- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
NAT Security rule
- LIVEcommunity
- Discussions
- General Topics
- NAT Security rule
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2018 04:03 PM
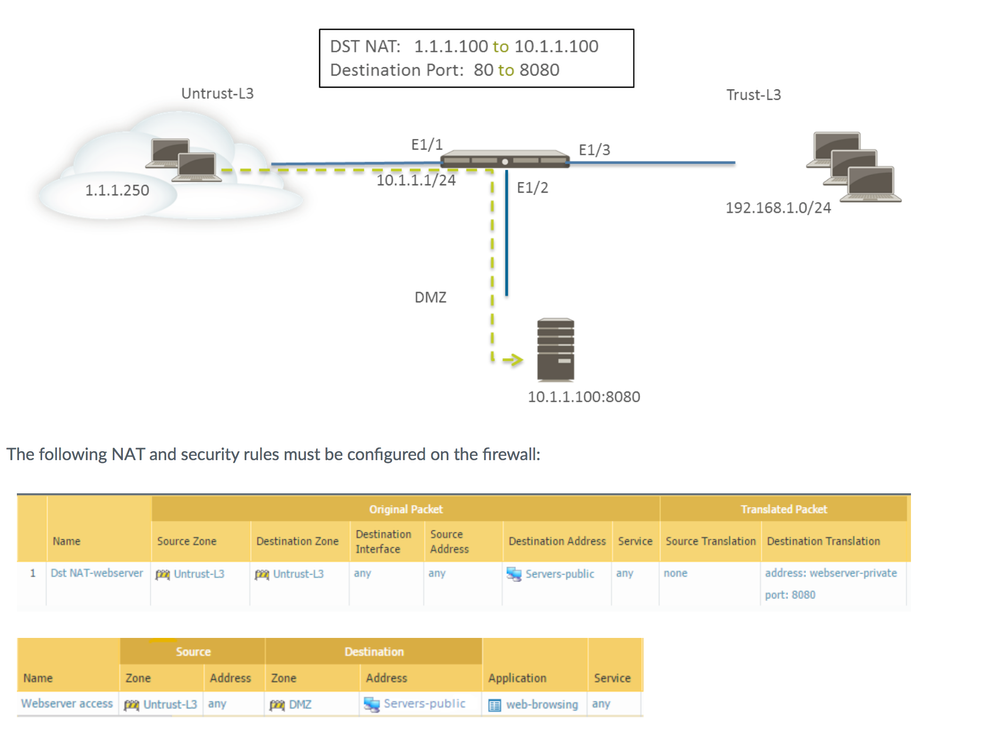
I'm used to working on Cisco ASA and I'm having a hard time understanding why the security rule states Untrust-L3 for both the source and destination zone. Typically wouldn't that be Untrust-L3 to DMZ? Is there a specific reason for this behavior?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-08-2018 01:56 AM
Hi @Glitchen
When a new packet arrives on an interface, the firewall needs to determine it's source and destination zones, these are determined by using the routing table.
So when a packet arrives from the internet, both it's source as destination IPs will be located in the untrust zone: they both follow the default gateway when performing a route lookup
(eg. packet from 193.51.100.1 to 203.0.113.1, both ip will resolve via 0.0.0.0/0 to the untrust zone)
Next, the NAT policy is checked to see if this packet matches something, and if it does, which zone the final destination is located in, this is where, post translation, it is deterined that security wise the (final) destination is dmz (eg. 203.0.113.1 translates to 10.0.0.1, which is routed to the dmz interface).
The next step is to verify the security policy for matches to see if the packet is going to be allowed or not. Since we now know the final destination is DMZ, you can build a security policy to allow from untrust to dmz
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-08-2018 12:56 AM
Hi @Glitchen,
This is by design.
Check out the following articles that can be very helpful on this topic :
https://live.paloaltonetworks.com/t5/Learning-Articles/Packet-Flow-Sequence-in-PAN-OS/ta-p/56081
Cheers !
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-08-2018 01:56 AM
Hi @Glitchen
When a new packet arrives on an interface, the firewall needs to determine it's source and destination zones, these are determined by using the routing table.
So when a packet arrives from the internet, both it's source as destination IPs will be located in the untrust zone: they both follow the default gateway when performing a route lookup
(eg. packet from 193.51.100.1 to 203.0.113.1, both ip will resolve via 0.0.0.0/0 to the untrust zone)
Next, the NAT policy is checked to see if this packet matches something, and if it does, which zone the final destination is located in, this is where, post translation, it is deterined that security wise the (final) destination is dmz (eg. 203.0.113.1 translates to 10.0.0.1, which is routed to the dmz interface).
The next step is to verify the security policy for matches to see if the packet is going to be allowed or not. Since we now know the final destination is DMZ, you can build a security policy to allow from untrust to dmz
PANgurus - Strata & Prisma Access specialist
- 1 accepted solution
- 2890 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- XSIAM - Data Patterns in General Topics
- Quarantined Files not appearing in Action Center in Cortex XDR Discussions
- Palo Alto Networks Certified Security Professional in General Topics
- Enforce GlobalProtect Access Based on Microsoft Intune Compliance Status in GlobalProtect Discussions
- Palo Alto 820 - Software Update for CVE-2026-0300 in Next-Generation Firewall Discussions