- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Global Protect pre-logon then on-demand configuration
- LIVEcommunity
- Discussions
- Network Security
- GlobalProtect Discussions
- Re: Global Protect pre-logon then on-demand configuration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-23-2021 12:31 PM - edited 06-25-2021 06:39 AM
We're using these versions (Yes, we need to upgrade, but other priorities at the moment)
PANos 8.1.14
Global Protect client 5.2.1
We're currently usingOn-Demand, which is working. We used this page with the only difference is we're using AD Authentication.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClH2CAK
Now we want to use pre-logon then on-demand.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA14u000000oM4ACAU
We used our internal PKI to create machine certs and those have been deployed using Group Policy.
What I'm not getting is how to configure GlobalProtect to use the machine cert for pre-logon.
Do I create a new SSL/TLS profile or certificate profile?
Can I use the PANos self-signed in conjunction with the PKI machine cert? Would the self-signed be for the portal and the machine cert be for the gateway?
I've gone through all the documents, as well as, the GP Admin guide.
Any advice or guidance is much appreciated!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2021 04:22 AM
yes I am using the same cert profile for portal and gateway.
I have a copy of our AD CA on the palo and this is in a certificate profile.
we have templates within AD to generate user certs which GP (group policy) puts in users personal store and other templates to generate machine certs which GP puts into the machine personal store.
we have approx 8k users with different setups but we have one small campus that uses a simple config with the above cert use.
It has 1 portal with 2 agent configs.
first one has pre-logon in the selection criteria and the second has any user in the selection criteria. the app settings for both vary slightly but both set to pre-logon, always on... but will be much the same for on demand...
both portal configs point to the same gateway, the gateway only has 1 config for all users... screen shots to follow...
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-23-2021 04:07 PM
We use our Windows CA, installed the machine cert for the CA and then added the CA as a trusted root certificate server and it works great.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-23-2021 10:27 PM
We use the same as @CobaltixIT and works fine. You can use a mix of pki and self signed as long as you list both root CA’s in the cert profile but cant see the benefit of mixing here...
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2021 04:03 AM
Thank you both. I know I have myself confused with this. And now a few more questions.
Are you using solely your internal PKI for the portal and gateway? And @Mick_Ball are you using the Cert profile for both portal and gateway?
Thank you both again. I'll get out of the weeds soon...
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2021 04:22 AM
yes I am using the same cert profile for portal and gateway.
I have a copy of our AD CA on the palo and this is in a certificate profile.
we have templates within AD to generate user certs which GP (group policy) puts in users personal store and other templates to generate machine certs which GP puts into the machine personal store.
we have approx 8k users with different setups but we have one small campus that uses a simple config with the above cert use.
It has 1 portal with 2 agent configs.
first one has pre-logon in the selection criteria and the second has any user in the selection criteria. the app settings for both vary slightly but both set to pre-logon, always on... but will be much the same for on demand...
both portal configs point to the same gateway, the gateway only has 1 config for all users... screen shots to follow...
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2021 04:43 AM
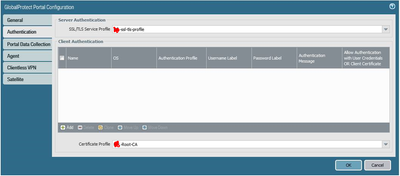
Portal Auth
Portal configs
Gateway Auth
Gateway conf
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2021 04:49 AM
And your SSL/TLS profile points to your CA?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2021 11:09 AM
Yes but not the same CA used for authentication.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-01-2021 11:02 AM
Just a followup. I switched to using a wilcard cert for the portal and internal PKI with machine certs for pre-logon. I've passed this hurdle and now just need to resolve the cookie issue I'm having with pre-login.
Thanks for your help!
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-01-2021 01:32 PM
Hope y'all are well.
Thank you both for your help. In the end we stood up an MS NPS server for RADIUS.
Now the portal has the wildcard.domain.com cert and the gateway has an internal PKI certificate. When a computer is joined to the domain they are issued a cert from our PKI. Then using RADIUS to authenticate Pre-Logon then Demand is working and users can change their password before logging in.
Since the company is allowing BYOD for remote users I have to configure GP to allow a non-domain computer to authenticate. (BYOD may change soon, but in the meantime...)
- 1 accepted solution
- 11782 Views
- 9 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Windows 11 Global Protect App not booting at login screen for Prelogon Solution in GlobalProtect Discussions
- GP - Pre-Login in GlobalProtect Discussions
- GlobalProtect Client Certificate Authentication Issues in GlobalProtect Discussions
- Best Practices for Global Protect Machine and User Cert Authentication in GlobalProtect Discussions
- Global Protect Always On VPN Pre-Logon in GlobalProtect Discussions