- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Suspicious DNS Query list
- LIVEcommunity
- Discussions
- General Topics
- Re: Suspicious DNS Query list
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-15-2014 02:06 PM
Hello,
Is there a list of all the DNS Querys that PA considers suspicious?
I was considering changing the default action from alert to block for these signatures.
Since there is potentially 1 million URLs that will automatically get blocked when adjusted, my client might want to go over the list before making the decision.
Thanks!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-15-2014 02:24 PM
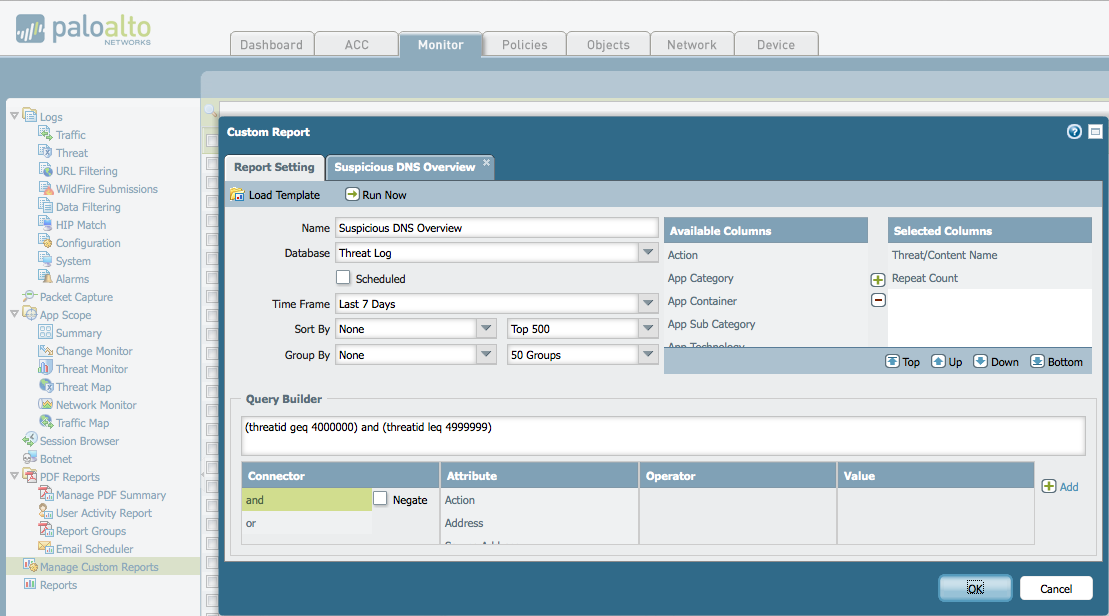
That list is a "living database" and changes over time. I think a better method to use with your customer would be to understand "what would have been blocked". You can run a simple custom report to answer that question. Use the "Threat Log" as your data source and use the following options (feel free to change your timeframe - just keep in mind the longer the timeframe the longer the report may take to run. Start small ~1 day and then work your way up).
