- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
TLS 1.3 is Coming - How to deal with it????
- LIVEcommunity
- Discussions
- General Topics
- Re: TLS 1.3 is Coming - How to deal with it????
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-28-2018 07:30 AM
My security counter parts came to me letting me know that in Chrome version 70.X+ TLS 1.3 will be turned on by default. This appears to be causing problems in our current firewall deployment:
A/P HA-par 5220s running 8.0.10 (soon to be 8.0.12).
It looks like Google has released an article describing what's going on:
https://www.chromium.org/Home/tls13
In this article it highlights how Cisco FirePower devices can be configured to avoid issue. Does anyone know how to correct this in Palo?
Here is the error the users get (TLS1.3 Downgrade detected)
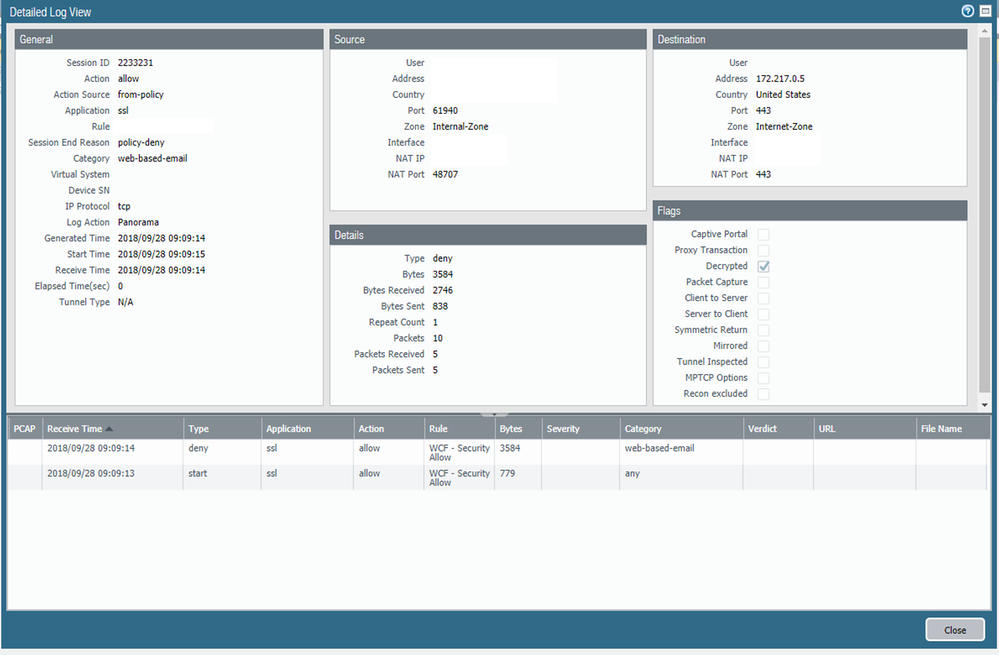
This is the traffic log for the user traffic. "Webmail" access is allowed, and we're doing SSL decryption.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2018 09:32 AM
Hello All,
The link to the google groups article fixes the issue as it tells Chrome to disable the 1.3 variant.
Just paste the following into the chrome browser address field and it should bring it up, then change the setting to 'Disabled'. You will have to restart your browser.
chrome://flags/#tls13-variant
Cheers!
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2018 09:49 AM
Desabling the 1.3 variant works on my PC, but i'm not sure how I would go about deploying this workaround.
I don't have the option to disable 1.3 variant in my Chrome GPO, at least by that name.
Any ideas in that regard?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2018 12:00 PM
Update on this issue:
"We are aware of two vendors whose products have this bug: Cisco and Palo Alto Networks, although there may be more. We reported the issue to Cisco in December 2017. They released the fix this past August and have published an advisory. Palo Alto Networks recently discovered the issue on their devices and are planning to release PAN-OS 8.1.4, PAN-OS 8.0.14, and PAN-OS 7.1.21 to fix this, tentatively by Nov 30th."
