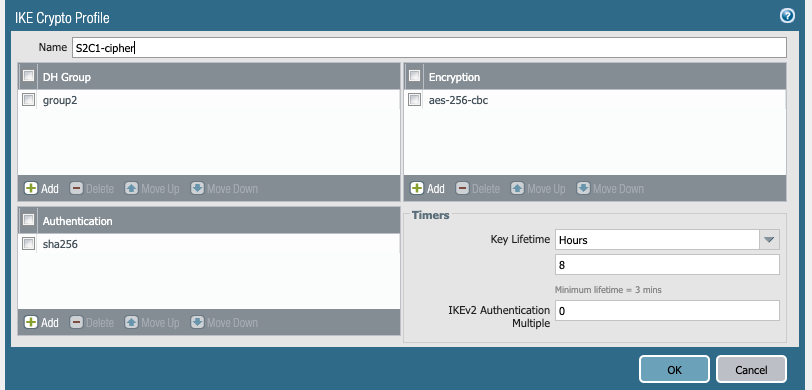
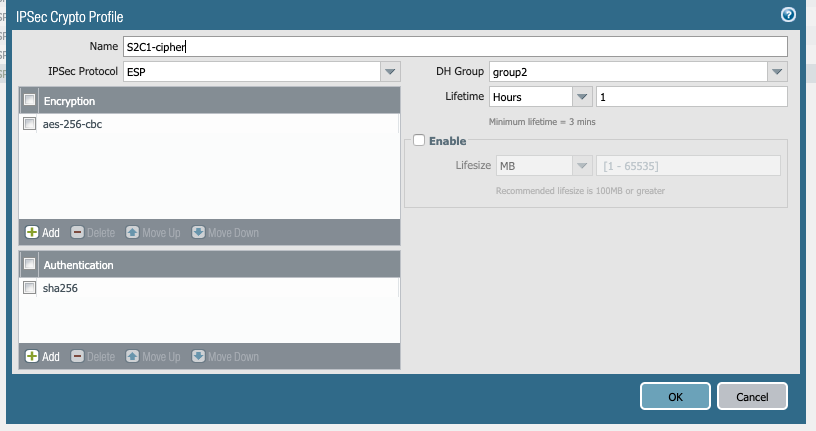
Step1 : Server side Config :
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 | sudo apt update && sudo apt upgrade -y sudo apt-get install strongswan Set the following kernel parameters: cat >> /etc/sysctl.conf << EOF net.ipv4.ipforward = 1 net.ipv4.conf.all.acceptredirects = 0 net.ipv4.conf.all.send_redirects = 0 EOF sysctl -p /etc/sysctl.conf vi /etc/ipsec.conf vi /etc/ipsec.secrets |
vi /etc/ipsec.conf
root@rithvik-gpcs-client-1:/home/rithvik# cat /etc/ipsec.conf # ipsec.conf - strongSwan IPsec configuration file # basic configuration #config setup # strictcrlpolicy=yes # uniqueids = no # Add connections here. # Sample VPN connections #conn sample-self-signed # leftsubnet=10.1.0.0/16 # leftcert=selfCert.der # leftsendcert=never # right=192.168.0.2 # rightsubnet=10.2.0.0/16 # rightcert=peerCert.der # auto=start #conn sample-with-ca-cert # leftsubnet=10.1.0.0/16 # leftcert=myCert.pem # right=192.168.0.2 # rightsubnet=10.2.0.0/16 # rightid="C=CH, O=Linux strongSwan CN=peer name" # auto=start # # # config setup charondebug="all" uniqueids=yes strictcrlpolicy=no conn %default # connection to paris datacenter conn ubuntu-client-to-firewall # leftid=10.1.0.101 leftsubnet=10.1.0.0/16 right=10.1.0.201 rightsubnet=10.1.0.0/16 ike=aes256-sha2_256-modp1024! esp=aes256-sha2_256! keyingtries=0 ikelifetime=1h lifetime=8h dpddelay=30 dpdtimeout=120 dpdaction=restart authby=secret auto=start keyexchange=ikev2 type=tunnel root@rithvik-gpcs-client-1:/home/rithvik# |
vi /etc/ipsec.secrets
root@rithvik-gpcs-client-1:/home/rithvik# cat /etc/ipsec.secrets # This file holds shared secrets or RSA private keys for authentication. # RSA private key for this host, authenticating it to any other host # which knows the public part. 10.1.0.101 10.1.0.201 : PSK '123456' #PSK "123456" root@rithvik-gpcs-client-1:/home/rithvik# |
- 15857 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!




