- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Nominated Discussion: Configure a second DUO for PA firewall MFA
- LIVEcommunity
- Articles
- General Articles
- Nominated Discussion: Configure a second DUO for PA firewall MFA
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
This Nominated Discussion Article is based on the post "Configure second DUO for PA firewall MFA " by @boblin and responded to by @Raido_Rattameister , @TomYoung , @BPry. Read on to see the discussion and solution! Make sure to check out the document @boblin created and linked at the bottom to assist other users !
We have configured a DUO Proxy server for PA firewall MFA and it works. We also configured the second DUO proxy server for redundancy. However, we don't know how to configure PA firewall to fail-over to the second DUO in a case the primary DUO proxy server is down. Any help?
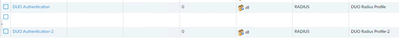
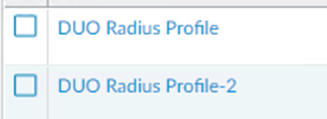
You need to add auth sequence under "Device > Authentication Sequence"
Add both RADIUS profiles there. Configure GlobalProtect auth to use previously configured sequence.
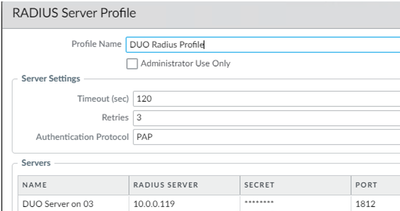
Check how many retries and timeout your RADIUS profiles have configured under "Device > Server Profiles > RADIUS".
Let's assume that you have 2 attempts with 20 seconds timeout.
This leaves 20 seconds for secondary RADIUS server as GlobalProtect will time out in 60 seconds by default.
You might want to extend GP timeout.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PMD5CAO
Is it possible to configure active/active or balance? If so how to do it?
The easiest way to configure redundancy for the same protocol is to add multiple servers in the RADIUS Server Profile. However, this will not load balance. The NGFW will try each one from the top down. https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClqECAS
I have configured the second DUO proxy server, but it doesn't work. To troubleshooting, what would you do? Perhaps, where I can check the logs?
I find authproxy.log and it shows:
2023-04-26T15:56:36.843265-0500 [duoauthproxy.lib.log#info] Duo Security Authentication Proxy 5.7.4 - Init Complete
2023-04-26T16:08:57.409802-0500 [-] (UDP Port 1812 Closed)
2023-04-26T16:08:57.409802-0500 [-] Stopping protocol <duoauthproxy.lib.forward_serv.DuoForwardServer object at 0x0000028A1FE91E80>
2023-04-26T16:08:57.409802-0500 [-] Main loop terminated.
2023-04-26T16:09:05.780813-0500 [-] DuoForwardServer starting on 1812
2023-04-26T16:09:05.780813-0500 [-] Starting protocol <duoauthproxy.lib.forward_serv.DuoForwardServer object at 0x0000021AA5B81CA0>
2023-04-26T16:09:05.876008-0500 [duoauthproxy.lib.log#info] FIPS mode is not enabled
2023-04-26T16:09:05.876008-0500 [duoauthproxy.lib.log#info] Reactor in use: <twisted.internet.selectreactor.SelectReactor object at 0x0000021AA32785E0>
2023-04-26T16:09:05.876008-0500 [duoauthproxy.lib.log#info] AD Client Module Configuration:
2023-04-26T16:09:05.876008-0500 [duoauthproxy.lib.log#info] {'host': '10.0.0.58',
To troubleshoot:
Can you authenticate to the secondary RADIUS server that you created separate from the authentication sequence that you configured (create a temporary Authentication Profile with just the new config if needed)?
Via the CLI you can do this with the 'test authentication authentication-profile <profilename> username <username> password' command to verify that it just isn't an issue on that secondary node.
You can auto review the authd log file by using 'less mp-log authd.log' on the CLI as well.
The second DUO Proxy server configuration is correct and works if I don't use authentication sequence. For example, the first duo proxy IP is 10.0.0.119
in RADIUS Server profile, if you change the IP to second DUO proxy 10.0.0.183, it works.
If in Authentication Profile, I have two profiles.
and authentication sequence has two profiles.
Only DUO Profile works. If I stop the first duo proxy server, it doesn't work.
How do you run 'test authentication authentication-profile'? I keep getting Invalid syntax.
Based on your screenshot, you have a 120 seconds timeout. That is an eternity!
For failover to ever happen it would take 3x120 seconds.
GlobalProtect will wait only 60 seconds by default until it times out.
I have two DUO profile in the authentication sequency and it works. However, it seems to me this is active/passive. How can we setup active/active or balance?
Active/Active can be only set if RADIUS profile points to NAT policy in Palo and this NAT policy has dynamic destination IP with session distribution. But it will not check if destination is live or not. DNAT is just round robin or least session etc basis.
There's no other way to set active/active.
Utilizing NAT with session distribution is kind of a hack that you can use if you really need active/active.
Here's a step by step guide (full credits to the author @boblin for making this):
Configure two duo proxy servers for Palo alto firewall MFA redundancy
- 3501 Views
- 0 comments
- 0 Likes
- Custom Signatures With ChatGPT and AI Security in General Articles
- Nominated Discussion: Configure Split Tunneling by Domain in General Articles
- Nominated Discussion - Sorting Question in General Articles
- Nominated Discussion: Using the REST API to Create a Bunch of Address Objects in General Articles
- A Guide to NAT on Palo Alto Networks Firewalls in Support FAQ
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
ADNS
1 -
Advanced DNS Security
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
2 -
AI Security
1 -
AI Threat
1 -
AIOPS
1 -
Analytics
1 -
Ansible
2 -
antivirus
1 -
API
2 -
API & SDK
1 -
App-ID
1 -
applications
2 -
APS
1 -
Artificial Intelligence
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
6 -
AWS
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
7 -
Block List
1 -
Cardinality
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CI CD Integration
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud ngfw
1 -
Cloud security
2 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Configuration
8 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Container
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
Cortex XSOAR
2 -
CPSP
1 -
Custom Signatures
3 -
custom-featured-post
1 -
cyber elite
1 -
cyberelite
13 -
Cybersecurity
1 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
DLP
1 -
Docker
2 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
End to End Encryption
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
3 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
GKE
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
4 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
HyperLogLog
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector Design
2 -
Log Management
1 -
Logging
1 -
login
1 -
Logs
3 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
Network Security
35 -
Network Security Management
1 -
Network-Security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
31 -
NGFW Configuration
12 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Prisma Access
1 -
Panorama
12 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
7 -
Prisma AIRS
1 -
Prisma SASE
2 -
Prisma SD-WAN
1 -
proactive insights
2 -
Prompt Poaching
1 -
Public Cloud
1 -
Python
2 -
Radius
1 -
Ransomware
1 -
RBI
2 -
region
1 -
Registration
1 -
Remote Browser Isolation
3 -
Reporting
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Site-to-Site VPN
1 -
Software Firewalls
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
2 -
Strata Logging Service (SLS)
1 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Terraform
3 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
7 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
Upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
8 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WhatsApp
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next