- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
palo alto interrupting web server traffic
- LIVEcommunity
- Discussions
- General Topics
- palo alto interrupting web server traffic
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
palo alto interrupting web server traffic
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-06-2017 11:09 AM
Hi,
I have web server , in some computers website load properly and some not loading properly .
I suspect pa is interrupting
Please advise
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-06-2017 11:32 AM - edited 03-07-2017 07:35 AM
Hi @sib2017
What is actually happening? How is your policy looks like (profiles) etc. Traffic logs for the affected users? What I am usually doing (not always possible in the production) is taking one of the affected users/PCs and creating a "clear" test policy without anything purely from source to the destination permit any any (no profiles) and see what is happening. Same issue? Removing test policy and checking the client-server side only :0 as this is not PA issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-06-2017 02:40 PM - edited 03-06-2017 02:41 PM
your issue is very vague. if you are talking about the same website on multiple computers, the first thing to check is to see if each computer is hitting the same rule for the same website in the traffic log. if so, you should also look at the reason for the session end, if it's a tcp-fin or timed out or a reset of some sort. also consider the threat log if you have a threat prevention policy in place. you also need to consider if all computers are using the same browser/version.
there are many places something like this could go wrong, but unless your rules are applied subjectively/unevenly, the firewall is probably the least likely source of the issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 07:30 AM
Hi,
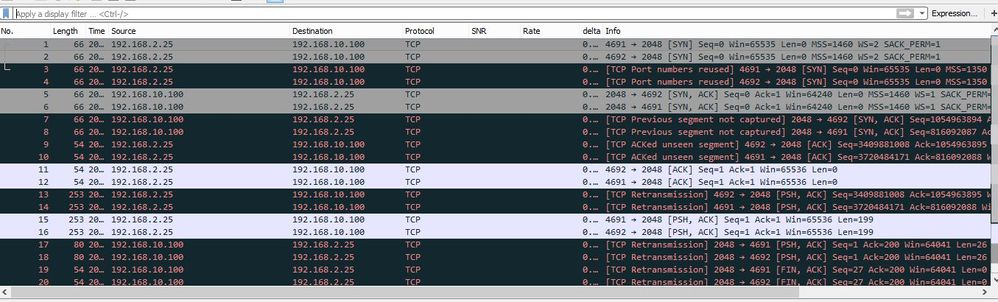
The server is 192.168.10.100:2048
and the client is : 192.168.2.25
Here is the capture -rx from the pa
Sometimes can access the port 2048 .That is the syptom. sometimes cannot .
In my capture there are tcp port numbers resued ,multiple retransmsiion and tcp previous segment not captured .
These are indicating to any problems
Thank you
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 07:35 AM - edited 03-07-2017 07:36 AM
What can you see in the traffic logs when accessing this server? How the PA identifies this port TCP 2048 under which application? How is your security policy looks like?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 09:56 AM
Hi,
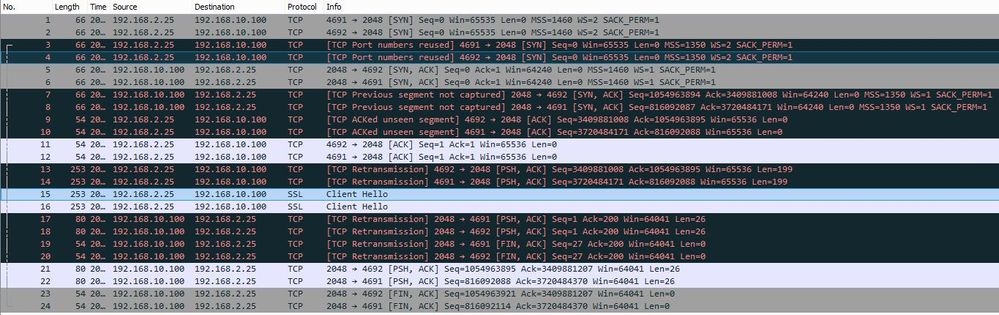
As per the screenshot there is SYN-ACK and corresponding (5 and 6) and finally client sent an ACK (11 and 12)
so the server listening on port 2048 , is'nt it ?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 10:06 AM
A couple things could help clear it up if you can repost the screenshot:
- Remove or hide the SNR and Rate columns in Wireshark.
- Reduce the sizes of the IP columns to expand the other columns that have "..." so we can see the full data.
- I assume the "delta" column is delta time between displayed frames, but expanding that field could help (or change your time display format to "Seconds since previous displayed packet".
- Grab a packet capture of a working client to compare the flow.
It looks like we see two sets of three-way handshakes here, both on destination port 2048. Both handshakes are complete, and there seems to be an exchange of data (client sends PSH flags on frames 11-12, 13-14, and 15-16; the server sends a reply in frames 17-18).
If the traffic is known to Wireshark, you can also decode it as the known traffic (if it's TLS for example, right-click on any frame and choose Decode As..., and specify port 2048 to be whatever the actual traffic is).
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 11:28 AM
Hi gwesson
Thank you for the reply .
I have adjusted the view as you said . And i did decode as 'ssl'
Sorry for the incenvenience
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 11:39 AM - edited 03-07-2017 01:07 PM
Hi,
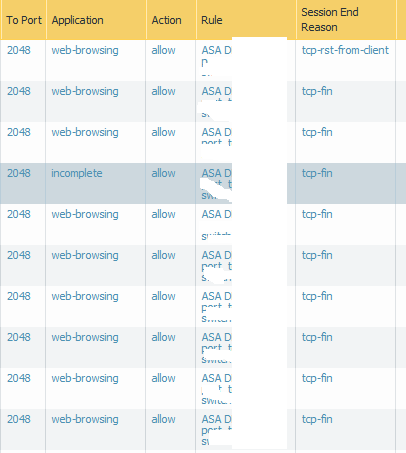
Yes, correct. The server is listening on TCP 2048 port (no doubt) but same time we can see SSL traffic to the same server. But what l am trying to understand is how is the PA seeing this traffic and how it is identifying? Under which application. This all info is under Monitoring tab on PA.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 01:02 PM
@TranceforLife is bringing up a really good point. If the only information that your giving is a wireshark it doesn't actually tell us what the Palo Alto itself is seeing. Knowing what your security policy for the traffic looks like, how the Palo Alto is seeing the termination, all of that other good information.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-07-2017 11:21 PM
Hi,
Unfortunately i Changed this port from 2048 to 80 and all the logs were over written .
When i change the app to port 80 , its seems working fine .There is some few old logs (Rules are same )
And there are some records shows session end reason is unknown
Thanks
- 8107 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- return traffic being dropped, not being sent through the vpn tunnel in General Topics
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- Global Protect Internal Detection in GlobalProtect Discussions
- Config/System Logs Not Forwarding to Syslog Server in Next-Generation Firewall Discussions
- Palo Alto Networks PA- 450 Next‑Generation Firewall to maintain uninterrupted BSNL SIP trunk services in the event of a primary internet link failure. in Next-Generation Firewall Discussions