- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
SSL Decryption for Chrome Browser
- LIVEcommunity
- Discussions
- General Topics
- SSL Decryption for Chrome Browser
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
SSL Decryption for Chrome Browser
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-13-2017 09:41 PM
Hello,
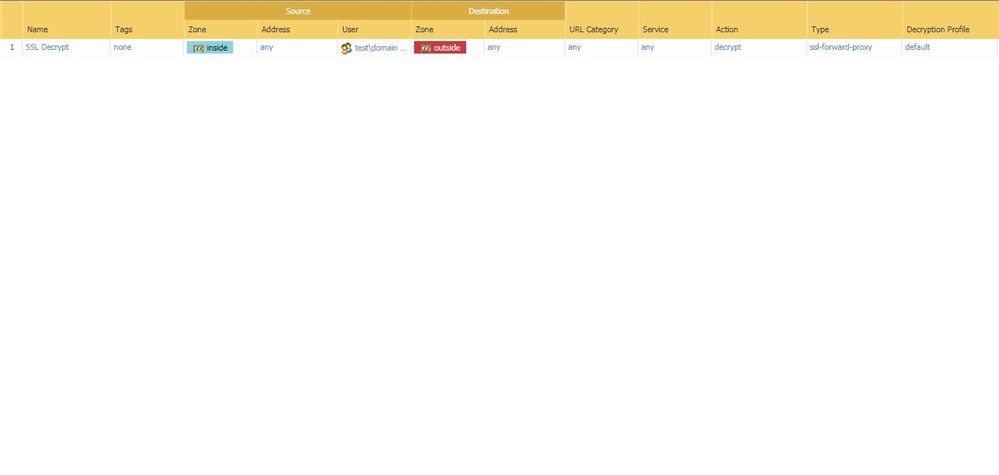
Below is our Decryption Policy. Using latest Chrome version.
Security certificate used by the Palo is from the Windows domain PKI and is already implicitly trusted as this testing is from a domain connected Windows 10 device over Ethernet.
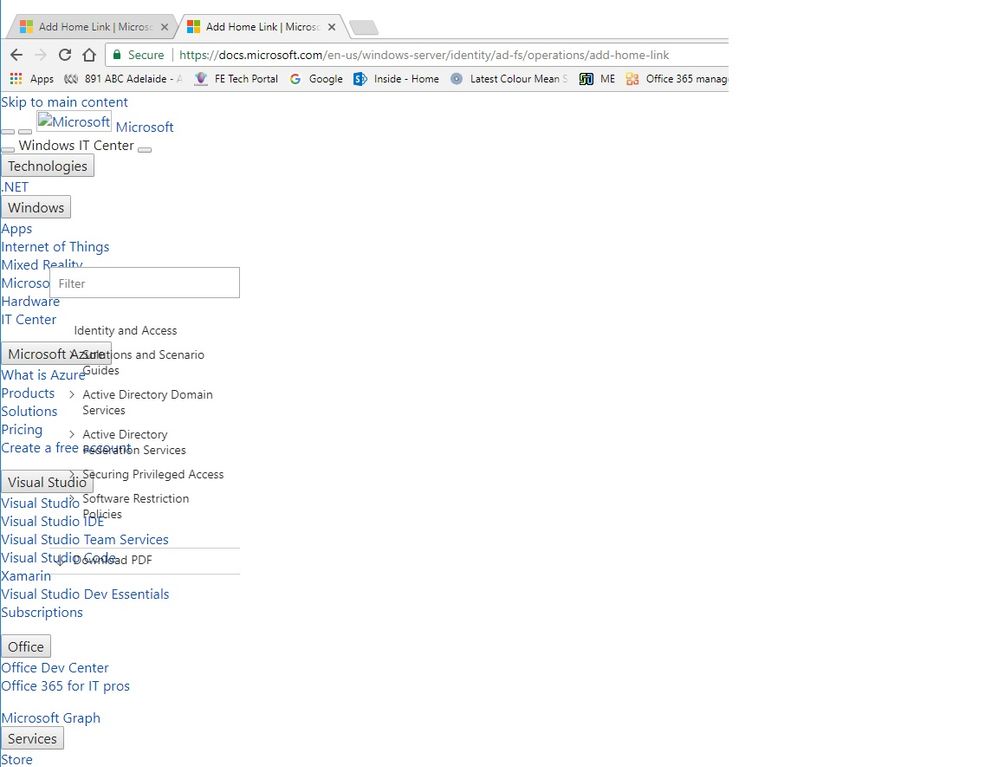
It is working fine for IE but in Chrome it is showing like this:
If I set the URL Category of Computers and Internet information to no-decrypt the error stops for this web site but continues for others, including the main Palo support pages.
Any idea how to stop this?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 01:10 AM
Hi,
Are you getting any decrypt-error end reason in traffic logs?
Can you use the service in the Security Rule as 'any' (in case you are using application-default).
Also you may block quic application as its mainly used by Chrome.
Regards,
Sharief
Sharief
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-25-2017 03:48 PM
Thanks M.
We noticed that if the certificate used for forward proxy SSL is not SHA 256 then the Google Chrome browser will not behave. Our Windows PKI is still producing SHA 1 certificates and would need to be updated to be of any use for issuing these certs to the Palo.
Once the SHA 256 cert generated from the Palo is imported to the test PC’s then Google Chrome immediately sees it in the store and is happy to use this for SSL inspection. A SHA1 cert from our Windows PKI does not show up in Chrome and is ignored for SSL decryption, which was the start of this issue.
It would seem that Google is on the fast track to make SHA 1 a bit of history, while IE11 is still happy to use SHA1 for security.
- 3678 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma browser extension for Google Chrome does not auto or force sign in in Prisma Access Agent Discussions
- Submit false positive in VirusTotal
- web file blocking in Next-Generation Firewall Discussions
- Panorama managed - Global protect SAML cert renew - IDP xml import wrong expiry in GlobalProtect Discussions
- Cannot add Links between Tasks - messed up in browser. in Cortex XSOAR Discussions