- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
OKTA SAML panorama authentication?
- LIVEcommunity
- Discussions
- General Topics
- OKTA SAML panorama authentication?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
OKTA SAML panorama authentication?
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-16-2021 08:01 AM - edited 02-16-2021 08:06 AM
Trying to get this working and I am able to authenticate using OKTA SAML via the button on the login screen but when I do (after entering u/p on the OKTA page) it redirects me back to the Panorama login page. I see PAN_AUTH_SCUESS SAML on the CLI but never an 'auth-sucess' in the GUI (Monitor > Logs ? System) because it never actually logs me in. The only thing I see in the GUI when attempting to login via SAML is a saml_client_redirect for that SAML profile when I attempt to use it.
Does anyone have Admin SAML logins to panorama working and if so any idea what is going on here? I dont use GP or captive-portal and I only want this working with admin logins. This is the document I followed: https://saml-doc.okta.com/SAML_Docs/How-to-Configure-SAML-2.0-for-Palo-Alto-Networks-Admin-UI.html
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-17-2021 04:40 AM
SAML will work with web gui based logins, as we use it for authentication to our lab/demo equipment, as we mock up different configurations.
If I understood your comment, you see the SAML redirect (in the webpage) but does not go any further. If you are seeing this, then SAML may not be configured correctly or there is some other message.
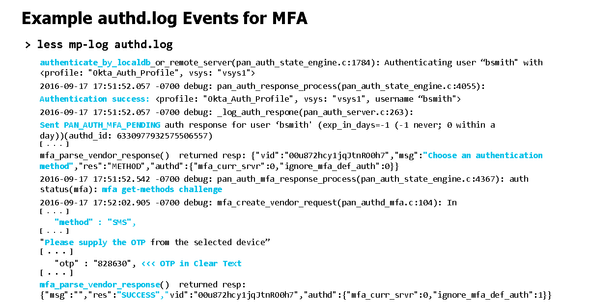
My recommendation for you to do, is to get into CLI and run the below commands and then follow an authentication attempt for your user:
one command could be
test mfa-vendors mfa-server-profile <profile name>
another command you could run also is
tail follow yes mp-log authd.log
You would be looking for something like this...
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-17-2021 06:09 AM
I see the redirect page, I login using my SAML u/p and then it redirects me back to the panorama login screen. I have done all those commands and have a case open with support who were less than helpful so I figured I would ask here.
For instance I test that SAML profile from the CLI and it spits out the test URL: https://<panIP>:443/SAML20/SP/TEST which when pasting into a browser opens up an OKTA authentication window, I login and it says 'signing into the Palo Alto Networks UI' or something along those lines and its back to the login screen. So authentication works it just doesn't work to actually login to panorama.
From the logs I see PAN_AUTH_SUCCESS SAML response and redirects but again it just doesn't log me in. I would copy/paste the output but not really sure what is considered sensitive in those logs.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-17-2021 10:32 AM
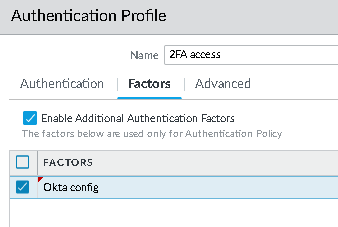
Have you considered trying to use 2FA for authentication vs exlcusively SAML?
For example... we use LDAP as our first factor, and then Okta as our 2nd factor.
We authenticate first to the Panorama using , then put in Okta creds, with the popup window and then I can log in.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-18-2021 05:59 AM - edited 02-18-2021 06:00 AM
No because I wanted to get SAML working first but DUO MFA is on the roadmap once we got SAML working.
Either way it shouldn't matter what number of authentication methods I choose it should still log me into the panorama. Whether I am using, local, LDAP, OKTA, SAML is irrelevant as those are simply authentication methods. LDAP and local works, SAML does not.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-18-2021 09:57 AM
Log in to the Panorama that manages Prisma Access and configure the SAML signing certificate that you want to use with SAML 2.0. ... Configure SAML Authentication for Prisma Access Using Okta With the Prisma Access App Select. Device. ... Click. Generate. ... Select the certificate, then click. ... Export the certificate in PEM format.
- 6305 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GP with saml authentication always redirects to idp in General Topics
- [SOLVED] Panorama's SAML-Based Administrator Cannot See Other Administrators And Generate TSFs in Panorama Discussions
- SAML authentication with cookies won´t work in General Topics
- cloud identity engine and Entra ID certificate warning in Cloud Identity Engine Discussions
- New cert GP cert prompt for people testing Yubikeys for windows logon in GlobalProtect Discussions