- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
- LIVEcommunity
- Community Legacy Content
- PSIRT Articles
- Who rated this article
Who rated this article
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 12-27-2017 11:56 AM - edited on 11-01-2019 10:14 AM by Retired Member
Background
ROBOT [1] is an attack that affects the TLS RSA key exchange and could lead to decryption of captured sessions if the TLS server originally serving said captured session is still alive, vulnerable and using the same private key.
Exposure
SSL Decryption and GlobalProtect are susceptible to this issue. Our engineers are working on a software fix. We recommend customers running PAN-OS to upgrade to a fixed version of software or use content update 757, and implement further mitigations through the configuration changes described below under “Mitigations”. PAN-OS impacted releases include 6.1.19 and prior, 7.1.14 and prior, 8.0.6-h3 and prior.
Fix and Mitigations
Software update
PAN-OS 6.1.20 and newer, 7.1.15 and newer, and 8.0.7 and newer are fixed. Customers exposed to this vulnerability are invited to upgrade to a corrected version of PAN-OS.
Content Update
Palo Alto Networks has released content update 757, which includes a vulnerability signature (“TLS Network Security Protocol Information Disclosure Vulnerability – ROBOT”, #38407) that can be used as an interim mitigation to protect PAN-OS devices until the software is upgraded. For complete protection, signature #38407 must be applied upstream from any interfaces implementing SSL Decryption, or hosting a GlobalProtect portal or a GlobalProtect gateway.
SSL Decryption Mitigation
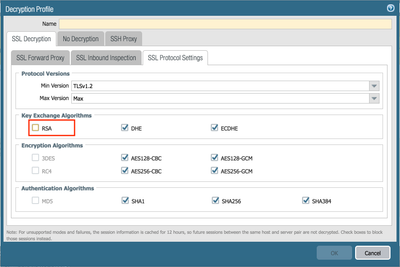
Customers running PAN-OS 7.1 or later can configure their SSL Decryption profiles to disable RSA.
GlobalProtect Mitigation
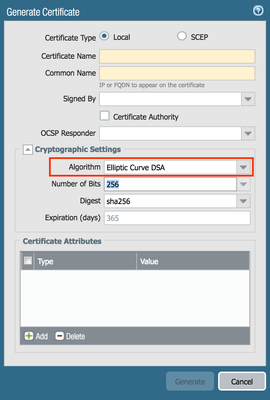
If the GlobalProtect server certificate is using RSA, customers running PAN-OS 7.1 or later can opt to replace this certificate with one implementing the Eliptic Curve DSA algorithm as a safer alternative.
Note: A PAN-OS 7.1 known issue prevents properly formatted ECDSA CSR. As a result, the Global Protect ECDSA certificate could either be generated:
- on appliance by temporarily importing the enterprise Certificate Authority in PAN-OS; or
- on external enterprise PKI system then imported into PAN-OS along with its private key.
See Also
PAN-OS Technical Documentation
Critical Issues Addressed In PAN-OS Releases
Best Practices For PAN-OS Upgrade
Reference