- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
IKE Certificate Authentication Peer ID
- LIVEcommunity
- Discussions
- General Topics
- IKE Certificate Authentication Peer ID
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
IKE Certificate Authentication Peer ID
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2020 07:23 AM
Hi,
Im trying to setup a VPN connection using certificate based authentication. When Phase 1 tries to establish I'm getting the following error
Peer's ID payload ' IPv4_address:xxx.xxx.xxx.xxx' does not match certificate ID, Error: failed to get subjectAltName.
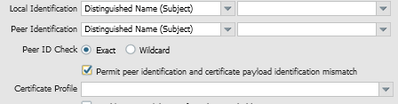
I have added the peer's IP address to the IP(SAN) of the certificate and also tried using 'Permit peer identification and certificate payload identification mismatch' with no luck.
Any further suggestions on how to bring up phase 1?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2020 02:04 PM
The error seems to suggest that either A. The other side is sending a local identification that does not match any SAN that is present on the certificate or B. Does not contain a SAN attribute on the certificate at all.
Are both sides under your control, where you're able to generate a new certificate if need be or inspect the current attributes of the certificate it's using?
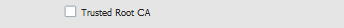
Also make sure the Certificate Profile on the VPN contains the Intermediate, Root or Self Signed certificate and is marked as a Trusted certificate in the local device store.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 12:39 AM
Hi,
I can generate a new certificate if required.
The issue is that it's looking for the peer id which is an IP address in the SAN. I have added this into the cert and verified its there in the SAN but it still doesn't not get picked up during the phase 1 verification - would it be work adding another san entry like hostname and adding the IP address?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 01:24 AM
If you can generate a new certificate it would defiantly be worth generating a new one containing additional SAN entries.
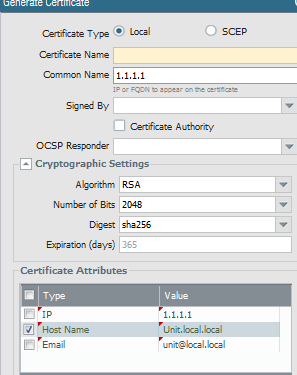
I'd suggest tagging on the SANs Hostname, FQDN and IP address and check if you can get the firewall to recognize these attributes as the Peer Identification.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 06:35 AM
New certificate didn't do the trick. PA Support also don't seem to know either 😞
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 07:21 AM
Are you sure you've imported the peers certificate, or signer of the certificate, in the local firewall and added a certificate profile containing this certificate which applies on the VPN?
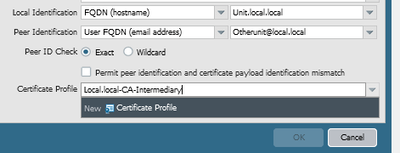
The Peer Identification, local and peer, needs to match on both sides (Reverse local/Remote) and the Cert Profile, if containing the cert marked as trusted, should set up the Phase 1 connection.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 07:30 AM
Ok to go through the motions..
I generated a CSR using my public IP as the CN
I sent my CSR to the peer who signed it and sent back their Root, Int CA's and my signed cert
I imported all 3
In the IKE setup I set the Cert to be the signed cert
I created a cert profile adding both CA's
I then set Local Identification to be my DN record of the Cert (as this populate this way)
I then set the Peer Identification to be their IP
If I change the IP to be something else it fails before the authentication saying the Peer ID they presented didnt match.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 08:00 AM
Gotcha, just to clarify did you also designate SAN attributes for your firewall cert and for the cert the other firewall is using?
Like:
The additional attributes are SAN items which seem related to the error where no additional attributes were found.
It would end up local something similar to the below screenshot if he other side has a certificate with Email Otherunit@local.local.
Lastly the intermediate and/or root need to be marked in the certificate store as trusted CA's
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 08:04 AM
I tried setting the SAN for IP to be that of the remote peer.
Im in the process of waiting for a new cert to be signed where the SAN IP is set to the local peer ip as you show in your screenshots.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 08:09 AM
Sorry yes, I have also set these to trusted.
If i set anything other than the IP address in the Peer Identification field i get the following error
received ID_R (type ipaddr [xxx.xxx.xxx.xxx]) does not match peer ID
So if i set it back to the IP i then get the cert error
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 08:13 AM
That would mean the Peer firewall is sending it's IP address as Local Identifier, however the question is if this is also defined on the certificate the Peer is using as that needs to match aswell.
So the Peers Certificate would need a SAN Attribute "IP Address" with it's IP.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-11-2020 08:47 AM
I've posed the question to my peer.
I added this IP as a SAN entry in my CSR but as far as their side im not sure.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-12-2020 06:25 AM
Taking the original error and picking it piece by piece.
Peer's ID payload ' IPv4_address:xxx.xxx.xxx.xxx' does not match certificate ID, Error: failed to get subjectAltName.
It would seem that their side does have their Local ID Field and IP Field are filled with an IP address however the certificate they use doesn't seem to have a SAN at all, or a matching IP address SAN on the certificate.
Looking at the last bit my guestimate would be the second case.
Next step would be to verify if this is actually the case by either having them check the config or make a PCAP of the initial exchange to capture the certificate info (Depending on the Ike version and mode of connection (Main/aggressive)).
- 11951 Views
- 12 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- Is It Possible to Distribute Client Certificates to iOS Devices Using GlobalProtect SCEP Without MDM? in General Topics
- SAML authentication with cookies won´t work in General Topics
- Palo Alto Global Protect clients failing to connect intermittently in GlobalProtect Discussions