Full link:
https://www.ietf.org/mail-archive/web/tls/current/msg27066.html
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2018 04:14 AM
I updated our firmware last night to 8.1.4 and the issue has gone away
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2018 08:34 AM
This message was sent to Palo Alto Networks customers:
Dear valued Palo Alto Networks customer,
Please take the action recommended below if you have enabled SSL decryption forward proxy. This is required for users to access Gmail and other websites and applications using web browsers that implement strict TLS 1.3 compliance. We have been informed that Google Chrome is planning to implement strict TLS 1.3 compliance in their upcoming version 72. The stable build of Google Chrome version 72 may be available in January 2019, and if your users use a pre-stable build of Google Chrome, they will experience the issue outlined below earlier.
Applies to
All supported PAN-OS releases
Action Required
If you run PAN-OS 8.1:
- Upgrade to PAN-OS 8.1.4 (available now)
If you run a prior version of PAN-OS, plan to upgrade to one of the following releases:
- PAN-OS 8.0.14 (targeted to be available on Nov 15, 2018*)
- PAN-OS 7.1.21 (targeted to be available on Nov 1, 2018*)
Impact
Without upgrading to one of the above maintenance releases, users may no longer be able access Gmail and other websites and applications that utilize TLS 1.3 when SSL forward proxy decryption is in use. As a result, your users will receive the following web browser error: ‘ERR_TLS13_DOWNGRADE_DETECTED’.
By upgrading PAN-OS to one of the above maintenance releases, your users will be able to continue to access Gmail and other TLS 1.3 enabled websites and applications when using browsers that exhibit this behavior.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2018 09:24 AM
@bspilde wrote:PAN-OS 8.0.14 and 8.1.4 will support TLS 1.3.
Thanks for following up.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2018 09:26 AM
@bspilde Where / How did you recieve this info below?
@bspilde wrote:This message was sent to Palo Alto Networks customers:
Dear valued Palo Alto Networks customer,
Please take the action recommended below if you have enabled SSL decryption forward proxy. This is required for users to access Gmail and other websites and applications using web browsers that implement strict TLS 1.3 compliance. We have been informed that Google Chrome is planning to implement strict TLS 1.3 compliance in their upcoming version 72. The stable build of Google Chrome version 72 may be available in January 2019, and if your users use a pre-stable build of Google Chrome, they will experience the issue outlined below earlier.
Applies to
All supported PAN-OS releases
Action Required
If you run PAN-OS 8.1:
- Upgrade to PAN-OS 8.1.4 (available now)
If you run a prior version of PAN-OS, plan to upgrade to one of the following releases:
- PAN-OS 8.0.14 (targeted to be available on Nov 15, 2018*)
- PAN-OS 7.1.21 (targeted to be available on Nov 1, 2018*)
Impact
Without upgrading to one of the above maintenance releases, users may no longer be able access Gmail and other websites and applications that utilize TLS 1.3 when SSL forward proxy decryption is in use. As a result, your users will receive the following web browser error: ‘ERR_TLS13_DOWNGRADE_DETECTED’.
By upgrading PAN-OS to one of the above maintenance releases, your users will be able to continue to access Gmail and other TLS 1.3 enabled websites and applications when using browsers that exhibit this behavior.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-04-2018 10:05 AM
On the support page check preferences under your profile for all communication preferences by type.
Hope that helps!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-14-2019 10:31 AM
This issue had disappeared for us after upgrading our firewalls (now at 8.1.5). However, as of this morning (on Chrome 71.0.3578.98 and possibly older versions), it has reappeared for at least two URLs:
https://www.yegjoyride.com/volunteer-1
The first one is happy in Firefox; however, the second one has a similar error in Firefox. No errors occur from our guest network, which has no decryption.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-14-2019 12:04 PM
Those URL's/categories are being decrypted?
- 30157 Views
- 25 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Dead Space in Cortex XDR Discussions
- Cortex XDR - Issues auto-grouping under same case due to shared IP - how to manage? in Cortex XDR Discussions
- cyvrlpc.sys failure in Cortex XDR Discussions
- Portal/Gateway certificate renewals - automation? in GlobalProtect Discussions
- Continuous Threat Logs Showing Management Server IP as Source in Next-Generation Firewall Discussions