- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to block the real IPs from CDN?
- LIVEcommunity
- Discussions
- General Topics
- How to block the real IPs from CDN?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How to block the real IPs from CDN?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2014 08:55 PM
Is there any function that can makes the PA block the traffic of the real IP instead of CDN IPs?
We deployed the PA NGFW on the external side of our web server and enabled the Threat Prevention function. Because we are using the CDN, so from the web server, all the source IPs in the traffic are hosted by the CDN service provider.
So when the PA NGFW blocks the source IP addresses because of the attack behavior, is there any way to block the real IPs of the attackers nor the IPs hosted by the CDN provider?
Thanks!
- Labels:
-
Configuration
-
Content-ID
-
Networking
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2014 07:55 AM
Thanks for reply, rmonvon.
Yes, we have asked our CDN provider to pass the real IP addresses in the packet header.
Do you have any idea?![]()
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2014 08:44 AM
Are they embedding the IP address in the TCP option 28 header or HTTP 'x-forwarded-for' header or another header?
If they are using the TCP option 28 header, I suggest you contact your local Palo Alto Nwks' SE and submit a feature request.
If they are using the HTTP 'x-forwarded-for' header, the PA can log the header so you can correlate the logs to determine the real IP of the intruder. From there, you can write a custom threat signature to match the real IP and block this new custom threat. This is a manual process though.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2014 09:43 AM
Thanks for your reply.
They are embedding the IP address in the HTTP 'x-forwarded-for' header.
Can the blocking function be automatical?
For example, if the attacker is launching a DOS attack, can PA only block or quarantine the real IP nor the CDN IP?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2014 09:58 AM
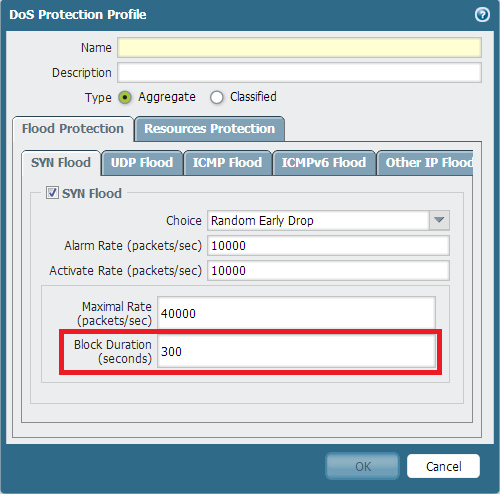
For example, if I enable syn flood prevetion, will the PA FW quarantine the real IPs or CDN IP? Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-27-2014 10:17 AM
The default behavior of the PA will take action on the source IP address, and in this case this would be the CDN's IP address. At this time, the PA cannot take action on the IP address in the HTTP 'x-forwarded-for' header. Please contact your local Palo Alto Nwks' SE and submit a feature request. You can turn on logging for HTTP 'x-forwarded-for' header:
- 6843 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Introducing the Strata Cloud Manager (SCM) Terraform Provider: Automate and Scale Your Network Security in Strata Cloud Manager
- How to request review of residual High-Risk rating when category dispute has been resolved? in General Topics
- Palo Alto Networks Training and Student Engagement Opportunities in General Topics
- Default certificate TLSv1.3_Default in General Topics
- Is there an API to add IPs to Cortex XDR EDL programmatically? in Cortex XDR Discussions