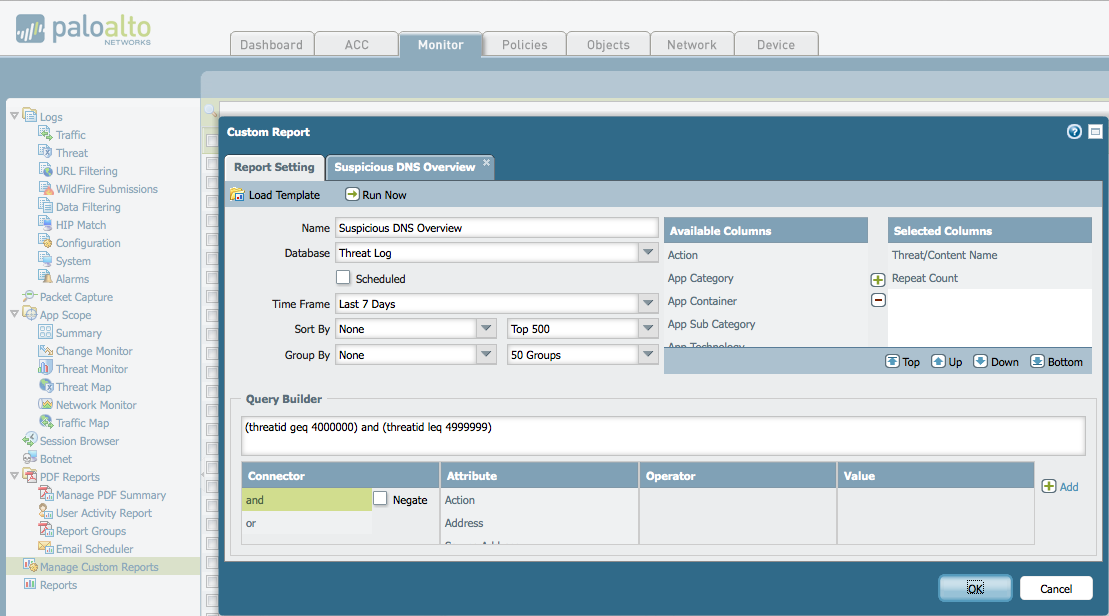
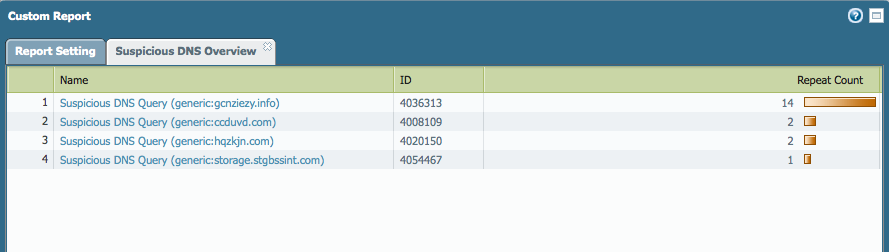
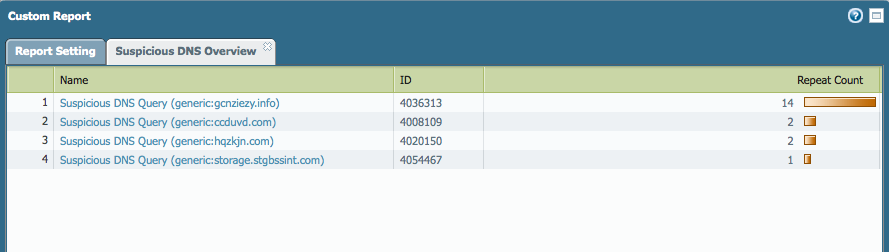
In my small lab environment, the output looks like this:
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-15-2014 02:24 PM
That list is a "living database" and changes over time. I think a better method to use with your customer would be to understand "what would have been blocked". You can run a simple custom report to answer that question. Use the "Threat Log" as your data source and use the following options (feel free to change your timeframe - just keep in mind the longer the timeframe the longer the report may take to run. Start small ~1 day and then work your way up).
In my small lab environment, the output looks like this:
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-15-2014 05:17 PM
I agree with Jared. Even if you could see the whole database, and the chances are low that PA would allow that. I'm sure they consider those contents a trade secret they want to keep from the competition, the report is more relevant.
The report tells you what your users are likely to see on your network.
Remember also that generally when a default action is to alert instead of block, there is a much higher possibility of a false positive. So you may generate some work allowing blocked sites after the action is changed.
ACE PanOS 6; ACE PanOS 7; ASE 3.0; PSE 7.0 Foundations & Associate in Platform; Cyber Security; Data Center
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2014 07:40 AM
Thanks for your replies.
- 1 accepted solution
- 3966 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- Help me on developing XQL Query in Cortex XDR Discussions
- Assistance with LDAP Authentication in General Topics
- XQL query to get a list of current applications installed on hosts in Cortex XDR Discussions
- How to escape a wildcard (*) in Cortex XDR Discussions




